Master header file for Tor-specific functionality. More...
#include "orconfig.h"#include "torint.h"#include "crypto.h"#include "crypto_format.h"#include "tortls.h"#include "torlog.h"#include "container.h"#include "compress.h"#include "address.h"#include "compat_libevent.h"#include "ht.h"#include "confline.h"#include "replaycache.h"#include "crypto_curve25519.h"#include "crypto_ed25519.h"#include "tor_queue.h"#include "token_bucket.h"#include "util_format.h"#include "hs_circuitmap.h"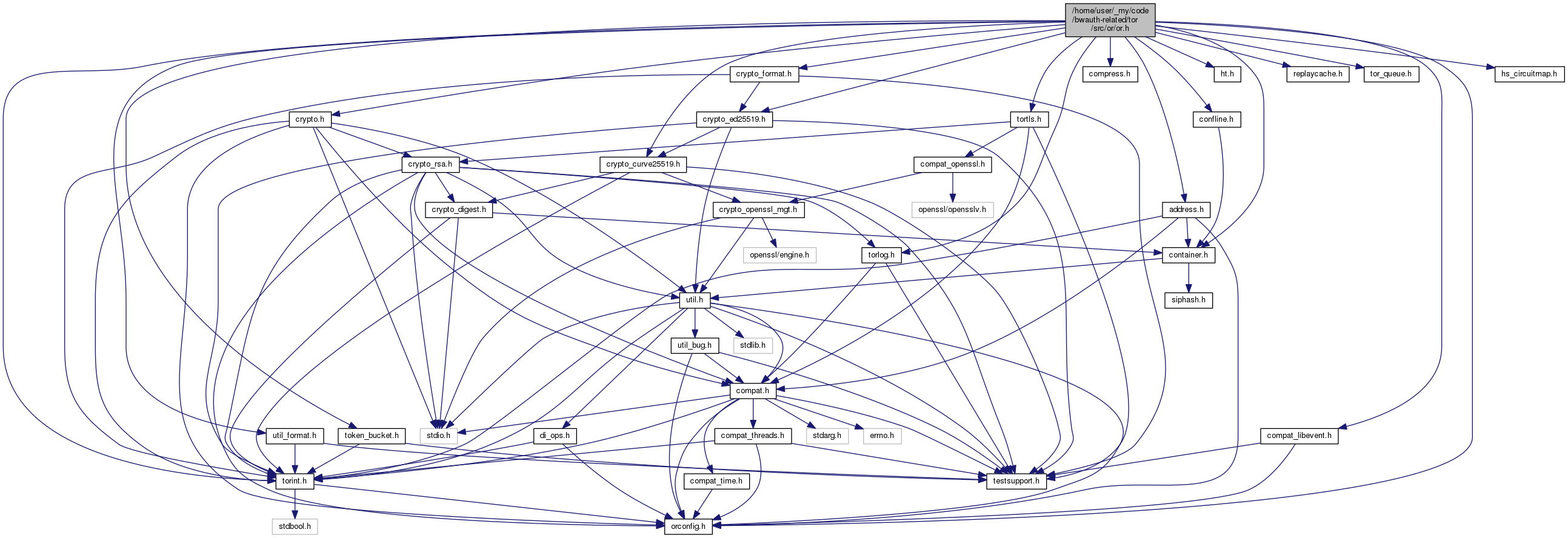
Go to the source code of this file.
Macros | |
| #define | SIGHUP 1 |
| #define | SIGINT 2 |
| #define | SIGUSR1 10 |
| #define | SIGUSR2 12 |
| #define | SIGTERM 15 |
| #define | SIGNEWNYM 129 |
| #define | SIGCLEARDNSCACHE 130 |
| #define | SIGHEARTBEAT 131 |
| #define | DOWNCAST(to, ptr) ((to*)SUBTYPE_P(ptr, to, base_)) |
| #define | MAX_NICKNAME_LEN 19 |
| #define | MAX_HEX_NICKNAME_LEN (HEX_DIGEST_LEN+1) |
| #define | MAX_VERBOSE_NICKNAME_LEN (1+HEX_DIGEST_LEN+1+MAX_NICKNAME_LEN) |
| #define | MAX_BUF_SIZE ((1<<24)-1) /* 16MB-1 */ |
| #define | MAX_DIR_DL_SIZE MAX_BUF_SIZE |
| #define | MAX_HEADERS_SIZE 50000 |
| #define | MAX_DIR_UL_SIZE MAX_BUF_SIZE |
| #define | MAX_DESCRIPTOR_UPLOAD_SIZE 20000 |
| #define | MAX_EXTRAINFO_UPLOAD_SIZE 50000 |
| #define | MIN_ONION_KEY_LIFETIME_DAYS (1) |
| #define | MAX_ONION_KEY_LIFETIME_DAYS (90) |
| #define | DEFAULT_ONION_KEY_LIFETIME_DAYS (28) |
| #define | MIN_ONION_KEY_GRACE_PERIOD_DAYS (1) |
| #define | DEFAULT_ONION_KEY_GRACE_PERIOD_DAYS (7) |
| #define | ONION_KEY_CONSENSUS_CHECK_INTERVAL (60*60) |
| #define | MAX_SSL_KEY_LIFETIME_INTERNAL (2*60*60) |
| #define | ROUTER_MAX_AGE (60*60*48) |
| #define | ROUTER_MAX_AGE_TO_PUBLISH (60*60*24) |
| #define | OLD_ROUTER_DESC_MAX_AGE (60*60*24*5) |
| #define | circ_id_type_bitfield_t ENUM_BF(circ_id_type_t) |
| #define | CONN_TYPE_MIN_ 3 |
| #define | CONN_TYPE_OR_LISTENER 3 |
| #define | CONN_TYPE_OR 4 |
| #define | CONN_TYPE_EXIT 5 |
| #define | CONN_TYPE_AP_LISTENER 6 |
| #define | CONN_TYPE_AP 7 |
| #define | CONN_TYPE_DIR_LISTENER 8 |
| #define | CONN_TYPE_DIR 9 |
| #define | CONN_TYPE_CONTROL_LISTENER 11 |
| #define | CONN_TYPE_CONTROL 12 |
| #define | CONN_TYPE_AP_TRANS_LISTENER 13 |
| #define | CONN_TYPE_AP_NATD_LISTENER 14 |
| #define | CONN_TYPE_AP_DNS_LISTENER 15 |
| #define | CONN_TYPE_EXT_OR 16 |
| #define | CONN_TYPE_EXT_OR_LISTENER 17 |
| #define | CONN_TYPE_AP_HTTP_CONNECT_LISTENER 18 |
| #define | CONN_TYPE_MAX_ 19 |
| #define | PROXY_NONE 0 |
| #define | PROXY_CONNECT 1 |
| #define | PROXY_SOCKS4 2 |
| #define | PROXY_SOCKS5 3 |
| #define | PROXY_PLUGGABLE 4 |
| #define | PROXY_INFANT 1 |
| #define | PROXY_HTTPS_WANT_CONNECT_OK 2 |
| #define | PROXY_SOCKS4_WANT_CONNECT_OK 3 |
| #define | PROXY_SOCKS5_WANT_AUTH_METHOD_NONE 4 |
| #define | PROXY_SOCKS5_WANT_AUTH_METHOD_RFC1929 5 |
| #define | PROXY_SOCKS5_WANT_AUTH_RFC1929_OK 6 |
| #define | PROXY_SOCKS5_WANT_CONNECT_OK 7 |
| #define | PROXY_CONNECTED 8 |
| #define | CONN_IS_EDGE(x) ((x)->type == CONN_TYPE_EXIT || (x)->type == CONN_TYPE_AP) |
| #define | LISTENER_STATE_READY 0 |
| #define | OR_CONN_STATE_MIN_ 1 |
| #define | OR_CONN_STATE_CONNECTING 1 |
| #define | OR_CONN_STATE_PROXY_HANDSHAKING 2 |
| #define | OR_CONN_STATE_TLS_HANDSHAKING 3 |
| #define | OR_CONN_STATE_TLS_CLIENT_RENEGOTIATING 4 |
| #define | OR_CONN_STATE_TLS_SERVER_RENEGOTIATING 5 |
| #define | OR_CONN_STATE_OR_HANDSHAKING_V2 6 |
| #define | OR_CONN_STATE_OR_HANDSHAKING_V3 7 |
| #define | OR_CONN_STATE_OPEN 8 |
| #define | OR_CONN_STATE_MAX_ 8 |
| #define | EXT_OR_CONN_STATE_MIN_ 1 |
| #define | EXT_OR_CONN_STATE_AUTH_WAIT_AUTH_TYPE 1 |
| #define | EXT_OR_CONN_STATE_AUTH_WAIT_CLIENT_NONCE 2 |
| #define | EXT_OR_CONN_STATE_AUTH_WAIT_CLIENT_HASH 3 |
| #define | EXT_OR_CONN_STATE_AUTH_MAX 3 |
| #define | EXT_OR_CONN_STATE_OPEN 4 |
| #define | EXT_OR_CONN_STATE_FLUSHING 5 |
| #define | EXT_OR_CONN_STATE_MAX_ 5 |
| #define | EXIT_CONN_STATE_MIN_ 1 |
| #define | EXIT_CONN_STATE_RESOLVING 1 |
| #define | EXIT_CONN_STATE_CONNECTING 2 |
| #define | EXIT_CONN_STATE_OPEN 3 |
| #define | EXIT_CONN_STATE_RESOLVEFAILED 4 |
| #define | EXIT_CONN_STATE_MAX_ 4 |
| #define | AP_CONN_STATE_MIN_ 5 |
| #define | AP_CONN_STATE_SOCKS_WAIT 5 |
| #define | AP_CONN_STATE_RENDDESC_WAIT 6 |
| #define | AP_CONN_STATE_CONTROLLER_WAIT 7 |
| #define | AP_CONN_STATE_CIRCUIT_WAIT 8 |
| #define | AP_CONN_STATE_CONNECT_WAIT 9 |
| #define | AP_CONN_STATE_RESOLVE_WAIT 10 |
| #define | AP_CONN_STATE_OPEN 11 |
| #define | AP_CONN_STATE_NATD_WAIT 12 |
| #define | AP_CONN_STATE_HTTP_CONNECT_WAIT 13 |
| #define | AP_CONN_STATE_MAX_ 13 |
| #define | AP_CONN_STATE_IS_UNATTACHED(s) ((s) <= AP_CONN_STATE_CIRCUIT_WAIT || (s) == AP_CONN_STATE_NATD_WAIT) |
| #define | DIR_CONN_STATE_MIN_ 1 |
| #define | DIR_CONN_STATE_CONNECTING 1 |
| #define | DIR_CONN_STATE_CLIENT_SENDING 2 |
| #define | DIR_CONN_STATE_CLIENT_READING 3 |
| #define | DIR_CONN_STATE_CLIENT_FINISHED 4 |
| #define | DIR_CONN_STATE_SERVER_COMMAND_WAIT 5 |
| #define | DIR_CONN_STATE_SERVER_WRITING 6 |
| #define | DIR_CONN_STATE_MAX_ 6 |
| #define | DIR_CONN_IS_SERVER(conn) ((conn)->purpose == DIR_PURPOSE_SERVER) |
| #define | CONTROL_CONN_STATE_MIN_ 1 |
| #define | CONTROL_CONN_STATE_OPEN 1 |
| #define | CONTROL_CONN_STATE_NEEDAUTH 2 |
| #define | CONTROL_CONN_STATE_MAX_ 2 |
| #define | DIR_PURPOSE_MIN_ 4 |
| #define | DIR_PURPOSE_HAS_FETCHED_RENDDESC_V2 4 |
| #define | DIR_PURPOSE_FETCH_SERVERDESC 6 |
| #define | DIR_PURPOSE_FETCH_EXTRAINFO 7 |
| #define | DIR_PURPOSE_UPLOAD_DIR 8 |
| #define | DIR_PURPOSE_UPLOAD_VOTE 10 |
| #define | DIR_PURPOSE_UPLOAD_SIGNATURES 11 |
| #define | DIR_PURPOSE_FETCH_STATUS_VOTE 12 |
| #define | DIR_PURPOSE_FETCH_DETACHED_SIGNATURES 13 |
| #define | DIR_PURPOSE_FETCH_CONSENSUS 14 |
| #define | DIR_PURPOSE_FETCH_CERTIFICATE 15 |
| #define | DIR_PURPOSE_SERVER 16 |
| #define | DIR_PURPOSE_UPLOAD_RENDDESC_V2 17 |
| #define | DIR_PURPOSE_FETCH_RENDDESC_V2 18 |
| #define | DIR_PURPOSE_FETCH_MICRODESC 19 |
| #define | DIR_PURPOSE_UPLOAD_HSDESC 20 |
| #define | DIR_PURPOSE_FETCH_HSDESC 21 |
| #define | DIR_PURPOSE_HAS_FETCHED_HSDESC 22 |
| #define | DIR_PURPOSE_MAX_ 22 |
| #define | DIR_PURPOSE_IS_UPLOAD(p) |
| #define | EXIT_PURPOSE_MIN_ 1 |
| #define | EXIT_PURPOSE_CONNECT 1 |
| #define | EXIT_PURPOSE_RESOLVE 2 |
| #define | EXIT_PURPOSE_MAX_ 2 |
| #define | CIRCUIT_STATE_BUILDING 0 |
| #define | CIRCUIT_STATE_ONIONSKIN_PENDING 1 |
| #define | CIRCUIT_STATE_CHAN_WAIT 2 |
| #define | CIRCUIT_STATE_GUARD_WAIT 3 |
| #define | CIRCUIT_STATE_OPEN 4 |
| #define | CIRCUIT_PURPOSE_MIN_ 1 |
| #define | CIRCUIT_PURPOSE_OR_MIN_ 1 |
| #define | CIRCUIT_PURPOSE_OR 1 |
| #define | CIRCUIT_PURPOSE_INTRO_POINT 2 |
| #define | CIRCUIT_PURPOSE_REND_POINT_WAITING 3 |
| #define | CIRCUIT_PURPOSE_REND_ESTABLISHED 4 |
| #define | CIRCUIT_PURPOSE_OR_MAX_ 4 |
| #define | CIRCUIT_PURPOSE_C_GENERAL 5 |
| #define | CIRCUIT_PURPOSE_C_HS_MIN_ 6 |
| #define | CIRCUIT_PURPOSE_C_INTRODUCING 6 |
| #define | CIRCUIT_PURPOSE_C_INTRODUCE_ACK_WAIT 7 |
| #define | CIRCUIT_PURPOSE_C_INTRODUCE_ACKED 8 |
| #define | CIRCUIT_PURPOSE_C_ESTABLISH_REND 9 |
| #define | CIRCUIT_PURPOSE_C_REND_READY 10 |
| #define | CIRCUIT_PURPOSE_C_REND_READY_INTRO_ACKED 11 |
| #define | CIRCUIT_PURPOSE_C_REND_JOINED 12 |
| #define | CIRCUIT_PURPOSE_C_HSDIR_GET 13 |
| #define | CIRCUIT_PURPOSE_C_HS_MAX_ 13 |
| #define | CIRCUIT_PURPOSE_C_MEASURE_TIMEOUT 14 |
| #define | CIRCUIT_PURPOSE_C_MAX_ 14 |
| #define | CIRCUIT_PURPOSE_S_HS_MIN_ 15 |
| #define | CIRCUIT_PURPOSE_S_ESTABLISH_INTRO 15 |
| #define | CIRCUIT_PURPOSE_S_INTRO 16 |
| #define | CIRCUIT_PURPOSE_S_CONNECT_REND 17 |
| #define | CIRCUIT_PURPOSE_S_REND_JOINED 18 |
| #define | CIRCUIT_PURPOSE_S_HSDIR_POST 19 |
| #define | CIRCUIT_PURPOSE_S_HS_MAX_ 19 |
| #define | CIRCUIT_PURPOSE_TESTING 20 |
| #define | CIRCUIT_PURPOSE_CONTROLLER 21 |
| #define | CIRCUIT_PURPOSE_PATH_BIAS_TESTING 22 |
| #define | CIRCUIT_PURPOSE_HS_VANGUARDS 23 |
| #define | CIRCUIT_PURPOSE_MAX_ 23 |
| #define | CIRCUIT_PURPOSE_UNKNOWN 255 |
| #define | CIRCUIT_PURPOSE_IS_ORIGIN(p) ((p)>CIRCUIT_PURPOSE_OR_MAX_) |
| #define | CIRCUIT_PURPOSE_IS_CLIENT(p) |
| #define | CIRCUIT_IS_ORIGIN(c) (CIRCUIT_PURPOSE_IS_ORIGIN((c)->purpose)) |
| #define | CIRCUIT_PURPOSE_IS_ESTABLISHED_REND(p) |
| #define | CIRCUIT_IS_ORCIRC(c) (((circuit_t *)(c))->magic == OR_CIRCUIT_MAGIC) |
| #define | CIRCUIT_PURPOSE_COUNTS_TOWARDS_MAXPENDING(p) |
| #define | MIN_CIRCUITS_HANDLING_STREAM 2 |
| #define | RELAY_COMMAND_BEGIN 1 |
| #define | RELAY_COMMAND_DATA 2 |
| #define | RELAY_COMMAND_END 3 |
| #define | RELAY_COMMAND_CONNECTED 4 |
| #define | RELAY_COMMAND_SENDME 5 |
| #define | RELAY_COMMAND_EXTEND 6 |
| #define | RELAY_COMMAND_EXTENDED 7 |
| #define | RELAY_COMMAND_TRUNCATE 8 |
| #define | RELAY_COMMAND_TRUNCATED 9 |
| #define | RELAY_COMMAND_DROP 10 |
| #define | RELAY_COMMAND_RESOLVE 11 |
| #define | RELAY_COMMAND_RESOLVED 12 |
| #define | RELAY_COMMAND_BEGIN_DIR 13 |
| #define | RELAY_COMMAND_EXTEND2 14 |
| #define | RELAY_COMMAND_EXTENDED2 15 |
| #define | RELAY_COMMAND_ESTABLISH_INTRO 32 |
| #define | RELAY_COMMAND_ESTABLISH_RENDEZVOUS 33 |
| #define | RELAY_COMMAND_INTRODUCE1 34 |
| #define | RELAY_COMMAND_INTRODUCE2 35 |
| #define | RELAY_COMMAND_RENDEZVOUS1 36 |
| #define | RELAY_COMMAND_RENDEZVOUS2 37 |
| #define | RELAY_COMMAND_INTRO_ESTABLISHED 38 |
| #define | RELAY_COMMAND_RENDEZVOUS_ESTABLISHED 39 |
| #define | RELAY_COMMAND_INTRODUCE_ACK 40 |
| #define | END_OR_CONN_REASON_DONE 1 |
| #define | END_OR_CONN_REASON_REFUSED 2 /* connection refused */ |
| #define | END_OR_CONN_REASON_OR_IDENTITY 3 |
| #define | END_OR_CONN_REASON_CONNRESET 4 /* connection reset by peer */ |
| #define | END_OR_CONN_REASON_TIMEOUT 5 |
| #define | END_OR_CONN_REASON_NO_ROUTE 6 /* no route to host/net */ |
| #define | END_OR_CONN_REASON_IO_ERROR 7 /* read/write error */ |
| #define | END_OR_CONN_REASON_RESOURCE_LIMIT 8 /* sockets, buffers, etc */ |
| #define | END_OR_CONN_REASON_PT_MISSING 9 /* PT failed or not available */ |
| #define | END_OR_CONN_REASON_MISC 10 |
| #define | END_STREAM_REASON_MISC 1 |
| #define | END_STREAM_REASON_RESOLVEFAILED 2 |
| #define | END_STREAM_REASON_CONNECTREFUSED 3 |
| #define | END_STREAM_REASON_EXITPOLICY 4 |
| #define | END_STREAM_REASON_DESTROY 5 |
| #define | END_STREAM_REASON_DONE 6 |
| #define | END_STREAM_REASON_TIMEOUT 7 |
| #define | END_STREAM_REASON_NOROUTE 8 |
| #define | END_STREAM_REASON_HIBERNATING 9 |
| #define | END_STREAM_REASON_INTERNAL 10 |
| #define | END_STREAM_REASON_RESOURCELIMIT 11 |
| #define | END_STREAM_REASON_CONNRESET 12 |
| #define | END_STREAM_REASON_TORPROTOCOL 13 |
| #define | END_STREAM_REASON_NOTDIRECTORY 14 |
| #define | END_STREAM_REASON_ENTRYPOLICY 15 |
| #define | END_STREAM_REASON_CANT_ATTACH 257 |
| #define | END_STREAM_REASON_NET_UNREACHABLE 258 |
| #define | END_STREAM_REASON_SOCKSPROTOCOL 259 |
| #define | END_STREAM_REASON_CANT_FETCH_ORIG_DEST 260 |
| #define | END_STREAM_REASON_INVALID_NATD_DEST 261 |
| #define | END_STREAM_REASON_PRIVATE_ADDR 262 |
| #define | END_STREAM_REASON_HTTPPROTOCOL 263 |
| #define | END_STREAM_REASON_MASK 511 |
| #define | END_STREAM_REASON_FLAG_REMOTE 512 |
| #define | END_STREAM_REASON_FLAG_ALREADY_SENT_CLOSED 1024 |
| #define | END_STREAM_REASON_FLAG_ALREADY_SOCKS_REPLIED 2048 |
| #define | REMAP_STREAM_SOURCE_CACHE 1 |
| #define | REMAP_STREAM_SOURCE_EXIT 2 |
| #define | RESOLVED_TYPE_HOSTNAME 0 |
| #define | RESOLVED_TYPE_IPV4 4 |
| #define | RESOLVED_TYPE_IPV6 6 |
| #define | RESOLVED_TYPE_ERROR_TRANSIENT 0xF0 |
| #define | RESOLVED_TYPE_ERROR 0xF1 |
| #define | END_CIRC_REASON_IP_NOW_REDUNDANT -4 |
| #define | END_CIRC_REASON_MEASUREMENT_EXPIRED -3 |
| #define | END_CIRC_REASON_NOPATH -2 |
| #define | END_CIRC_AT_ORIGIN -1 |
| #define | END_CIRC_REASON_MIN_ 0 |
| #define | END_CIRC_REASON_NONE 0 |
| #define | END_CIRC_REASON_TORPROTOCOL 1 |
| #define | END_CIRC_REASON_INTERNAL 2 |
| #define | END_CIRC_REASON_REQUESTED 3 |
| #define | END_CIRC_REASON_HIBERNATING 4 |
| #define | END_CIRC_REASON_RESOURCELIMIT 5 |
| #define | END_CIRC_REASON_CONNECTFAILED 6 |
| #define | END_CIRC_REASON_OR_IDENTITY 7 |
| #define | END_CIRC_REASON_CHANNEL_CLOSED 8 |
| #define | END_CIRC_REASON_FINISHED 9 |
| #define | END_CIRC_REASON_TIMEOUT 10 |
| #define | END_CIRC_REASON_DESTROYED 11 |
| #define | END_CIRC_REASON_NOSUCHSERVICE 12 |
| #define | END_CIRC_REASON_MAX_ 12 |
| #define | END_CIRC_REASON_FLAG_REMOTE 512 |
| #define | REND_SERVICE_ID_LEN_BASE32 16 |
| #define | REND_SERVICE_ADDRESS_LEN (16+1+5) |
| #define | REND_SERVICE_ID_LEN 10 |
| #define | REND_TIME_PERIOD_V2_DESC_VALIDITY (24*60*60) |
| #define | REND_TIME_PERIOD_OVERLAPPING_V2_DESCS (60*60) |
| #define | REND_NUMBER_OF_NON_CONSECUTIVE_REPLICAS 2 |
| #define | REND_NUMBER_OF_CONSECUTIVE_REPLICAS 3 |
| #define | REND_DESC_ID_V2_LEN_BASE32 BASE32_DIGEST_LEN |
| #define | REND_SECRET_ID_PART_LEN_BASE32 BASE32_DIGEST_LEN |
| #define | REND_INTRO_POINT_ID_LEN_BASE32 BASE32_DIGEST_LEN |
| #define | REND_DESC_COOKIE_LEN 16 |
| #define | REND_DESC_COOKIE_LEN_BASE64 22 |
| #define | REND_BASIC_AUTH_CLIENT_ID_LEN 4 |
| #define | REND_BASIC_AUTH_CLIENT_MULTIPLE 16 |
| #define | REND_BASIC_AUTH_CLIENT_ENTRY_LEN |
| #define | REND_DESC_MAX_SIZE (20 * 1024) |
| #define | REND_LEGAL_CLIENTNAME_CHARACTERS "abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789+-_" |
| #define | REND_CLIENTNAME_MAX_LEN 16 |
| #define | REND_COOKIE_LEN DIGEST_LEN |
| #define | REND_REPLAY_TIME_INTERVAL (5 * 60) |
| #define | CIRCWINDOW_START 1000 |
| #define | CIRCWINDOW_START_MIN 100 |
| #define | CIRCWINDOW_START_MAX 1000 |
| #define | CIRCWINDOW_INCREMENT 100 |
| #define | STREAMWINDOW_START 500 |
| #define | STREAMWINDOW_INCREMENT 50 |
| #define | ORCIRC_MAX_MIDDLE_CELLS (CIRCWINDOW_START_MAX*2) |
| #define | ORCIRC_MAX_MIDDLE_KILL_THRESH (1.1f) |
| #define | CELL_PADDING 0 |
| #define | CELL_CREATE 1 |
| #define | CELL_CREATED 2 |
| #define | CELL_RELAY 3 |
| #define | CELL_DESTROY 4 |
| #define | CELL_CREATE_FAST 5 |
| #define | CELL_CREATED_FAST 6 |
| #define | CELL_VERSIONS 7 |
| #define | CELL_NETINFO 8 |
| #define | CELL_RELAY_EARLY 9 |
| #define | CELL_CREATE2 10 |
| #define | CELL_CREATED2 11 |
| #define | CELL_PADDING_NEGOTIATE 12 |
| #define | CELL_VPADDING 128 |
| #define | CELL_CERTS 129 |
| #define | CELL_AUTH_CHALLENGE 130 |
| #define | CELL_AUTHENTICATE 131 |
| #define | CELL_AUTHORIZE 132 |
| #define | CELL_COMMAND_MAX_ 132 |
| #define | TIMEOUT_UNTIL_UNREACHABILITY_COMPLAINT (20*60) |
| #define | LEGAL_NICKNAME_CHARACTERS "abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789" |
| #define | DEFAULT_CLIENT_NICKNAME "client" |
| #define | UNNAMED_ROUTER_NICKNAME "Unnamed" |
| #define | SOCKS4_NETWORK_LEN 8 |
| #define | CELL_PAYLOAD_SIZE 509 |
| #define | CELL_MAX_NETWORK_SIZE 514 |
| #define | VAR_CELL_MAX_HEADER_SIZE 7 |
| #define | RELAY_HEADER_SIZE (1+2+2+4+2) |
| #define | RELAY_PAYLOAD_SIZE (CELL_PAYLOAD_SIZE-RELAY_HEADER_SIZE) |
| #define | BASE_CONNECTION_MAGIC 0x7C3C304Eu |
| #define | OR_CONNECTION_MAGIC 0x7D31FF03u |
| #define | EDGE_CONNECTION_MAGIC 0xF0374013u |
| #define | ENTRY_CONNECTION_MAGIC 0xbb4a5703 |
| #define | DIR_CONNECTION_MAGIC 0x9988ffeeu |
| #define | CONTROL_CONNECTION_MAGIC 0x8abc765du |
| #define | LISTENER_CONNECTION_MAGIC 0x1a1ac741u |
| #define | OR_AUTH_CHALLENGE_LEN 32 |
| #define | AUTHTYPE_RSA_SHA256_TLSSECRET 1 |
| #define | AUTHTYPE_RSA_SHA256_RFC5705 2 |
| #define | AUTHTYPE_ED25519_SHA256_RFC5705 3 |
| #define | V3_AUTH_FIXED_PART_LEN (8+(32*6)) |
| #define | V3_AUTH_BODY_LEN (V3_AUTH_FIXED_PART_LEN + 8 + 16) |
| #define | EXT_OR_CONN_ID_LEN DIGEST_LEN /* 20 */ |
| #define | OR_CONN_HIGHWATER (32*1024) |
| #define | OR_CONN_LOWWATER (16*1024) |
| #define | DEBUGGING_17659 |
| #define | NUM_CIRCUITS_LAUNCHED_THRESHOLD 10 |
| #define | TO_CONN(c) (&(((c)->base_))) |
| #define | ENTRY_TO_EDGE_CONN(c) (&(((c))->edge_)) |
| #define | ENTRY_TO_CONN(c) (TO_CONN(ENTRY_TO_EDGE_CONN(c))) |
| #define | addr_policy_action_bitfield_t ENUM_BF(addr_policy_action_t) |
| #define | saved_location_bitfield_t ENUM_BF(saved_location_t) |
| #define | download_schedule_bitfield_t ENUM_BF(download_schedule_t) |
| #define | download_want_authority_bitfield_t ENUM_BF(download_want_authority_t) |
| #define | download_schedule_increment_bitfield_t ENUM_BF(download_schedule_increment_t) |
| #define | IMPOSSIBLE_TO_DOWNLOAD 255 |
| #define | ROUTER_ANNOTATION_BUF_LEN 256 |
| #define | ROUTER_PURPOSE_GENERAL 0 |
| #define | ROUTER_PURPOSE_CONTROLLER 1 |
| #define | ROUTER_PURPOSE_BRIDGE 2 |
| #define | ROUTER_PURPOSE_UNKNOWN 255 |
| #define | MAX_KNOWN_FLAGS_IN_VOTE 64 |
| #define | N_CONSENSUS_FLAVORS ((int)(FLAV_MICRODESC)+1) |
| #define | ALL_DIRINFO ((dirinfo_type_t)((1<<7)-1)) |
| #define | CRYPT_PATH_MAGIC 0x70127012u |
| #define | ONION_HANDSHAKE_TYPE_TAP 0x0000 |
| #define | ONION_HANDSHAKE_TYPE_FAST 0x0001 |
| #define | ONION_HANDSHAKE_TYPE_NTOR 0x0002 |
| #define | MAX_ONION_HANDSHAKE_TYPE 0x0002 |
| #define | CPATH_STATE_CLOSED 0 |
| #define | CPATH_STATE_AWAITING_KEYS 1 |
| #define | CPATH_STATE_OPEN 2 |
| #define | CPATH_KEY_MATERIAL_LEN (20*2+16*2) |
| #define | DH_KEY_LEN DH_BYTES |
| #define | ORIGIN_CIRCUIT_MAGIC 0x35315243u |
| #define | OR_CIRCUIT_MAGIC 0x98ABC04Fu |
| #define | DEAD_CIRCUIT_MAGIC 0xdeadc14c |
| #define | MAX_RELAY_EARLY_CELLS_PER_CIRCUIT 8 |
| #define | path_state_bitfield_t ENUM_BF(path_state_t) |
| #define | PATHBIAS_SHOULDCOUNT_UNDECIDED 0 |
| #define | PATHBIAS_SHOULDCOUNT_IGNORED 1 |
| #define | PATHBIAS_SHOULDCOUNT_COUNTED 2 |
| #define | REND_TOKEN_LEN DIGEST_LEN |
| #define | TO_CIRCUIT(x) (&((x)->base_)) |
| #define | MIN_CONSTRAINED_TCP_BUFFER 2048 |
| #define | MAX_CONSTRAINED_TCP_BUFFER 262144 /* 256k */ |
| #define | ISO_DEFAULT (ISO_CLIENTADDR|ISO_SOCKSAUTH|ISO_SESSIONGRP|ISO_NYM_EPOCH) |
| #define | SESSION_GROUP_UNSET -1 |
| #define | SESSION_GROUP_DIRCONN -2 |
| #define | SESSION_GROUP_CONTROL_RESOLVE -3 |
| #define | SESSION_GROUP_FIRST_AUTO -4 |
| #define | CFG_AUTO_PORT 0xc4005e |
| #define | MAX_MAX_CLIENT_CIRCUITS_PENDING 1024 |
| #define | LOG_PROTOCOL_WARN (get_protocol_warning_severity_level()) |
| #define | MAX_SOCKS_REPLY_LEN 1024 |
| #define | MAX_SOCKS_ADDR_LEN 256 |
| #define | SOCKS_NO_AUTH 0x00 |
| #define | SOCKS_USER_PASS 0x02 |
| #define | SOCKS_COMMAND_CONNECT 0x01 |
| #define | SOCKS_COMMAND_RESOLVE 0xF0 |
| #define | SOCKS_COMMAND_RESOLVE_PTR 0xF1 |
| #define | SOCKS_COMMAND_IS_CONNECT(c) (((c)==SOCKS_COMMAND_CONNECT) || 0) |
| #define | SOCKS_COMMAND_IS_RESOLVE(c) |
| #define | DEFAULT_ROUTE_LEN 3 |
| #define | BW_WEIGHT_SCALE 10000 |
| #define | BW_MIN_WEIGHT_SCALE 1 |
| #define | BW_MAX_WEIGHT_SCALE INT32_MAX |
| #define | CBT_NCIRCUITS_TO_OBSERVE 1000 |
| #define | CBT_BIN_WIDTH ((build_time_t)50) |
| #define | CBT_DEFAULT_NUM_XM_MODES 3 |
| #define | CBT_MIN_NUM_XM_MODES 1 |
| #define | CBT_MAX_NUM_XM_MODES 20 |
| #define | CBT_BUILD_ABANDONED ((build_time_t)(INT32_MAX-1)) |
| #define | CBT_BUILD_TIME_MAX ((build_time_t)(INT32_MAX)) |
| #define | CBT_SAVE_STATE_EVERY 10 |
| #define | CBT_DEFAULT_CLOSE_QUANTILE 95 |
| #define | CBT_MIN_CLOSE_QUANTILE CBT_MIN_QUANTILE_CUTOFF |
| #define | CBT_MAX_CLOSE_QUANTILE CBT_MAX_QUANTILE_CUTOFF |
| #define | CBT_DEFAULT_RECENT_CIRCUITS 20 |
| #define | CBT_MIN_RECENT_CIRCUITS 3 |
| #define | CBT_MAX_RECENT_CIRCUITS 1000 |
| #define | CBT_DEFAULT_MAX_RECENT_TIMEOUT_COUNT (CBT_DEFAULT_RECENT_CIRCUITS*9/10) |
| #define | CBT_MIN_MAX_RECENT_TIMEOUT_COUNT 3 |
| #define | CBT_MAX_MAX_RECENT_TIMEOUT_COUNT 10000 |
| #define | CBT_DEFAULT_MIN_CIRCUITS_TO_OBSERVE 100 |
| #define | CBT_MIN_MIN_CIRCUITS_TO_OBSERVE 1 |
| #define | CBT_MAX_MIN_CIRCUITS_TO_OBSERVE 10000 |
| #define | CBT_DEFAULT_QUANTILE_CUTOFF 80 |
| #define | CBT_MIN_QUANTILE_CUTOFF 10 |
| #define | CBT_MAX_QUANTILE_CUTOFF 99 |
| #define | CBT_DEFAULT_TEST_FREQUENCY 10 |
| #define | CBT_MIN_TEST_FREQUENCY 1 |
| #define | CBT_MAX_TEST_FREQUENCY INT32_MAX |
| #define | CBT_DEFAULT_TIMEOUT_MIN_VALUE (1500) |
| #define | CBT_MIN_TIMEOUT_MIN_VALUE 500 |
| #define | CBT_MAX_TIMEOUT_MIN_VALUE INT32_MAX |
| #define | CBT_DEFAULT_TIMEOUT_INITIAL_VALUE (60*1000) |
| #define | CBT_MIN_TIMEOUT_INITIAL_VALUE CBT_MIN_TIMEOUT_MIN_VALUE |
| #define | CBT_MAX_TIMEOUT_INITIAL_VALUE INT32_MAX |
| #define | addressmap_entry_source_bitfield_t ENUM_BF(addressmap_entry_source_t) |
| #define | CONN_LOG_PROTECT(conn, stmt) |
| #define | GEOIP_NS_RESPONSE_NUM 6 |
| #define | WRITE_STATS_INTERVAL (24*60*60) |
| #define | MAX_INTRO_POINT_REACHABILITY_FAILURES 5 |
| #define | INTRO_POINT_MIN_LIFETIME_INTRODUCTIONS 16384 |
| #define | INTRO_POINT_MAX_LIFETIME_INTRODUCTIONS (INTRO_POINT_MIN_LIFETIME_INTRODUCTIONS * 2) |
| #define | INTRO_POINT_LIFETIME_MIN_SECONDS (18*60*60) |
| #define | INTRO_POINT_LIFETIME_MAX_SECONDS (24*60*60) |
| #define | MAX_INTRO_POINT_CIRCUIT_RETRIES 3 |
| #define | REND_PROTOCOL_VERSION_BITMASK_WIDTH 16 |
| #define | RELAY_REQUIRED_MIN_BANDWIDTH (75*1024) |
| #define | BRIDGE_REQUIRED_MIN_BANDWIDTH (50*1024) |
| #define | ROUTER_MAX_DECLARED_BANDWIDTH INT32_MAX |
| #define | PDS_ALLOW_SELF (1<<0) |
| #define | PDS_RETRY_IF_NO_SERVERS (1<<1) |
| #define | PDS_IGNORE_FASCISTFIREWALL (1<<2) |
| #define | PDS_NO_EXISTING_SERVERDESC_FETCH (1<<3) |
| #define | PDS_NO_EXISTING_MICRODESC_FETCH (1<<4) |
| #define | MAX_STATUS_TAG_LEN 32 |
Certificate types for CERTS cells. | |
These values are defined by the protocol, and affect how an X509 certificate in a CERTS cell is interpreted and used. | |
| #define | OR_CERT_TYPE_TLS_LINK 1 |
| #define | OR_CERT_TYPE_ID_1024 2 |
| #define | OR_CERT_TYPE_AUTH_1024 3 |
| #define | OR_CERT_TYPE_RSA_ED_CROSSCERT 7 |
Isolation flags | |
Ways to isolate client streams | |
| #define | ISO_DESTPORT (1u<<0) |
| #define | ISO_DESTADDR (1u<<1) |
| #define | ISO_SOCKSAUTH (1u<<2) |
| #define | ISO_CLIENTPROTO (1u<<3) |
| #define | ISO_CLIENTADDR (1u<<4) |
| #define | ISO_SESSIONGRP (1u<<5) |
| #define | ISO_NYM_EPOCH (1u<<6) |
| #define | ISO_STREAM (1u<<7) |
Enumerations | |
| enum | circ_id_type_t { CIRC_ID_TYPE_LOWER =0, CIRC_ID_TYPE_HIGHER =1, CIRC_ID_TYPE_NEITHER =2 } |
| enum | rend_auth_type_t { REND_NO_AUTH = 0, REND_BASIC_AUTH = 1, REND_STEALTH_AUTH = 2 } |
| enum | cell_direction_t { CELL_DIRECTION_IN =1, CELL_DIRECTION_OUT =2 } |
| enum | channel_state_t { CHANNEL_STATE_CLOSED = 0, CHANNEL_STATE_OPENING, CHANNEL_STATE_OPEN, CHANNEL_STATE_MAINT, CHANNEL_STATE_CLOSING, CHANNEL_STATE_ERROR, CHANNEL_STATE_LAST } |
| enum | channel_listener_state_t { CHANNEL_LISTENER_STATE_CLOSED = 0, CHANNEL_LISTENER_STATE_LISTENING, CHANNEL_LISTENER_STATE_CLOSING, CHANNEL_LISTENER_STATE_ERROR, CHANNEL_LISTENER_STATE_LAST } |
| enum | addr_policy_action_t { ADDR_POLICY_ACCEPT =1, ADDR_POLICY_REJECT =2 } |
| enum | saved_location_t { SAVED_NOWHERE =0, SAVED_IN_CACHE, SAVED_IN_JOURNAL } |
| enum | download_schedule_t { DL_SCHED_GENERIC = 0, DL_SCHED_CONSENSUS = 1, DL_SCHED_BRIDGE = 2 } |
| enum | download_want_authority_t { DL_WANT_ANY_DIRSERVER = 0, DL_WANT_AUTHORITY = 1 } |
| enum | download_schedule_increment_t { DL_SCHED_INCREMENT_FAILURE = 0, DL_SCHED_INCREMENT_ATTEMPT = 1 } |
| enum | networkstatus_type_t { NS_TYPE_VOTE, NS_TYPE_CONSENSUS, NS_TYPE_OPINION } |
| enum | consensus_flavor_t { FLAV_NS = 0, FLAV_MICRODESC = 1 } |
| enum | store_type_t { ROUTER_STORE = 0, EXTRAINFO_STORE = 1 } |
| enum | dirinfo_type_t { NO_DIRINFO = 0, V3_DIRINFO = 1 << 2, BRIDGE_DIRINFO = 1 << 4, EXTRAINFO_DIRINFO =1 << 5, MICRODESC_DIRINFO =1 << 6 } |
| enum | path_state_t { PATH_STATE_NEW_CIRC = 0, PATH_STATE_BUILD_ATTEMPTED = 1, PATH_STATE_BUILD_SUCCEEDED = 2, PATH_STATE_USE_ATTEMPTED = 3, PATH_STATE_USE_SUCCEEDED = 4, PATH_STATE_USE_FAILED = 5, PATH_STATE_ALREADY_COUNTED = 6 } |
| enum | outbound_addr_t { OUTBOUND_ADDR_EXIT, OUTBOUND_ADDR_OR, OUTBOUND_ADDR_EXIT_AND_OR, OUTBOUND_ADDR_MAX } |
| enum | setopt_err_t { SETOPT_OK = 0, SETOPT_ERR_MISC = -1, SETOPT_ERR_PARSE = -2, SETOPT_ERR_TRANSITION = -3, SETOPT_ERR_SETTING = -4 } |
| enum | addressmap_entry_source_t { ADDRMAPSRC_CONTROLLER, ADDRMAPSRC_AUTOMAP, ADDRMAPSRC_TORRC, ADDRMAPSRC_TRACKEXIT, ADDRMAPSRC_DNS, ADDRMAPSRC_NONE } |
| enum | circuit_status_event_t { CIRC_EVENT_LAUNCHED = 0, CIRC_EVENT_BUILT = 1, CIRC_EVENT_EXTENDED = 2, CIRC_EVENT_FAILED = 3, CIRC_EVENT_CLOSED = 4 } |
| enum | circuit_status_minor_event_t { CIRC_MINOR_EVENT_PURPOSE_CHANGED, CIRC_MINOR_EVENT_CANNIBALIZED } |
| enum | stream_status_event_t { STREAM_EVENT_SENT_CONNECT = 0, STREAM_EVENT_SENT_RESOLVE = 1, STREAM_EVENT_SUCCEEDED = 2, STREAM_EVENT_FAILED = 3, STREAM_EVENT_CLOSED = 4, STREAM_EVENT_NEW = 5, STREAM_EVENT_NEW_RESOLVE = 6, STREAM_EVENT_FAILED_RETRIABLE = 7, STREAM_EVENT_REMAP = 8 } |
| enum | or_conn_status_event_t { OR_CONN_EVENT_LAUNCHED = 0, OR_CONN_EVENT_CONNECTED = 1, OR_CONN_EVENT_FAILED = 2, OR_CONN_EVENT_CLOSED = 3, OR_CONN_EVENT_NEW = 4 } |
| enum | buildtimeout_set_event_t { BUILDTIMEOUT_SET_EVENT_COMPUTED = 0, BUILDTIMEOUT_SET_EVENT_RESET = 1, BUILDTIMEOUT_SET_EVENT_SUSPENDED = 2, BUILDTIMEOUT_SET_EVENT_DISCARD = 3, BUILDTIMEOUT_SET_EVENT_RESUME = 4 } |
| enum | bootstrap_status_t { BOOTSTRAP_STATUS_UNDEF =-1, BOOTSTRAP_STATUS_STARTING =0, BOOTSTRAP_STATUS_CONN_DIR =5, BOOTSTRAP_STATUS_HANDSHAKE =-2, BOOTSTRAP_STATUS_HANDSHAKE_DIR =10, BOOTSTRAP_STATUS_ONEHOP_CREATE =15, BOOTSTRAP_STATUS_REQUESTING_STATUS =20, BOOTSTRAP_STATUS_LOADING_STATUS =25, BOOTSTRAP_STATUS_LOADING_KEYS =40, BOOTSTRAP_STATUS_REQUESTING_DESCRIPTORS =45, BOOTSTRAP_STATUS_LOADING_DESCRIPTORS =50, BOOTSTRAP_STATUS_CONN_OR =80, BOOTSTRAP_STATUS_HANDSHAKE_OR =85, BOOTSTRAP_STATUS_CIRCUIT_CREATE =90, BOOTSTRAP_STATUS_DONE =100 } |
| enum | routerstatus_format_type_t { NS_V2, NS_V3_CONSENSUS, NS_V3_VOTE, NS_CONTROL_PORT, NS_V3_CONSENSUS_MICRODESC } |
| enum | geoip_client_action_t { GEOIP_CLIENT_CONNECT = 0, GEOIP_CLIENT_NETWORKSTATUS = 1 } |
| enum | geoip_ns_response_t { GEOIP_SUCCESS = 0, GEOIP_REJECT_NOT_ENOUGH_SIGS = 1, GEOIP_REJECT_UNAVAILABLE = 2, GEOIP_REJECT_NOT_FOUND = 3, GEOIP_REJECT_NOT_MODIFIED = 4, GEOIP_REJECT_BUSY = 5 } |
| enum | dirreq_type_t { DIRREQ_DIRECT = 0, DIRREQ_TUNNELED = 1 } |
| enum | dirreq_state_t { DIRREQ_IS_FOR_NETWORK_STATUS = 0, DIRREQ_FLUSHING_DIR_CONN_FINISHED = 1, DIRREQ_END_CELL_SENT = 2, DIRREQ_CIRC_QUEUE_FLUSHED = 3, DIRREQ_CHANNEL_BUFFER_FLUSHED = 4 } |
| enum | version_status_t { VS_RECOMMENDED =0, VS_OLD =1, VS_NEW =2, VS_NEW_IN_SERIES =3, VS_UNRECOMMENDED =4, VS_EMPTY =5, VS_UNKNOWN } |
| enum | addr_policy_result_t { ADDR_POLICY_ACCEPTED =0, ADDR_POLICY_REJECTED =-1, ADDR_POLICY_PROBABLY_ACCEPTED =1, ADDR_POLICY_PROBABLY_REJECTED =2 } |
| enum | pk_op_t { SIGN_DIR, SIGN_RTR, VERIFY_DIR, VERIFY_RTR, ENC_ONIONSKIN, DEC_ONIONSKIN, TLS_HANDSHAKE_C, TLS_HANDSHAKE_S, REND_CLIENT, REND_MID, REND_SERVER } |
| enum | bandwidth_weight_rule_t { NO_WEIGHTING, WEIGHT_FOR_EXIT, WEIGHT_FOR_MID, WEIGHT_FOR_GUARD, WEIGHT_FOR_DIR } |
| enum | router_crn_flags_t { CRN_NEED_UPTIME = 1<<0, CRN_NEED_CAPACITY = 1<<1, CRN_NEED_GUARD = 1<<2, CRN_WEIGHT_AS_EXIT = 1<<5, CRN_NEED_DESC = 1<<6, CRN_PREF_ADDR = 1<<7, CRN_DIRECT_CONN = 1<<8, CRN_RENDEZVOUS_V3 = 1<<9 } |
| enum | was_router_added_t { ROUTER_ADDED_SUCCESSFULLY = 1, ROUTER_BAD_EI = -1, ROUTER_IS_ALREADY_KNOWN = -2, ROUTER_NOT_IN_CONSENSUS = -3, ROUTER_NOT_IN_CONSENSUS_OR_NETWORKSTATUS = -4, ROUTER_AUTHDIR_REJECTS = -5, ROUTER_WAS_NOT_WANTED = -6, ROUTER_WAS_TOO_OLD = -7, ROUTER_CERTS_EXPIRED = -8 } |
Functions | |
| double | circuit_build_times_quantile_cutoff (void) |
| int32_t | circuit_build_times_initial_timeout (void) |
Detailed Description
Master header file for Tor-specific functionality.
Macro Definition Documentation
◆ AP_CONN_STATE_CIRCUIT_WAIT
| #define AP_CONN_STATE_CIRCUIT_WAIT 8 |
State for a SOCKS connection: waiting for a completed circuit.
◆ AP_CONN_STATE_CONNECT_WAIT
| #define AP_CONN_STATE_CONNECT_WAIT 9 |
State for a SOCKS connection: sent BEGIN, waiting for CONNECTED.
◆ AP_CONN_STATE_CONTROLLER_WAIT
| #define AP_CONN_STATE_CONTROLLER_WAIT 7 |
The controller will attach this connection to a circuit; it isn't our job to do so.
◆ AP_CONN_STATE_HTTP_CONNECT_WAIT
| #define AP_CONN_STATE_HTTP_CONNECT_WAIT 13 |
State for an HTTP tunnel: waiting for an HTTP CONNECT command.
◆ AP_CONN_STATE_IS_UNATTACHED
| #define AP_CONN_STATE_IS_UNATTACHED | ( | s | ) | ((s) <= AP_CONN_STATE_CIRCUIT_WAIT || (s) == AP_CONN_STATE_NATD_WAIT) |
True iff the AP_CONN_STATE_* value s means that the corresponding edge connection is not attached to any circuit.
◆ AP_CONN_STATE_NATD_WAIT
| #define AP_CONN_STATE_NATD_WAIT 12 |
State for a transparent natd connection: waiting for original destination.
◆ AP_CONN_STATE_OPEN
| #define AP_CONN_STATE_OPEN 11 |
State for a SOCKS connection: ready to send and receive.
◆ AP_CONN_STATE_RENDDESC_WAIT
| #define AP_CONN_STATE_RENDDESC_WAIT 6 |
State for a SOCKS connection: got a y.onion URL; waiting to receive rendezvous descriptor.
◆ AP_CONN_STATE_RESOLVE_WAIT
| #define AP_CONN_STATE_RESOLVE_WAIT 10 |
State for a SOCKS connection: sent RESOLVE, waiting for RESOLVED.
◆ AP_CONN_STATE_SOCKS_WAIT
| #define AP_CONN_STATE_SOCKS_WAIT 5 |
State for a SOCKS connection: waiting for SOCKS request.
◆ AUTHTYPE_ED25519_SHA256_RFC5705
| #define AUTHTYPE_ED25519_SHA256_RFC5705 3 |
As AUTHTYPE_RSA_SHA256_RFC5705, but uses an Ed25519 identity key to authenticate.
◆ AUTHTYPE_RSA_SHA256_RFC5705
| #define AUTHTYPE_RSA_SHA256_RFC5705 2 |
As AUTHTYPE_RSA_SHA256_TLSSECRET, but instead of using the negotiated TLS secrets, uses exported keying material from the TLS session as described in RFC 5705.
Not used by today's tors, since everything that supports this also supports ED25519_SHA256_5705, which is better.
◆ AUTHTYPE_RSA_SHA256_TLSSECRET
| #define AUTHTYPE_RSA_SHA256_TLSSECRET 1 |
The first supported type of AUTHENTICATE cell. It contains a bunch of structures signed with an RSA1024 key. The signed structures include a HMAC using negotiated TLS secrets, and a digest of all cells sent or received before the AUTHENTICATE cell (including the random server-generated AUTH_CHALLENGE cell).
◆ BW_WEIGHT_SCALE
| #define BW_WEIGHT_SCALE 10000 |
Precision multiplier for the Bw weights
◆ CBT_BIN_WIDTH
| #define CBT_BIN_WIDTH ((build_time_t)50) |
Width of the histogram bins in milliseconds
◆ CBT_BUILD_ABANDONED
| #define CBT_BUILD_ABANDONED ((build_time_t)(INT32_MAX-1)) |
CBT_BUILD_ABANDONED is our flag value to represent a force-closed circuit (Aka a 'right-censored' pareto value).
◆ CBT_DEFAULT_CLOSE_QUANTILE
| #define CBT_DEFAULT_CLOSE_QUANTILE 95 |
How long to wait before actually closing circuits that take too long to build in terms of CDF quantile.
◆ CBT_DEFAULT_MAX_RECENT_TIMEOUT_COUNT
| #define CBT_DEFAULT_MAX_RECENT_TIMEOUT_COUNT (CBT_DEFAULT_RECENT_CIRCUITS*9/10) |
Maximum count of timeouts that finish the first hop in the past RECENT_CIRCUITS before calculating a new timeout.
This tells us whether to abandon timeout history and set the timeout back to whatever circuit_build_times_get_initial_timeout() gives us.
◆ CBT_DEFAULT_MIN_CIRCUITS_TO_OBSERVE
| #define CBT_DEFAULT_MIN_CIRCUITS_TO_OBSERVE 100 |
Minimum circuits before estimating a timeout
◆ CBT_DEFAULT_NUM_XM_MODES
| #define CBT_DEFAULT_NUM_XM_MODES 3 |
Number of modes to use in the weighted-avg computation of Xm
◆ CBT_DEFAULT_QUANTILE_CUTOFF
| #define CBT_DEFAULT_QUANTILE_CUTOFF 80 |
Cutoff percentile on the CDF for our timeout estimation.
◆ CBT_DEFAULT_RECENT_CIRCUITS
| #define CBT_DEFAULT_RECENT_CIRCUITS 20 |
How many circuits count as recent when considering if the connection has gone gimpy or changed.
◆ CBT_DEFAULT_TEST_FREQUENCY
| #define CBT_DEFAULT_TEST_FREQUENCY 10 |
How often in seconds should we build a test circuit
◆ CBT_DEFAULT_TIMEOUT_INITIAL_VALUE
| #define CBT_DEFAULT_TIMEOUT_INITIAL_VALUE (60*1000) |
Initial circuit build timeout in milliseconds
◆ CBT_DEFAULT_TIMEOUT_MIN_VALUE
| #define CBT_DEFAULT_TIMEOUT_MIN_VALUE (1500) |
Lowest allowable value for CircuitBuildTimeout in milliseconds
◆ CBT_NCIRCUITS_TO_OBSERVE
| #define CBT_NCIRCUITS_TO_OBSERVE 1000 |
Total size of the circuit timeout history to accumulate. 1000 is approx 2.5 days worth of continual-use circuits.
◆ CBT_SAVE_STATE_EVERY
| #define CBT_SAVE_STATE_EVERY 10 |
Save state every 10 circuits
◆ CELL_MAX_NETWORK_SIZE
| #define CELL_MAX_NETWORK_SIZE 514 |
Number of bytes in a cell transmitted over the network, in the longest form
◆ CELL_PAYLOAD_SIZE
| #define CELL_PAYLOAD_SIZE 509 |
Number of bytes in a cell, minus cell header.
◆ CFG_AUTO_PORT
| #define CFG_AUTO_PORT 0xc4005e |
A magic value for the (Socks|OR|...)Port options below, telling Tor to pick its own port.
◆ CIRCUIT_IS_ORCIRC
| #define CIRCUIT_IS_ORCIRC | ( | c | ) | (((circuit_t *)(c))->magic == OR_CIRCUIT_MAGIC) |
True iff the circuit_t c is actually an or_circuit_t
◆ CIRCUIT_IS_ORIGIN
| #define CIRCUIT_IS_ORIGIN | ( | c | ) | (CIRCUIT_PURPOSE_IS_ORIGIN((c)->purpose)) |
True iff the circuit_t c is actually an origin_circuit_t.
◆ CIRCUIT_PURPOSE_C_ESTABLISH_REND
| #define CIRCUIT_PURPOSE_C_ESTABLISH_REND 9 |
Client-side circuit purpose: at the client, waiting for ack.
◆ CIRCUIT_PURPOSE_C_GENERAL
| #define CIRCUIT_PURPOSE_C_GENERAL 5 |
Client-side circuit purpose: Normal circuit, with cpath.
◆ CIRCUIT_PURPOSE_C_HSDIR_GET
| #define CIRCUIT_PURPOSE_C_HSDIR_GET 13 |
This circuit is used for getting hsdirs
◆ CIRCUIT_PURPOSE_C_INTRODUCE_ACK_WAIT
| #define CIRCUIT_PURPOSE_C_INTRODUCE_ACK_WAIT 7 |
Client-side circuit purpose: at the client, sent INTRODUCE1 to intro point, waiting for ACK/NAK.
◆ CIRCUIT_PURPOSE_C_INTRODUCE_ACKED
| #define CIRCUIT_PURPOSE_C_INTRODUCE_ACKED 8 |
Client-side circuit purpose: at the client, introduced and acked, closing.
◆ CIRCUIT_PURPOSE_C_INTRODUCING
| #define CIRCUIT_PURPOSE_C_INTRODUCING 6 |
Client-side circuit purpose: at the client, connecting to intro point.
◆ CIRCUIT_PURPOSE_C_MEASURE_TIMEOUT
| #define CIRCUIT_PURPOSE_C_MEASURE_TIMEOUT 14 |
This circuit is used for build time measurement only
◆ CIRCUIT_PURPOSE_C_REND_JOINED
| #define CIRCUIT_PURPOSE_C_REND_JOINED 12 |
Client-side circuit purpose: at the client, rendezvous established.
◆ CIRCUIT_PURPOSE_C_REND_READY
| #define CIRCUIT_PURPOSE_C_REND_READY 10 |
Client-side circuit purpose: at the client, waiting for the service.
◆ CIRCUIT_PURPOSE_C_REND_READY_INTRO_ACKED
| #define CIRCUIT_PURPOSE_C_REND_READY_INTRO_ACKED 11 |
Client-side circuit purpose: at the client, waiting for the service, INTRODUCE has been acknowledged.
◆ CIRCUIT_PURPOSE_CONTROLLER
| #define CIRCUIT_PURPOSE_CONTROLLER 21 |
A controller made this circuit and Tor should not use it.
◆ CIRCUIT_PURPOSE_COUNTS_TOWARDS_MAXPENDING
| #define CIRCUIT_PURPOSE_COUNTS_TOWARDS_MAXPENDING | ( | p | ) |
True iff this circuit purpose should count towards the global pending rate limit (set by MaxClientCircuitsPending). We count all general purpose circuits, as well as the first step of client onion service connections (HSDir gets).
◆ CIRCUIT_PURPOSE_HS_VANGUARDS
| #define CIRCUIT_PURPOSE_HS_VANGUARDS 23 |
This circuit is used for vanguards/restricted paths.
This type of circuit is only created preemptively and never on-demand. When an HS operation needs to take place (e.g. connect to an intro point), these circuits are then cannibalized and repurposed to the actual needed HS purpose.
◆ CIRCUIT_PURPOSE_INTRO_POINT
| #define CIRCUIT_PURPOSE_INTRO_POINT 2 |
OR-side circuit purpose: At OR, from the service, waiting for intro from clients.
◆ CIRCUIT_PURPOSE_IS_CLIENT
| #define CIRCUIT_PURPOSE_IS_CLIENT | ( | p | ) |
True iff the circuit purpose p is for a circuit that originated here to serve as a client. (Hidden services don't count here.)
◆ CIRCUIT_PURPOSE_IS_ESTABLISHED_REND
| #define CIRCUIT_PURPOSE_IS_ESTABLISHED_REND | ( | p | ) |
True iff the circuit purpose p is for an established rendezvous circuit.
◆ CIRCUIT_PURPOSE_IS_ORIGIN
| #define CIRCUIT_PURPOSE_IS_ORIGIN | ( | p | ) | ((p)>CIRCUIT_PURPOSE_OR_MAX_) |
True iff the circuit purpose p is for a circuit that originated at this node.
◆ CIRCUIT_PURPOSE_OR
| #define CIRCUIT_PURPOSE_OR 1 |
OR-side circuit purpose: normal circuit, at OR.
◆ CIRCUIT_PURPOSE_PATH_BIAS_TESTING
| #define CIRCUIT_PURPOSE_PATH_BIAS_TESTING 22 |
This circuit is used for path bias probing only
◆ CIRCUIT_PURPOSE_REND_ESTABLISHED
| #define CIRCUIT_PURPOSE_REND_ESTABLISHED 4 |
OR-side circuit purpose: At OR, both circuits have this purpose.
◆ CIRCUIT_PURPOSE_REND_POINT_WAITING
| #define CIRCUIT_PURPOSE_REND_POINT_WAITING 3 |
OR-side circuit purpose: At OR, from the client, waiting for the service.
◆ CIRCUIT_PURPOSE_S_CONNECT_REND
| #define CIRCUIT_PURPOSE_S_CONNECT_REND 17 |
Hidden-service-side circuit purpose: at the service, connecting to rend point.
◆ CIRCUIT_PURPOSE_S_ESTABLISH_INTRO
| #define CIRCUIT_PURPOSE_S_ESTABLISH_INTRO 15 |
Hidden-service-side circuit purpose: at the service, waiting for introductions.
◆ CIRCUIT_PURPOSE_S_HSDIR_POST
| #define CIRCUIT_PURPOSE_S_HSDIR_POST 19 |
This circuit is used for uploading hsdirs
◆ CIRCUIT_PURPOSE_S_INTRO
| #define CIRCUIT_PURPOSE_S_INTRO 16 |
Hidden-service-side circuit purpose: at the service, successfully established intro.
◆ CIRCUIT_PURPOSE_S_REND_JOINED
| #define CIRCUIT_PURPOSE_S_REND_JOINED 18 |
Hidden-service-side circuit purpose: at the service, rendezvous established.
◆ CIRCUIT_PURPOSE_TESTING
| #define CIRCUIT_PURPOSE_TESTING 20 |
A testing circuit; not meant to be used for actual traffic.
◆ CIRCUIT_PURPOSE_UNKNOWN
| #define CIRCUIT_PURPOSE_UNKNOWN 255 |
A catch-all for unrecognized purposes. Currently we don't expect to make or see any circuits with this purpose.
◆ CIRCUIT_STATE_BUILDING
| #define CIRCUIT_STATE_BUILDING 0 |
Circuit state: I'm the origin, still haven't done all my handshakes.
◆ CIRCUIT_STATE_CHAN_WAIT
| #define CIRCUIT_STATE_CHAN_WAIT 2 |
Circuit state: I'd like to deliver a create, but my n_chan is still connecting.
◆ CIRCUIT_STATE_GUARD_WAIT
| #define CIRCUIT_STATE_GUARD_WAIT 3 |
Circuit state: the circuit is open but we don't want to actually use it until we find out if a better guard will be available.
◆ CIRCUIT_STATE_ONIONSKIN_PENDING
| #define CIRCUIT_STATE_ONIONSKIN_PENDING 1 |
Circuit state: Waiting to process the onionskin.
◆ CIRCUIT_STATE_OPEN
| #define CIRCUIT_STATE_OPEN 4 |
Circuit state: onionskin(s) processed, ready to send/receive cells.
◆ CIRCWINDOW_INCREMENT
| #define CIRCWINDOW_INCREMENT 100 |
Amount to increment a circuit window when we get a circuit SENDME.
◆ CIRCWINDOW_START
| #define CIRCWINDOW_START 1000 |
Initial value for both sides of a circuit transmission window when the circuit is initialized. Measured in cells.
◆ CONN_IS_EDGE
| #define CONN_IS_EDGE | ( | x | ) | ((x)->type == CONN_TYPE_EXIT || (x)->type == CONN_TYPE_AP) |
True iff x is an edge connection.
◆ CONN_LOG_PROTECT
| #define CONN_LOG_PROTECT | ( | conn, | |
| stmt | |||
| ) |
Execute the statement stmt, which may log events concerning the connection conn. To prevent infinite loops, disable log messages being sent to controllers if conn is a control connection.
Stmt must not contain any return or goto statements.
◆ CONN_TYPE_AP
| #define CONN_TYPE_AP 7 |
A SOCKS proxy connection from the user application to the onion proxy.
◆ CONN_TYPE_AP_DNS_LISTENER
| #define CONN_TYPE_AP_DNS_LISTENER 15 |
Type for sockets listening for DNS requests.
◆ CONN_TYPE_AP_HTTP_CONNECT_LISTENER
| #define CONN_TYPE_AP_HTTP_CONNECT_LISTENER 18 |
Type for sockets listening for HTTP CONNECT tunnel connections.
◆ CONN_TYPE_AP_LISTENER
| #define CONN_TYPE_AP_LISTENER 6 |
Type for sockets listening for SOCKS connections.
◆ CONN_TYPE_AP_NATD_LISTENER
| #define CONN_TYPE_AP_NATD_LISTENER 14 |
Type for sockets listening for transparent connections redirected by natd.
◆ CONN_TYPE_AP_TRANS_LISTENER
| #define CONN_TYPE_AP_TRANS_LISTENER 13 |
Type for sockets listening for transparent connections redirected by pf or netfilter.
◆ CONN_TYPE_CONTROL
| #define CONN_TYPE_CONTROL 12 |
Type for connections from user interface process.
◆ CONN_TYPE_CONTROL_LISTENER
| #define CONN_TYPE_CONTROL_LISTENER 11 |
Type for listening for connections from user interface process.
◆ CONN_TYPE_DIR
| #define CONN_TYPE_DIR 9 |
Type for HTTP connections to the directory server.
◆ CONN_TYPE_DIR_LISTENER
| #define CONN_TYPE_DIR_LISTENER 8 |
Type for sockets listening for HTTP connections to the directory server.
◆ CONN_TYPE_EXIT
| #define CONN_TYPE_EXIT 5 |
A TCP connection from an onion router to a stream's destination.
◆ CONN_TYPE_EXT_OR
| #define CONN_TYPE_EXT_OR 16 |
Type for connections from the Extended ORPort.
◆ CONN_TYPE_EXT_OR_LISTENER
| #define CONN_TYPE_EXT_OR_LISTENER 17 |
Type for sockets listening for Extended ORPort connections.
◆ CONN_TYPE_OR
| #define CONN_TYPE_OR 4 |
A bidirectional TLS connection transmitting a sequence of cells. May be from an OR to an OR, or from an OP to an OR.
◆ CONN_TYPE_OR_LISTENER
| #define CONN_TYPE_OR_LISTENER 3 |
Type for sockets listening for OR connections.
◆ CONTROL_CONN_STATE_NEEDAUTH
| #define CONTROL_CONN_STATE_NEEDAUTH 2 |
State for a control connection: Waiting for authentication; speaking protocol v1.
◆ CONTROL_CONN_STATE_OPEN
| #define CONTROL_CONN_STATE_OPEN 1 |
State for a control connection: Authenticated and accepting v1 commands.
◆ DEAD_CIRCUIT_MAGIC
| #define DEAD_CIRCUIT_MAGIC 0xdeadc14c |
"magic" value for a circuit that would have been freed by circuit_free, but which we're keeping around until a cpuworker reply arrives. See circuit_free() for more documentation.
◆ DEFAULT_CLIENT_NICKNAME
| #define DEFAULT_CLIENT_NICKNAME "client" |
Name to use in client TLS certificates if no nickname is given. Once Tor 0.1.2.x is obsolete, we can remove this.
◆ DEFAULT_ONION_KEY_GRACE_PERIOD_DAYS
| #define DEFAULT_ONION_KEY_GRACE_PERIOD_DAYS (7) |
Default grace period for acceptance of an onion key in days.
◆ DEFAULT_ONION_KEY_LIFETIME_DAYS
| #define DEFAULT_ONION_KEY_LIFETIME_DAYS (28) |
Default lifetime for an onion key in days.
◆ DEFAULT_ROUTE_LEN
| #define DEFAULT_ROUTE_LEN 3 |
How many hops does a general-purpose circuit have by default?
◆ DIR_CONN_IS_SERVER
| #define DIR_CONN_IS_SERVER | ( | conn | ) | ((conn)->purpose == DIR_PURPOSE_SERVER) |
True iff the purpose of conn means that it's a server-side directory connection.
◆ DIR_CONN_STATE_CLIENT_FINISHED
| #define DIR_CONN_STATE_CLIENT_FINISHED 4 |
State for connection to directory server: happy and finished.
◆ DIR_CONN_STATE_CLIENT_READING
| #define DIR_CONN_STATE_CLIENT_READING 3 |
State for connection to directory server: reading HTTP response.
◆ DIR_CONN_STATE_CLIENT_SENDING
| #define DIR_CONN_STATE_CLIENT_SENDING 2 |
State for connection to directory server: sending HTTP request.
◆ DIR_CONN_STATE_CONNECTING
| #define DIR_CONN_STATE_CONNECTING 1 |
State for connection to directory server: waiting for connect().
◆ DIR_CONN_STATE_SERVER_COMMAND_WAIT
| #define DIR_CONN_STATE_SERVER_COMMAND_WAIT 5 |
State for connection at directory server: waiting for HTTP request.
◆ DIR_CONN_STATE_SERVER_WRITING
| #define DIR_CONN_STATE_SERVER_WRITING 6 |
State for connection at directory server: sending HTTP response.
◆ DIR_PURPOSE_FETCH_CERTIFICATE
| #define DIR_PURPOSE_FETCH_CERTIFICATE 15 |
A connection to a directory server: download one or more directory authority certificates.
◆ DIR_PURPOSE_FETCH_CONSENSUS
| #define DIR_PURPOSE_FETCH_CONSENSUS 14 |
A connection to a directory server: download a v3 networkstatus consensus.
◆ DIR_PURPOSE_FETCH_DETACHED_SIGNATURES
| #define DIR_PURPOSE_FETCH_DETACHED_SIGNATURES 13 |
A connection to a directory server: download a v3 detached signatures object for a consensus.
◆ DIR_PURPOSE_FETCH_EXTRAINFO
| #define DIR_PURPOSE_FETCH_EXTRAINFO 7 |
A connection to a directory server: download one or more extra-info documents.
◆ DIR_PURPOSE_FETCH_HSDESC
| #define DIR_PURPOSE_FETCH_HSDESC 21 |
A connection to a hidden service directory: fetch a v3 descriptor.
◆ DIR_PURPOSE_FETCH_MICRODESC
| #define DIR_PURPOSE_FETCH_MICRODESC 19 |
A connection to a directory server: download a microdescriptor.
◆ DIR_PURPOSE_FETCH_RENDDESC_V2
| #define DIR_PURPOSE_FETCH_RENDDESC_V2 18 |
A connection to a hidden service directory server: download a v2 rendezvous descriptor.
◆ DIR_PURPOSE_FETCH_SERVERDESC
| #define DIR_PURPOSE_FETCH_SERVERDESC 6 |
A connection to a directory server: download one or more server descriptors.
◆ DIR_PURPOSE_FETCH_STATUS_VOTE
| #define DIR_PURPOSE_FETCH_STATUS_VOTE 12 |
A connection to a directory server: download one or more v3 networkstatus votes.
◆ DIR_PURPOSE_HAS_FETCHED_HSDESC
| #define DIR_PURPOSE_HAS_FETCHED_HSDESC 22 |
A connection to a directory server: set after a hidden service descriptor is downloaded.
◆ DIR_PURPOSE_HAS_FETCHED_RENDDESC_V2
| #define DIR_PURPOSE_HAS_FETCHED_RENDDESC_V2 4 |
A connection to a directory server: set after a v2 rendezvous descriptor is downloaded.
◆ DIR_PURPOSE_IS_UPLOAD
| #define DIR_PURPOSE_IS_UPLOAD | ( | p | ) |
True iff p is a purpose corresponding to uploading data to a directory server.
◆ DIR_PURPOSE_SERVER
| #define DIR_PURPOSE_SERVER 16 |
Purpose for connection at a directory server.
◆ DIR_PURPOSE_UPLOAD_DIR
| #define DIR_PURPOSE_UPLOAD_DIR 8 |
A connection to a directory server: upload a server descriptor.
◆ DIR_PURPOSE_UPLOAD_HSDESC
| #define DIR_PURPOSE_UPLOAD_HSDESC 20 |
A connection to a hidden service directory: upload a v3 descriptor.
◆ DIR_PURPOSE_UPLOAD_RENDDESC_V2
| #define DIR_PURPOSE_UPLOAD_RENDDESC_V2 17 |
A connection to a hidden service directory server: upload a v2 rendezvous descriptor.
◆ DIR_PURPOSE_UPLOAD_SIGNATURES
| #define DIR_PURPOSE_UPLOAD_SIGNATURES 11 |
A connection to a directory server: upload a v3 consensus signature
◆ DIR_PURPOSE_UPLOAD_VOTE
| #define DIR_PURPOSE_UPLOAD_VOTE 10 |
A connection to a directory server: upload a v3 networkstatus vote.
◆ DOWNCAST
| #define DOWNCAST | ( | to, | |
| ptr | |||
| ) | ((to*)SUBTYPE_P(ptr, to, base_)) |
Helper macro: Given a pointer to to.base_, of type from*, return &to.
◆ END_CIRC_AT_ORIGIN
| #define END_CIRC_AT_ORIGIN -1 |
Catch-all "other" reason for closing origin circuits.
◆ END_CIRC_REASON_FLAG_REMOTE
| #define END_CIRC_REASON_FLAG_REMOTE 512 |
Bitwise-OR this with the argument to circuit_mark_for_close() or control_event_circuit_status() to indicate that the reason was passed through from a destroy or truncate cell.
◆ END_CIRC_REASON_MEASUREMENT_EXPIRED
| #define END_CIRC_REASON_MEASUREMENT_EXPIRED -3 |
Our post-timeout circuit time measurement period expired. We must give up now
◆ END_CIRC_REASON_NOPATH
| #define END_CIRC_REASON_NOPATH -2 |
We couldn't build a path for this circuit.
◆ END_STREAM_REASON_CANT_ATTACH
| #define END_STREAM_REASON_CANT_ATTACH 257 |
We were unable to attach the connection to any circuit at all.
◆ END_STREAM_REASON_CANT_FETCH_ORIG_DEST
| #define END_STREAM_REASON_CANT_FETCH_ORIG_DEST 260 |
This is a transparent proxy connection, but we can't extract the original target address:port.
◆ END_STREAM_REASON_FLAG_ALREADY_SENT_CLOSED
| #define END_STREAM_REASON_FLAG_ALREADY_SENT_CLOSED 1024 |
Bitwise-or this with the argument to control_event_stream_status to indicate that we already sent a CLOSED stream event.
◆ END_STREAM_REASON_FLAG_ALREADY_SOCKS_REPLIED
| #define END_STREAM_REASON_FLAG_ALREADY_SOCKS_REPLIED 2048 |
Bitwise-or this with endreason to indicate that we already sent a socks reply, and no further reply needs to be sent from connection_mark_unattached_ap().
◆ END_STREAM_REASON_FLAG_REMOTE
| #define END_STREAM_REASON_FLAG_REMOTE 512 |
Bitwise-or this with the argument to control_event_stream_status to indicate that the reason came from an END cell.
◆ END_STREAM_REASON_HTTPPROTOCOL
| #define END_STREAM_REASON_HTTPPROTOCOL 263 |
This is an HTTP tunnel connection and the client used or misused HTTP in a way we can't handle.
◆ END_STREAM_REASON_INVALID_NATD_DEST
| #define END_STREAM_REASON_INVALID_NATD_DEST 261 |
This is a connection on the NATD port, and the destination IP:Port was either ill-formed or out-of-range.
◆ END_STREAM_REASON_MASK
| #define END_STREAM_REASON_MASK 511 |
Bitwise-and this value with endreason to mask out all flags.
◆ END_STREAM_REASON_NET_UNREACHABLE
| #define END_STREAM_REASON_NET_UNREACHABLE 258 |
We can't connect to any directories at all, so we killed our streams before they can time out.
◆ END_STREAM_REASON_PRIVATE_ADDR
| #define END_STREAM_REASON_PRIVATE_ADDR 262 |
The target address is in a private network (like 127.0.0.1 or 10.0.0.1); you don't want to do that over a randomly chosen exit
◆ END_STREAM_REASON_SOCKSPROTOCOL
| #define END_STREAM_REASON_SOCKSPROTOCOL 259 |
This is a SOCKS connection, and the client used (or misused) the SOCKS protocol in a way we couldn't handle.
◆ ENTRY_TO_CONN
| #define ENTRY_TO_CONN | ( | c | ) | (TO_CONN(ENTRY_TO_EDGE_CONN(c))) |
Cast a entry_connection_t subtype pointer to a connection_t
◆ ENTRY_TO_EDGE_CONN
| #define ENTRY_TO_EDGE_CONN | ( | c | ) | (&(((c))->edge_)) |
Cast a entry_connection_t subtype pointer to a edge_connection_t
◆ EXIT_CONN_STATE_CONNECTING
| #define EXIT_CONN_STATE_CONNECTING 2 |
State for an exit connection: waiting for connect() to finish.
◆ EXIT_CONN_STATE_OPEN
| #define EXIT_CONN_STATE_OPEN 3 |
State for an exit connection: open and ready to transmit data.
◆ EXIT_CONN_STATE_RESOLVEFAILED
| #define EXIT_CONN_STATE_RESOLVEFAILED 4 |
State for an exit connection: waiting to be removed.
◆ EXIT_CONN_STATE_RESOLVING
| #define EXIT_CONN_STATE_RESOLVING 1 |
State for an exit connection: waiting for response from DNS farm.
◆ EXIT_PURPOSE_CONNECT
| #define EXIT_PURPOSE_CONNECT 1 |
This exit stream wants to do an ordinary connect.
◆ EXIT_PURPOSE_RESOLVE
| #define EXIT_PURPOSE_RESOLVE 2 |
This exit stream wants to do a resolve (either normal or reverse).
◆ EXT_OR_CONN_ID_LEN
| #define EXT_OR_CONN_ID_LEN DIGEST_LEN /* 20 */ |
Length of Extended ORPort connection identifier.
◆ EXT_OR_CONN_STATE_AUTH_WAIT_AUTH_TYPE
| #define EXT_OR_CONN_STATE_AUTH_WAIT_AUTH_TYPE 1 |
Extended ORPort authentication is waiting for the authentication type selected by the client.
◆ EXT_OR_CONN_STATE_AUTH_WAIT_CLIENT_HASH
| #define EXT_OR_CONN_STATE_AUTH_WAIT_CLIENT_HASH 3 |
Extended ORPort authentication is waiting for the client hash.
◆ EXT_OR_CONN_STATE_AUTH_WAIT_CLIENT_NONCE
| #define EXT_OR_CONN_STATE_AUTH_WAIT_CLIENT_NONCE 2 |
Extended ORPort authentication is waiting for the client nonce.
◆ EXT_OR_CONN_STATE_FLUSHING
| #define EXT_OR_CONN_STATE_FLUSHING 5 |
Extended ORPort is flushing its last messages and preparing to start accepting OR connections.
◆ EXT_OR_CONN_STATE_MIN_
| #define EXT_OR_CONN_STATE_MIN_ 1 |
States of the Extended ORPort protocol. Be careful before changing the numbers: they matter.
◆ EXT_OR_CONN_STATE_OPEN
| #define EXT_OR_CONN_STATE_OPEN 4 |
Authentication finished and the Extended ORPort is now accepting traffic.
◆ IMPOSSIBLE_TO_DOWNLOAD
| #define IMPOSSIBLE_TO_DOWNLOAD 255 |
If n_download_failures is this high, the download can never happen.
◆ INTRO_POINT_LIFETIME_MAX_SECONDS
| #define INTRO_POINT_LIFETIME_MAX_SECONDS (24*60*60) |
The maximum number of seconds that an introduction point will last before expiring due to old age.
XXX Should this be configurable?
◆ INTRO_POINT_LIFETIME_MIN_SECONDS
| #define INTRO_POINT_LIFETIME_MIN_SECONDS (18*60*60) |
The minimum number of seconds that an introduction point will last before expiring due to old age. (If it receives INTRO_POINT_LIFETIME_INTRODUCTIONS INTRODUCE2 cells, it may expire sooner.)
XXX Should this be configurable?
◆ INTRO_POINT_MIN_LIFETIME_INTRODUCTIONS
| #define INTRO_POINT_MIN_LIFETIME_INTRODUCTIONS 16384 |
The minimum and maximum number of distinct INTRODUCE2 cells which a hidden service's introduction point will receive before it begins to expire.
◆ ISO_CLIENTADDR
| #define ISO_CLIENTADDR (1u<<4) |
Isolate based on client address
◆ ISO_CLIENTPROTO
| #define ISO_CLIENTPROTO (1u<<3) |
Isolate based on client protocol choice
◆ ISO_DEFAULT
| #define ISO_DEFAULT (ISO_CLIENTADDR|ISO_SOCKSAUTH|ISO_SESSIONGRP|ISO_NYM_EPOCH) |
Default isolation level for ports.
◆ ISO_DESTADDR
| #define ISO_DESTADDR (1u<<1) |
Isolate based on destination address
◆ ISO_DESTPORT
| #define ISO_DESTPORT (1u<<0) |
Isolate based on destination port
◆ ISO_NYM_EPOCH
| #define ISO_NYM_EPOCH (1u<<6) |
Isolate based on newnym epoch (always on).
◆ ISO_SESSIONGRP
| #define ISO_SESSIONGRP (1u<<5) |
Isolate based on session group (always on).
◆ ISO_SOCKSAUTH
| #define ISO_SOCKSAUTH (1u<<2) |
Isolate based on SOCKS authentication
◆ ISO_STREAM
| #define ISO_STREAM (1u<<7) |
Isolate all streams (Internal only).
◆ LEGAL_NICKNAME_CHARACTERS
| #define LEGAL_NICKNAME_CHARACTERS "abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789" |
Legal characters in a nickname.
◆ LISTENER_STATE_READY
| #define LISTENER_STATE_READY 0 |
State for any listener connection.
◆ MAX_BUF_SIZE
| #define MAX_BUF_SIZE ((1<<24)-1) /* 16MB-1 */ |
Maximum size, in bytes, for resized buffers.
◆ MAX_DESCRIPTOR_UPLOAD_SIZE
| #define MAX_DESCRIPTOR_UPLOAD_SIZE 20000 |
Maximum size, in bytes, of a single router descriptor uploaded to us as a directory authority. Caches and clients fetch whatever descriptors the authorities tell them to fetch, and don't care about size.
◆ MAX_DIR_DL_SIZE
| #define MAX_DIR_DL_SIZE MAX_BUF_SIZE |
Maximum size, in bytes, for any directory object that we've downloaded.
◆ MAX_DIR_UL_SIZE
| #define MAX_DIR_UL_SIZE MAX_BUF_SIZE |
Maximum size, in bytes, for any directory object that we're accepting as an upload.
◆ MAX_EXTRAINFO_UPLOAD_SIZE
| #define MAX_EXTRAINFO_UPLOAD_SIZE 50000 |
Maximum size of a single extrainfo document, as above.
◆ MAX_HEADERS_SIZE
| #define MAX_HEADERS_SIZE 50000 |
For HTTP parsing: Maximum number of bytes we'll accept in the headers of an HTTP request or response.
◆ MAX_HEX_NICKNAME_LEN
| #define MAX_HEX_NICKNAME_LEN (HEX_DIGEST_LEN+1) |
Length of a router identity encoded as a hexadecimal digest, plus possible dollar sign.
◆ MAX_INTRO_POINT_CIRCUIT_RETRIES
| #define MAX_INTRO_POINT_CIRCUIT_RETRIES 3 |
The maximum number of circuit creation retry we do to an intro point before giving up. We try to reuse intro point that fails during their lifetime so this is a hard limit on the amount of time we do that.
◆ MAX_INTRO_POINT_REACHABILITY_FAILURES
| #define MAX_INTRO_POINT_REACHABILITY_FAILURES 5 |
The maximum number of non-circuit-build-timeout failures a hidden service client will tolerate while trying to build a circuit to an introduction point. See also rend_intro_point_t.unreachable_count.
◆ MAX_KNOWN_FLAGS_IN_VOTE
| #define MAX_KNOWN_FLAGS_IN_VOTE 64 |
How many known-flags are allowed in a vote? This is the width of the flags field of vote_routerstatus_t
◆ MAX_NICKNAME_LEN
| #define MAX_NICKNAME_LEN 19 |
Length of longest allowable configured nickname.
◆ MAX_ONION_KEY_LIFETIME_DAYS
| #define MAX_ONION_KEY_LIFETIME_DAYS (90) |
Maximum lifetime for an onion key in days.
◆ MAX_RELAY_EARLY_CELLS_PER_CIRCUIT
| #define MAX_RELAY_EARLY_CELLS_PER_CIRCUIT 8 |
Largest number of relay_early cells that we can send on a given circuit.
◆ MAX_SSL_KEY_LIFETIME_INTERNAL
| #define MAX_SSL_KEY_LIFETIME_INTERNAL (2*60*60) |
How often do we rotate TLS contexts?
◆ MAX_VERBOSE_NICKNAME_LEN
| #define MAX_VERBOSE_NICKNAME_LEN (1+HEX_DIGEST_LEN+1+MAX_NICKNAME_LEN) |
Maximum length of verbose router identifier: dollar sign, hex ID digest, equal sign or tilde, nickname.
◆ MIN_CIRCUITS_HANDLING_STREAM
| #define MIN_CIRCUITS_HANDLING_STREAM 2 |
How many circuits do we want simultaneously in-progress to handle a given stream?
◆ MIN_ONION_KEY_GRACE_PERIOD_DAYS
| #define MIN_ONION_KEY_GRACE_PERIOD_DAYS (1) |
Minimum grace period for acceptance of an onion key in days. The maximum value is defined in proposal #274 as being the current network consensus parameter for "onion-key-rotation-days".
◆ MIN_ONION_KEY_LIFETIME_DAYS
| #define MIN_ONION_KEY_LIFETIME_DAYS (1) |
Minimum lifetime for an onion key in days.
◆ N_CONSENSUS_FLAVORS
| #define N_CONSENSUS_FLAVORS ((int)(FLAV_MICRODESC)+1) |
How many different consensus flavors are there?
◆ OLD_ROUTER_DESC_MAX_AGE
| #define OLD_ROUTER_DESC_MAX_AGE (60*60*24*5) |
How old do we let a saved descriptor get before force-removing it?
◆ ONION_KEY_CONSENSUS_CHECK_INTERVAL
| #define ONION_KEY_CONSENSUS_CHECK_INTERVAL (60*60) |
How often we should check the network consensus if it is time to rotate or expire onion keys.
◆ OR_AUTH_CHALLENGE_LEN
| #define OR_AUTH_CHALLENGE_LEN 32 |
Minimum length of the random part of an AUTH_CHALLENGE cell.
◆ OR_CERT_TYPE_AUTH_1024
| #define OR_CERT_TYPE_AUTH_1024 3 |
A certificate that authenticates a key used in an AUTHENTICATE cell in the v3 handshake. The subject key must be a 1024-bit RSA key; it must be signed by the identity key
◆ OR_CERT_TYPE_ID_1024
| #define OR_CERT_TYPE_ID_1024 2 |
A self-signed identity certificate. The subject key must be a 1024-bit RSA key.
◆ OR_CERT_TYPE_TLS_LINK
| #define OR_CERT_TYPE_TLS_LINK 1 |
A certificate that authenticates a TLS link key. The subject key must match the key used in the TLS handshake; it must be signed by the identity key.
◆ OR_CIRCUIT_MAGIC
| #define OR_CIRCUIT_MAGIC 0x98ABC04Fu |
"magic" value for an or_circuit_t
◆ OR_CONN_HIGHWATER
| #define OR_CONN_HIGHWATER (32*1024) |
When adding cells to an OR connection's outbuf, keep adding until the outbuf is at least this long, or we run out of cells.
◆ OR_CONN_LOWWATER
| #define OR_CONN_LOWWATER (16*1024) |
Add cells to an OR connection's outbuf whenever the outbuf's data length drops below this size.
◆ OR_CONN_STATE_CONNECTING
| #define OR_CONN_STATE_CONNECTING 1 |
State for a connection to an OR: waiting for connect() to finish.
◆ OR_CONN_STATE_OPEN
| #define OR_CONN_STATE_OPEN 8 |
State for an OR connection: Ready to send/receive cells.
◆ OR_CONN_STATE_OR_HANDSHAKING_V2
| #define OR_CONN_STATE_OR_HANDSHAKING_V2 6 |
State for an OR connection: We're done with our SSL handshake, we've done renegotiation, but we haven't yet negotiated link protocol versions and sent a netinfo cell.
◆ OR_CONN_STATE_OR_HANDSHAKING_V3
| #define OR_CONN_STATE_OR_HANDSHAKING_V3 7 |
State for an OR connection: We're done with our SSL handshake, but we haven't yet negotiated link protocol versions, done a V3 handshake, and sent a netinfo cell.
◆ OR_CONN_STATE_PROXY_HANDSHAKING
| #define OR_CONN_STATE_PROXY_HANDSHAKING 2 |
State for a connection to an OR: waiting for proxy handshake to complete
◆ OR_CONN_STATE_TLS_CLIENT_RENEGOTIATING
| #define OR_CONN_STATE_TLS_CLIENT_RENEGOTIATING 4 |
State for a connection to an OR: We're doing a second SSL handshake for renegotiation purposes. (V2 handshake only.)
◆ OR_CONN_STATE_TLS_HANDSHAKING
| #define OR_CONN_STATE_TLS_HANDSHAKING 3 |
State for an OR connection client: SSL is handshaking, not done yet.
◆ OR_CONN_STATE_TLS_SERVER_RENEGOTIATING
| #define OR_CONN_STATE_TLS_SERVER_RENEGOTIATING 5 |
State for a connection at an OR: We're waiting for the client to renegotiate (to indicate a v2 handshake) or send a versions cell (to indicate a v3 handshake)
◆ ORCIRC_MAX_MIDDLE_CELLS
| #define ORCIRC_MAX_MIDDLE_CELLS (CIRCWINDOW_START_MAX*2) |
Maximum number of queued cells on a circuit for which we are the midpoint before we give up and kill it. This must be >= circwindow to avoid killing innocent circuits, and >= circwindow*2 to give leaky-pipe a chance of working someday. The ORCIRC_MAX_MIDDLE_KILL_THRESH ratio controls the margin of error between emitting a warning and killing the circuit.
◆ ORCIRC_MAX_MIDDLE_KILL_THRESH
| #define ORCIRC_MAX_MIDDLE_KILL_THRESH (1.1f) |
Ratio of hard (circuit kill) to soft (warning) thresholds for the ORCIRC_MAX_MIDDLE_CELLS tests.
◆ ORIGIN_CIRCUIT_MAGIC
| #define ORIGIN_CIRCUIT_MAGIC 0x35315243u |
"magic" value for an origin_circuit_t
◆ PDS_ALLOW_SELF
| #define PDS_ALLOW_SELF (1<<0) |
Flag to indicate that we should not automatically be willing to use ourself to answer a directory request. Passed to router_pick_directory_server (et al).
◆ PDS_IGNORE_FASCISTFIREWALL
| #define PDS_IGNORE_FASCISTFIREWALL (1<<2) |
Flag to indicate that we should not exclude directory servers that our ReachableAddress settings would exclude. This usually means that we're going to connect to the server over Tor, and so we don't need to worry about our firewall telling us we can't. Passed to router_pick_directory_server (et al).
◆ PDS_NO_EXISTING_MICRODESC_FETCH
| #define PDS_NO_EXISTING_MICRODESC_FETCH (1<<4) |
Flag to indicate that we should not use any directory authority to which we have an existing directory connection for downloading microdescs.
Passed to router_pick_directory_server (et al)
◆ PDS_NO_EXISTING_SERVERDESC_FETCH
| #define PDS_NO_EXISTING_SERVERDESC_FETCH (1<<3) |
Flag to indicate that we should not use any directory authority to which we have an existing directory connection for downloading server descriptors or extrainfo documents.
Passed to router_pick_directory_server (et al)
◆ PDS_RETRY_IF_NO_SERVERS
| #define PDS_RETRY_IF_NO_SERVERS (1<<1) |
Flag to indicate that if no servers seem to be up, we should mark all directory servers as up and try again. Passed to router_pick_directory_server (et al).
◆ RELAY_HEADER_SIZE
| #define RELAY_HEADER_SIZE (1+2+2+4+2) |
Number of bytes in a relay cell's header (not including general cell header).
◆ RELAY_PAYLOAD_SIZE
| #define RELAY_PAYLOAD_SIZE (CELL_PAYLOAD_SIZE-RELAY_HEADER_SIZE) |
Largest number of bytes that can fit in a relay cell payload.
◆ REMAP_STREAM_SOURCE_CACHE
| #define REMAP_STREAM_SOURCE_CACHE 1 |
Reason for remapping an AP connection's address: we have a cached answer.
◆ REMAP_STREAM_SOURCE_EXIT
| #define REMAP_STREAM_SOURCE_EXIT 2 |
Reason for remapping an AP connection's address: the exit node told us an answer.
◆ REND_BASIC_AUTH_CLIENT_ENTRY_LEN
| #define REND_BASIC_AUTH_CLIENT_ENTRY_LEN |
Length of client entry consisting of client identifier and encrypted session key for hidden service authorization type 'basic'.
◆ REND_BASIC_AUTH_CLIENT_ID_LEN
| #define REND_BASIC_AUTH_CLIENT_ID_LEN 4 |
Length of client identifier in encrypted introduction points for hidden service authorization type 'basic'.
◆ REND_BASIC_AUTH_CLIENT_MULTIPLE
| #define REND_BASIC_AUTH_CLIENT_MULTIPLE 16 |
Multiple of the number of clients to which the real number of clients is padded with fake clients for hidden service authorization type 'basic'.
◆ REND_CLIENTNAME_MAX_LEN
| #define REND_CLIENTNAME_MAX_LEN 16 |
Maximum length of authorized client names for a hidden service.
◆ REND_COOKIE_LEN
| #define REND_COOKIE_LEN DIGEST_LEN |
Length of the rendezvous cookie that is used to connect circuits at the rendezvous point.
◆ REND_DESC_COOKIE_LEN
| #define REND_DESC_COOKIE_LEN 16 |
Length of the descriptor cookie that is used for client authorization to hidden services.
◆ REND_DESC_COOKIE_LEN_BASE64
| #define REND_DESC_COOKIE_LEN_BASE64 22 |
Length of the base64-encoded descriptor cookie that is used for exchanging client authorization between hidden service and client.
◆ REND_DESC_ID_V2_LEN_BASE32
| #define REND_DESC_ID_V2_LEN_BASE32 BASE32_DIGEST_LEN |
Length of v2 descriptor ID (32 base32 chars = 160 bits).
◆ REND_DESC_MAX_SIZE
| #define REND_DESC_MAX_SIZE (20 * 1024) |
Maximum size of v2 hidden service descriptors.
◆ REND_INTRO_POINT_ID_LEN_BASE32
| #define REND_INTRO_POINT_ID_LEN_BASE32 BASE32_DIGEST_LEN |
Length of the base32-encoded hash of an introduction point's identity key.
◆ REND_LEGAL_CLIENTNAME_CHARACTERS
| #define REND_LEGAL_CLIENTNAME_CHARACTERS "abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789+-_" |
Legal characters for use in authorized client names for a hidden service.
◆ REND_NUMBER_OF_CONSECUTIVE_REPLICAS
| #define REND_NUMBER_OF_CONSECUTIVE_REPLICAS 3 |
Number of consecutive replicas for a descriptor.
◆ REND_NUMBER_OF_NON_CONSECUTIVE_REPLICAS
| #define REND_NUMBER_OF_NON_CONSECUTIVE_REPLICAS 2 |
Number of non-consecutive replicas (i.e. distributed somewhere in the ring) for a descriptor.
◆ REND_REPLAY_TIME_INTERVAL
| #define REND_REPLAY_TIME_INTERVAL (5 * 60) |
Time interval for tracking replays of DH public keys received in INTRODUCE2 cells. Used only to avoid launching multiple simultaneous attempts to connect to the same rendezvous point.
◆ REND_SECRET_ID_PART_LEN_BASE32
| #define REND_SECRET_ID_PART_LEN_BASE32 BASE32_DIGEST_LEN |
Length of the base32-encoded secret ID part of versioned hidden service descriptors.
◆ REND_SERVICE_ADDRESS_LEN
| #define REND_SERVICE_ADDRESS_LEN (16+1+5) |
Length of 'y.onion' including '.onion' URL.
◆ REND_SERVICE_ID_LEN
| #define REND_SERVICE_ID_LEN 10 |
Length of a binary-encoded rendezvous service ID.
◆ REND_SERVICE_ID_LEN_BASE32
| #define REND_SERVICE_ID_LEN_BASE32 16 |
Length of 'y' portion of 'y.onion' URL.
◆ REND_TIME_PERIOD_OVERLAPPING_V2_DESCS
| #define REND_TIME_PERIOD_OVERLAPPING_V2_DESCS (60*60) |
Time period within which two sets of v2 descriptors will be uploaded in parallel.
◆ REND_TIME_PERIOD_V2_DESC_VALIDITY
| #define REND_TIME_PERIOD_V2_DESC_VALIDITY (24*60*60) |
Time period for which a v2 descriptor will be valid.
◆ ROUTER_ANNOTATION_BUF_LEN
| #define ROUTER_ANNOTATION_BUF_LEN 256 |
The max size we expect router descriptor annotations we create to be. We'll accept larger ones if we see them on disk, but we won't create any that are larger than this.
◆ ROUTER_MAX_AGE
| #define ROUTER_MAX_AGE (60*60*48) |
How old do we allow a router to get before removing it from the router list? In seconds.
◆ ROUTER_MAX_AGE_TO_PUBLISH
| #define ROUTER_MAX_AGE_TO_PUBLISH (60*60*24) |
How old can a router get before we (as a server) will no longer consider it live? In seconds.
◆ ROUTER_PURPOSE_BRIDGE
| #define ROUTER_PURPOSE_BRIDGE 2 |
Tor should use this router only for bridge positions in circuits: we got it via a directory request from the bridge itself, or a bridge authority.
◆ ROUTER_PURPOSE_CONTROLLER
| #define ROUTER_PURPOSE_CONTROLLER 1 |
Tor should avoid using this router for circuit-building: we got it from a controller. If the controller wants to use it, it'll have to ask for it by identity.
◆ ROUTER_PURPOSE_GENERAL
| #define ROUTER_PURPOSE_GENERAL 0 |
Tor can use this router for general positions in circuits; we got it from a directory server as usual, or we're an authority and a server uploaded it.
◆ ROUTER_PURPOSE_UNKNOWN
| #define ROUTER_PURPOSE_UNKNOWN 255 |
Tor should not use this router; it was marked in cached-descriptors with a purpose we didn't recognize.
◆ SESSION_GROUP_CONTROL_RESOLVE
| #define SESSION_GROUP_CONTROL_RESOLVE -3 |
Session group reserved for resolve requests launched by a controller
◆ SESSION_GROUP_DIRCONN
| #define SESSION_GROUP_DIRCONN -2 |
Session group reserved for directory connections
◆ SESSION_GROUP_FIRST_AUTO
| #define SESSION_GROUP_FIRST_AUTO -4 |
First automatically allocated session group number
◆ SESSION_GROUP_UNSET
| #define SESSION_GROUP_UNSET -1 |
Indicates that we haven't yet set a session group on a port_cfg_t.
◆ SOCKS4_NETWORK_LEN
| #define SOCKS4_NETWORK_LEN 8 |
Number of bytes in a SOCKS4 header.
◆ SOCKS_COMMAND_CONNECT
| #define SOCKS_COMMAND_CONNECT 0x01 |
Please open a TCP connection to this addr:port.
◆ SOCKS_COMMAND_IS_RESOLVE
| #define SOCKS_COMMAND_IS_RESOLVE | ( | c | ) |
◆ SOCKS_COMMAND_RESOLVE
| #define SOCKS_COMMAND_RESOLVE 0xF0 |
Please turn this FQDN into an IP address, privately.
◆ SOCKS_COMMAND_RESOLVE_PTR
| #define SOCKS_COMMAND_RESOLVE_PTR 0xF1 |
Please turn this IP address into an FQDN, privately.
◆ STREAMWINDOW_INCREMENT
| #define STREAMWINDOW_INCREMENT 50 |
Amount to increment a stream window when we get a stream SENDME.
◆ STREAMWINDOW_START
| #define STREAMWINDOW_START 500 |
Initial value on both sides of a stream transmission window when the stream is initialized. Measured in cells.
◆ TIMEOUT_UNTIL_UNREACHABILITY_COMPLAINT
| #define TIMEOUT_UNTIL_UNREACHABILITY_COMPLAINT (20*60) |
How long to test reachability before complaining to the user.
◆ TO_CIRCUIT
| #define TO_CIRCUIT | ( | x | ) | (&((x)->base_)) |
Convert a circuit subtype to a circuit_t.
◆ TO_CONN
| #define TO_CONN | ( | c | ) | (&(((c)->base_))) |
Cast a connection_t subtype pointer to a connection_t
◆ UNNAMED_ROUTER_NICKNAME
| #define UNNAMED_ROUTER_NICKNAME "Unnamed" |
Name chosen by routers that don't configure nicknames
◆ V3_AUTH_BODY_LEN
| #define V3_AUTH_BODY_LEN (V3_AUTH_FIXED_PART_LEN + 8 + 16) |
The length of the part of the AUTHENTICATE cell body that the client signs.
◆ V3_AUTH_FIXED_PART_LEN
| #define V3_AUTH_FIXED_PART_LEN (8+(32*6)) |
The length of the part of the AUTHENTICATE cell body that the client and server can generate independently (when using RSA_SHA256_TLSSECRET). It contains everything except the client's timestamp, the client's randomly generated nonce, and the signature.
◆ VAR_CELL_MAX_HEADER_SIZE
| #define VAR_CELL_MAX_HEADER_SIZE 7 |
Maximum length of a header on a variable-length cell.
Typedef Documentation
◆ addr_policy_t
| typedef struct addr_policy_t addr_policy_t |
A reference-counted address policy rule.
◆ authority_cert_t
| typedef struct authority_cert_t authority_cert_t |
Certificate for v3 directory protocol: binds long-term authority identity keys to medium-term authority signing keys.
◆ bandwidth_weight_rule_t
| typedef enum bandwidth_weight_rule_t bandwidth_weight_rule_t |
Possible ways to weight routers when choosing one randomly. See routerlist_sl_choose_by_bandwidth() for more information.
◆ build_time_t
| typedef uint32_t build_time_t |
A build_time_t is milliseconds
◆ buildtimeout_set_event_t
| typedef enum buildtimeout_set_event_t buildtimeout_set_event_t |
Used to indicate the type of a buildtime event
◆ cached_dir_t
| typedef struct cached_dir_t cached_dir_t |
A cached_dir_t represents a cacheable directory object, along with its compressed form.
◆ cell_queue_t
| typedef struct cell_queue_t cell_queue_t |
A queue of cells on a circuit, waiting to be added to the or_connection_t's outbuf.
◆ cell_t
Parsed onion routing cell. All communication between nodes is via cells.
◆ circid_t
| typedef uint32_t circid_t |
Identifies a circuit on an or_connection
◆ circuit_status_event_t
| typedef enum circuit_status_event_t circuit_status_event_t |
Used to indicate the type of a circuit event passed to the controller. The various types are defined in control-spec.txt
◆ circuit_status_minor_event_t
| typedef enum circuit_status_minor_event_t circuit_status_minor_event_t |
Used to indicate the type of a CIRC_MINOR event passed to the controller. The various types are defined in control-spec.txt .
◆ circuit_t
A circuit is a path over the onion routing network. Applications can connect to one end of the circuit, and can create exit connections at the other end of the circuit. AP and exit connections have only one circuit associated with them (and thus these connection types are closed when the circuit is closed), whereas OR connections multiplex many circuits at once, and stay standing even when there are no circuits running over them.
A circuit_t structure can fill one of two roles. First, a or_circuit_t links two connections together: either an edge connection and an OR connection, or two OR connections. (When joined to an OR connection, a circuit_t affects only cells sent to a particular circID on that connection. When joined to an edge connection, a circuit_t affects all data.)
Second, an origin_circuit_t holds the cipher keys and state for sending data along a given circuit. At the OP, it has a sequence of ciphers, each of which is shared with a single OR along the circuit. Separate ciphers are used for data going "forward" (away from the OP) and "backward" (towards the OP). At the OR, a circuit has only two stream ciphers: one for data going forward, and one for data going backward.
◆ connection_t
| typedef struct connection_t connection_t |
Description of a connection to another host or process, and associated data.
A connection is named based on what it's connected to – an "OR connection" has a Tor node on the other end, an "exit connection" has a website or other server on the other end, and an "AP connection" has an application proxy (and thus a user) on the other end.
Every connection has a type and a state. Connections never change their type, but can go through many state changes in their lifetime.
Every connection has two associated input and output buffers. Listeners don't use them. For non-listener connections, incoming data is appended to conn->inbuf, and outgoing data is taken from conn->outbuf. Connections differ primarily in the functions called to fill and drain these buffers.
◆ control_connection_t
| typedef struct control_connection_t control_connection_t |
Subtype of connection_t for an connection to a controller.
◆ country_t
| typedef int16_t country_t |
A signed integer representing a country code.
◆ crypt_path_t
| typedef struct crypt_path_t crypt_path_t |
Holds accounting information for a single step in the layered encryption performed by a circuit. Used only at the client edge of a circuit.
◆ desc_store_t
| typedef struct desc_store_t desc_store_t |
A 'store' is a set of descriptors saved on disk, with accompanying journal, mmaped as needed, rebuilt as needed.
◆ destroy_cell_queue_t
| typedef struct destroy_cell_queue_t destroy_cell_queue_t |
A queue of destroy cells on a channel.
◆ destroy_cell_t
| typedef struct destroy_cell_t destroy_cell_t |
A single queued destroy cell.
◆ dir_connection_t
| typedef struct dir_connection_t dir_connection_t |
Subtype of connection_t for an "directory connection" – that is, an HTTP connection to retrieve or serve directory material.
◆ dir_server_t
| typedef struct dir_server_t dir_server_t |
Represents information about a single trusted or fallback directory server.
◆ document_signature_t
| typedef struct document_signature_t document_signature_t |
A signature of some document by an authority.
◆ download_status_t
| typedef struct download_status_t download_status_t |
Information about our plans for retrying downloads for a downloadable directory object. Each type of downloadable directory object has a corresponding retry schedule, which can be different depending on whether the object is being downloaded from an authority or a mirror (want_authority). next_attempt_at contains the next time we will attempt to download the object. For schedules that increment_on failure, n_download_failures is used to determine the position in the schedule. (Each schedule is a smartlist of integer delays, parsed from a CSV option.) Every time a connection attempt fails, n_download_failures is incremented, the new delay value is looked up from the schedule, and next_attempt_at is set delay seconds from the time the previous connection failed. Therefore, at most one failure-based connection can be in progress for each download_status_t. For schedules that increment_on attempt, n_download_attempts is used to determine the position in the schedule. Every time a connection attempt is made, n_download_attempts is incremented, the new delay value is looked up from the schedule, and next_attempt_at is set delay seconds from the time the previous connection was attempted. Therefore, multiple concurrent attempted-based connections can be in progress for each download_status_t. After an object is successfully downloaded, any other concurrent connections are terminated. A new schedule which starts at position 0 is used for subsequent downloads of the same object.
◆ edge_connection_t
| typedef struct edge_connection_t edge_connection_t |
Subtype of connection_t for an "edge connection" – that is, an entry (ap) connection, or an exit.
◆ entry_connection_t
| typedef struct entry_connection_t entry_connection_t |
Subtype of edge_connection_t for an "entry connection" – that is, a SOCKS connection, a DNS request, a TransPort connection or a NATD connection
◆ ext_or_cmd_t
| typedef struct ext_or_cmd_t ext_or_cmd_t |
A parsed Extended ORPort message.
◆ extend_info_t
| typedef struct extend_info_t extend_info_t |
Information on router used when extending a circuit. We don't need a full routerinfo_t to extend: we only need addr:port:keyid to build an OR connection, and onion_key to create the onionskin. Note that for onehop general-purpose tunnels, the onion_key is NULL.
◆ extrainfo_t
| typedef struct extrainfo_t extrainfo_t |
Information needed to keep and cache a signed extra-info document.
◆ listener_connection_t
| typedef struct listener_connection_t listener_connection_t |
Subtype of connection_t; used for a listener socket.
◆ microdesc_t
| typedef struct microdesc_t microdesc_t |
A microdescriptor is the smallest amount of information needed to build a circuit through a router. They are generated by the directory authorities, using information from the uploaded routerinfo documents. They are not self-signed, but are rather authenticated by having their hash in a signed networkstatus document.
◆ networkstatus_t
| typedef struct networkstatus_t networkstatus_t |
A common structure to hold a v3 network status vote, or a v3 network status consensus.
◆ networkstatus_voter_info_t
| typedef struct networkstatus_voter_info_t networkstatus_voter_info_t |
Information about a single voter in a vote or a consensus.
◆ node_t
A node_t represents a Tor router.
Specifically, a node_t is a Tor router as we are using it: a router that we are considering for circuits, connections, and so on. A node_t is a thin wrapper around the routerstatus, routerinfo, and microdesc for a single router, and provides a consistent interface for all of them.
Also, a node_t has mutable state. While a routerinfo, a routerstatus, and a microdesc have[*] only the information read from a router descriptor, a consensus entry, and a microdescriptor (respectively)... a node_t has flags based on our own current opinion of the node.
[*] Actually, there is some leftover information in each that is mutable. We should try to excise that.
◆ ns_detached_signatures_t
| typedef struct ns_detached_signatures_t ns_detached_signatures_t |
A set of signatures for a networkstatus consensus. Unless otherwise noted, all fields are as for networkstatus_t.
◆ or_circuit_t
| typedef struct or_circuit_t or_circuit_t |
An or_circuit_t holds information needed to implement a circuit at an OR.
◆ or_conn_status_event_t
| typedef enum or_conn_status_event_t or_conn_status_event_t |
Used to indicate the type of an OR connection event passed to the controller. The various types are defined in control-spec.txt
◆ or_connection_t
| typedef struct or_connection_t or_connection_t |
Subtype of connection_t for an "OR connection" – that is, one that speaks cells over TLS.
◆ or_handshake_certs_t
| typedef struct or_handshake_certs_t or_handshake_certs_t |
Structure to hold all the certificates we've received on an OR connection
◆ or_handshake_state_t
| typedef struct or_handshake_state_t or_handshake_state_t |
Stores flags and information related to the portion of a v2/v3 Tor OR connection handshake that happens after the TLS handshake is finished.
◆ origin_circuit_t
| typedef struct origin_circuit_t origin_circuit_t |
An origin_circuit_t holds data necessary to build and use a circuit.
◆ packed_cell_t
| typedef struct packed_cell_t packed_cell_t |
A cell as packed for writing to the network.
◆ port_cfg_t
| typedef struct port_cfg_t port_cfg_t |
Configuration for a single port that we're listening on.
◆ protover_summary_flags_t
| typedef struct protover_summary_flags_t protover_summary_flags_t |
Flags used to summarize the declared protocol versions of a relay, so we don't need to parse them again and again.
◆ rend_auth_type_t
| typedef enum rend_auth_type_t rend_auth_type_t |
Client authorization type that a hidden service performs.
◆ rend_authorized_client_t
| typedef struct rend_authorized_client_t rend_authorized_client_t |
Hidden-service side configuration of client authorization.
◆ rend_data_t
| typedef struct rend_data_t rend_data_t |
Client- and server-side data that is used for hidden service connection establishment. Not all fields contain data depending on where this struct is used.
◆ rend_encoded_v2_service_descriptor_t
ASCII-encoded v2 hidden service descriptor.
◆ rend_intro_point_t
| typedef struct rend_intro_point_t rend_intro_point_t |
Introduction point information. Used both in rend_service_t (on the service side) and in rend_service_descriptor_t (on both the client and service side).
◆ rend_service_authorization_t
| typedef struct rend_service_authorization_t rend_service_authorization_t |
Client-side configuration of authorization for a hidden service.
◆ rend_service_descriptor_t
| typedef struct rend_service_descriptor_t rend_service_descriptor_t |
Information used to connect to a hidden service. Used on both the service side and the client side.
◆ routerstatus_t
| typedef struct routerstatus_t routerstatus_t |
Contents of a single router entry in a network status object.
◆ setopt_err_t
| typedef enum setopt_err_t setopt_err_t |
An error from options_trial_assign() or options_init_from_string().
◆ short_policy_entry_t
| typedef struct short_policy_entry_t short_policy_entry_t |
A single entry in a parsed policy summary, describing a range of ports.
◆ short_policy_t
| typedef struct short_policy_t short_policy_t |
A short_poliy_t is the parsed version of a policy summary.
◆ signed_descriptor_t
| typedef struct signed_descriptor_t signed_descriptor_t |
Information need to cache an onion router's descriptor.
◆ store_type_t
| typedef enum store_type_t store_type_t |
Allowable types of desc_store_t.
◆ stream_status_event_t
| typedef enum stream_status_event_t stream_status_event_t |
Used to indicate the type of a stream event passed to the controller. The various types are defined in control-spec.txt
◆ streamid_t
| typedef uint16_t streamid_t |
Identifies a stream on a circuit
◆ testing_cell_stats_entry_t
| typedef struct testing_cell_stats_entry_t testing_cell_stats_entry_t |
Entry in the cell stats list of a circuit; used only if CELL_STATS events are enabled.
◆ tor_version_t
| typedef struct tor_version_t tor_version_t |
Structure to hold parsed Tor versions. This is a little messier than we would like it to be, because we changed version schemes with 0.1.0.
See version-spec.txt for the whole business.
◆ var_cell_t
| typedef struct var_cell_t var_cell_t |
Parsed variable-length onion routing cell.
◆ version_status_t
| typedef enum version_status_t version_status_t |
Possible statuses of a version of Tor, given opinions from the directory servers.
◆ vote_microdesc_hash_t
| typedef struct vote_microdesc_hash_t vote_microdesc_hash_t |
Linked list of microdesc hash lines for a single router in a directory vote.
◆ vote_routerstatus_t
| typedef struct vote_routerstatus_t vote_routerstatus_t |
The claim about a single router, made in a vote.
◆ vote_timing_t
| typedef struct vote_timing_t vote_timing_t |
Describes the schedule by which votes should be generated.
◆ was_router_added_t
| typedef enum was_router_added_t was_router_added_t |
Return value for router_add_to_routerlist() and dirserv_add_descriptor()
Enumeration Type Documentation
◆ addr_policy_action_t
| enum addr_policy_action_t |
What action type does an address policy indicate: accept or reject?
◆ addr_policy_result_t
| enum addr_policy_result_t |
Outcome of applying an address policy to an address.
◆ addressmap_entry_source_t
Enumerates possible origins of a client-side address mapping.
◆ bandwidth_weight_rule_t
Possible ways to weight routers when choosing one randomly. See routerlist_sl_choose_by_bandwidth() for more information.
◆ bootstrap_status_t
| enum bootstrap_status_t |
Enum describing various stages of bootstrapping, for use with controller bootstrap status events. The values range from 0 to 100.
◆ buildtimeout_set_event_t
Used to indicate the type of a buildtime event
◆ cell_direction_t
| enum cell_direction_t |
◆ circ_id_type_t
| enum circ_id_type_t |
◆ circuit_status_event_t
Used to indicate the type of a circuit event passed to the controller. The various types are defined in control-spec.txt
◆ circuit_status_minor_event_t
Used to indicate the type of a CIRC_MINOR event passed to the controller. The various types are defined in control-spec.txt .
◆ consensus_flavor_t
| enum consensus_flavor_t |
Enumerates recognized flavors of a consensus networkstatus document. All flavors of a consensus are generated from the same set of votes, but they present different types information to different versions of Tor.
◆ dirinfo_type_t
| enum dirinfo_type_t |
Bitfield enum type listing types of information that directory authorities can be authoritative about, and that directory caches may or may not cache.
Note that the granularity here is based on authority granularity and on cache capabilities. Thus, one particular bit may correspond in practice to a few types of directory info, so long as every authority that pronounces officially about one of the types prounounces officially about all of them, and so long as every cache that caches one of them caches all of them.
◆ dirreq_state_t
| enum dirreq_state_t |
Possible states for either direct or tunneled directory requests that are relevant for determining network status download times.
◆ dirreq_type_t
| enum dirreq_type_t |
Directory requests that we are measuring can be either direct or tunneled.
◆ download_schedule_increment_t
Enumeration: do we want to increment the schedule position each time a connection is attempted (these attempts can be concurrent), or do we want to increment the schedule position after a connection fails?
◆ download_schedule_t
| enum download_schedule_t |
Enumeration: what directory object is being downloaded? This determines which schedule is selected to perform the download.
◆ download_want_authority_t
Enumeration: is the download schedule for downloading from an authority, or from any available directory mirror? During bootstrap, "any" means a fallback (or an authority, if there are no fallbacks). When we have a valid consensus, "any" means any directory server.
◆ geoip_client_action_t
Indicates an action that we might be noting geoip statistics on. Note that if we're noticing CONNECT, we're a bridge, and if we're noticing the others, we're not.
| Enumerator | |
|---|---|
| GEOIP_CLIENT_CONNECT | We've noticed a connection as a bridge relay or entry guard. |
| GEOIP_CLIENT_NETWORKSTATUS | We've served a networkstatus consensus as a directory server. |
◆ geoip_ns_response_t
| enum geoip_ns_response_t |
Indicates either a positive reply or a reason for rejectng a network status request that will be included in geoip statistics.
◆ networkstatus_type_t
| enum networkstatus_type_t |
Enumerates the possible seriousness values of a networkstatus document.
◆ or_conn_status_event_t
Used to indicate the type of an OR connection event passed to the controller. The various types are defined in control-spec.txt
◆ outbound_addr_t
| enum outbound_addr_t |
Enumeration of outbound address configuration types: Exit-only, OR-only, or both
◆ path_state_t
| enum path_state_t |
Describes the circuit building process in simplified terms based on the path bias accounting state for a circuit.
NOTE: These state values are enumerated in the order for which we expect circuits to transition through them. If you add states, you need to preserve this overall ordering. The various pathbias state transition and accounting functions (pathbias_mark_* and pathbias_count_*) contain ordinal comparisons to enforce proper state transitions for corrections.
This state machine and the associated logic was created to prevent miscounting due to unknown cases of circuit reuse. See also tickets #6475 and #7802.
| Enumerator | |
|---|---|
| PATH_STATE_NEW_CIRC | This circuit is "new". It has not yet completed a first hop or been counted by the path bias code. |
| PATH_STATE_BUILD_ATTEMPTED | This circuit has completed one/two hops, and has been counted by the path bias logic. |
| PATH_STATE_BUILD_SUCCEEDED | This circuit has been completely built |
| PATH_STATE_USE_ATTEMPTED | Did we try to attach any SOCKS streams or hidserv introductions to this circuit? Note: If we ever implement end-to-end stream timing through test stream probes (#5707), we must not set this for those probes (or any other automatic streams) because the adversary could just tag at a later point. |
| PATH_STATE_USE_SUCCEEDED | Did any SOCKS streams or hidserv introductions actually succeed on this circuit? If any streams detatch/fail from this circuit, the code transitions the circuit back to PATH_STATE_USE_ATTEMPTED to ensure we probe. See pathbias_mark_use_rollback() for that. |
| PATH_STATE_USE_FAILED | This is a special state to indicate that we got a corrupted relay cell on a circuit and we don't intend to probe it. |
| PATH_STATE_ALREADY_COUNTED | This is a special state to indicate that we already counted the circuit. Used to guard against potential state machine violations. |
◆ pk_op_t
| enum pk_op_t |
Possible public/private key operations in Tor: used to keep track of where we're spending our time.
◆ rend_auth_type_t
| enum rend_auth_type_t |
Client authorization type that a hidden service performs.
◆ router_crn_flags_t
| enum router_crn_flags_t |
Flags to be passed to control router_choose_random_node() to indicate what kind of nodes to pick according to what algorithm.
◆ routerstatus_format_type_t
An enum to describe what format we're generating a routerstatus line in.
◆ saved_location_t
| enum saved_location_t |
Enum used to remember where a signed_descriptor_t is stored and how to manage the memory for signed_descriptor_body.
◆ setopt_err_t
| enum setopt_err_t |
An error from options_trial_assign() or options_init_from_string().
◆ store_type_t
| enum store_type_t |
Allowable types of desc_store_t.
◆ stream_status_event_t
Used to indicate the type of a stream event passed to the controller. The various types are defined in control-spec.txt
◆ version_status_t
| enum version_status_t |
Possible statuses of a version of Tor, given opinions from the directory servers.
◆ was_router_added_t
| enum was_router_added_t |
Return value for router_add_to_routerlist() and dirserv_add_descriptor()
Function Documentation
◆ circuit_build_times_initial_timeout()
| int32_t circuit_build_times_initial_timeout | ( | void | ) |
Retrieve and bounds-check the cbtinitialtimeout consensus parameter.
Effect: This is the timeout value to use before computing a timeout, in milliseconds.
◆ circuit_build_times_quantile_cutoff()
| double circuit_build_times_quantile_cutoff | ( | void | ) |
Retrieve and bounds-check the cbtquantile consensus parameter.
Effect: This is the position on the quantile curve to use to set the timeout value. It is a percent (10-99).
 1.8.13
1.8.13