#include <or.h>
Detailed Description
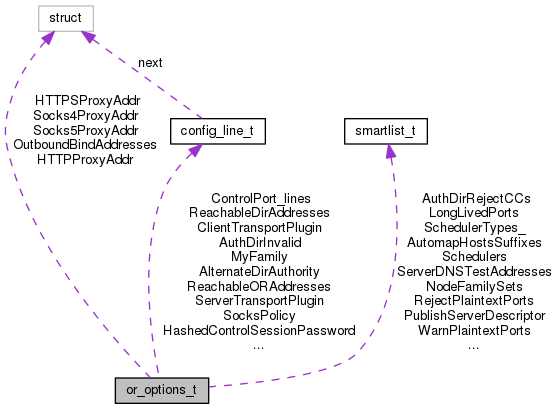
Configuration options for a Tor process.
Member Enumeration Documentation
◆ anonymous enum
| anonymous enum |
What should the tor process actually do?
◆ anonymous enum
| anonymous enum |
Parsed value of TransProxyType.
Field Documentation
◆ AccelDir
| char* AccelDir |
Optional hardware acceleration engine search dir.
◆ AccelName
| char* AccelName |
Optional hardware acceleration engine name.
◆ AccountingMax
| uint64_t AccountingMax |
How many bytes do we allow per accounting interval before hibernation? 0 for "never hibernate."
◆ AccountingRule_option
| char* AccountingRule_option |
How do we determine when our AccountingMax has been reached? "max" for when in or out reaches AccountingMax "sum" for when in plus out reaches AccountingMax "in" for when in reaches AccountingMax "out" for when out reaches AccountingMax
◆ AccountingStart
| char* AccountingStart |
How long is the accounting interval, and when does it start?
◆ Address
| char* Address |
OR only: configured address for this onion router.
◆ AddressMap
| config_line_t* AddressMap |
List of address map directives.
◆ AllDirActionsPrivate
| int AllDirActionsPrivate |
Should every directory action be sent through a Tor circuit?
◆ AllowNonRFC953Hostnames
| int AllowNonRFC953Hostnames |
If true, we allow connections to hostnames with weird characters.
◆ AlternateBridgeAuthority
| config_line_t* AlternateBridgeAuthority |
If set, use these bridge authorities and not the default one.
◆ AlternateDirAuthority
| config_line_t* AlternateDirAuthority |
If set, use these main (currently v3) directory authorities and not the default ones.
◆ AndroidIdentityTag
| char* AndroidIdentityTag |
Identity tag to add for Android logging.
◆ AssumeReachable
| int AssumeReachable |
Whether to publish our descriptor regardless.
◆ AuthDirBadExit
| config_line_t* AuthDirBadExit |
Address policy for descriptors to mark as bad exits.
◆ AuthDirFastGuarantee
| uint64_t AuthDirFastGuarantee |
If non-zero, always vote the Fast flag for any relay advertising this amount of capacity or more.
◆ AuthDirGuardBWGuarantee
| uint64_t AuthDirGuardBWGuarantee |
If non-zero, this advertised capacity or more is always sufficient to satisfy the bandwidth requirement for the Guard flag.
◆ AuthDirHasIPv6Connectivity
| int AuthDirHasIPv6Connectivity |
Boolean: are we on IPv6?
◆ AuthDirInvalid
| config_line_t* AuthDirInvalid |
Address policy for descriptors to never mark as valid.
◆ AuthDirListBadExits
| int AuthDirListBadExits |
True iff we should list bad exits, and vote for all other exits as good.
◆ AuthDirMaxServersPerAddr
| int AuthDirMaxServersPerAddr |
Do not permit more than this number of servers per IP address.
◆ AuthDirPinKeys
| int AuthDirPinKeys |
Boolean: Do we enforce key-pinning?
◆ AuthDirReject
| config_line_t* AuthDirReject |
Address policy for descriptors to reject.
◆ AuthDirSharedRandomness
| int AuthDirSharedRandomness |
Bool (default: 1): Switch for the shared random protocol. Only relevant to a directory authority. If off, the authority won't participate in the protocol. If on (default), a flag is added to the vote indicating participation.
◆ AuthDirTestEd25519LinkKeys
| int AuthDirTestEd25519LinkKeys |
Bool (default: 1): When testing routerinfos as a directory authority, do we enforce Ed25519 identity match?
◆ AuthoritativeDir
| int AuthoritativeDir |
Boolean: is this an authoritative directory?
◆ AutomapHostsOnResolve
| int AutomapHostsOnResolve |
If true, when we get a resolve request for a hostname ending with one of the suffixes in AutomapHostsSuffixes, map it to a virtual address.
◆ AutomapHostsSuffixes
| smartlist_t* AutomapHostsSuffixes |
List of suffixes for AutomapHostsOnResolve. The special value "." means "match everything."
◆ AvoidDiskWrites
| int AvoidDiskWrites |
Boolean: should we never cache things to disk? Not used yet.
◆ BandwidthBurst
| uint64_t BandwidthBurst |
How much bandwidth, at maximum, are we willing to use in a second?
◆ BandwidthRate
| uint64_t BandwidthRate |
How much bandwidth, on average, are we willing to use in a second?
◆ BridgeAuthoritativeDir
| int BridgeAuthoritativeDir |
Boolean: is this an authoritative directory that aggregates bridge descriptors?
◆ BridgeDistribution
| char* BridgeDistribution |
If set on a bridge relay, it will include this value on a new "bridge-distribution-request" line in its bridge descriptor.
◆ BridgePassword
| char* BridgePassword |
If set on a bridge authority, it will answer requests on its dirport for bridge statuses – but only if the requests use this password.
◆ BridgePassword_AuthDigest_
| char* BridgePassword_AuthDigest_ |
If BridgePassword is set, this is a SHA256 digest of the basic http authenticator for it. Used so we can do a time-independent comparison.
◆ BridgeRecordUsageByCountry
| int BridgeRecordUsageByCountry |
If true, and we have GeoIP data, and we're a bridge, keep a per-country count of how many client addresses have contacted us so that we can help the bridge authority guess which countries have blocked access to us.
◆ BridgeRelay
| int BridgeRelay |
Boolean: are we acting as a bridge relay? We make this explicit so we can change how we behave in the future.
◆ Bridges
| config_line_t* Bridges |
List of bootstrap bridge addresses.
◆ CacheDirectory
| char* CacheDirectory |
Where to store cached data, as modified.
◆ CacheDirectory_option
| char* CacheDirectory_option |
Where to store cached data, as configured by the user.
◆ CacheDirectoryGroupReadable
| int CacheDirectoryGroupReadable |
Boolean: Is the CacheDirectory g+r?
◆ CellStatistics
| int CellStatistics |
If true, the user wants us to collect cell statistics.
◆ CircuitBuildTimeout
| int CircuitBuildTimeout |
Cull non-open circuits that were born at least this many seconds ago. Used until adaptive algorithm learns a new value.
◆ CircuitsAvailableTimeout
| int CircuitsAvailableTimeout |
Try to have an open circuit for at least this long after last activity
◆ CircuitStreamTimeout
| int CircuitStreamTimeout |
If non-zero, detach streams from circuits and try a new circuit if the stream has been waiting for this many seconds. If zero, use our default internal timeout schedule.
◆ ClientBootstrapConsensusAuthorityDownloadInitialDelay
| int ClientBootstrapConsensusAuthorityDownloadInitialDelay |
Schedule for when clients should download consensuses from authorities if they are bootstrapping (that is, they don't have a usable, reasonably live consensus). Only used by clients fetching from a list of fallback directory mirrors.
This schedule is incremented by (potentially concurrent) connection attempts, unlike other schedules, which are incremented by connection failures. Only altered on testing networks.
◆ ClientBootstrapConsensusAuthorityOnlyDownloadInitialDelay
| int ClientBootstrapConsensusAuthorityOnlyDownloadInitialDelay |
Schedule for when clients should download consensuses from authorities if they are bootstrapping (that is, they don't have a usable, reasonably live consensus). Only used by clients which don't have or won't fetch from a list of fallback directory mirrors.
This schedule is incremented by (potentially concurrent) connection attempts, unlike other schedules, which are incremented by connection failures. Only altered on testing networks.
◆ ClientBootstrapConsensusFallbackDownloadInitialDelay
| int ClientBootstrapConsensusFallbackDownloadInitialDelay |
Schedule for when clients should download consensuses from fallback directory mirrors if they are bootstrapping (that is, they don't have a usable, reasonably live consensus). Only used by clients fetching from a list of fallback directory mirrors.
This schedule is incremented by (potentially concurrent) connection attempts, unlike other schedules, which are incremented by connection failures. Only altered on testing networks.
◆ ClientBootstrapConsensusMaxInProgressTries
| int ClientBootstrapConsensusMaxInProgressTries |
How many simultaneous in-progress connections will we make when trying to fetch a consensus before we wait for one to complete, timeout, or error out? Only altered on testing networks.
◆ ClientDNSRejectInternalAddresses
| int ClientDNSRejectInternalAddresses |
If true, do not believe anybody who tells us that a domain resolves to an internal address, or that an internal address has a PTR mapping. Helps avoid some cross-site attacks.
◆ ClientOnly
| int ClientOnly |
Boolean: should we never evolve into a server role?
◆ ClientPreferIPv6DirPort
| int ClientPreferIPv6DirPort |
If true, prefer an IPv6 directory port over an IPv4 one for direct directory connections. If auto, bridge clients prefer IPv6, and other clients prefer IPv4. Use fascist_firewall_prefer_ipv6_dirport() instead of accessing this value directly.
◆ ClientPreferIPv6ORPort
| int ClientPreferIPv6ORPort |
If true, prefer an IPv6 OR port over an IPv4 one for entry node connections. If auto, bridge clients prefer IPv6, and other clients prefer IPv4. Use node_ipv6_or_preferred() instead of accessing this value directly.
◆ ClientRejectInternalAddresses
| int ClientRejectInternalAddresses |
If true, do not accept any requests to connect to internal addresses over randomly chosen exits.
◆ ClientTransportPlugin
| config_line_t* ClientTransportPlugin |
List of client transport plugins.
◆ ClientUseIPv4
| int ClientUseIPv4 |
If true, clients may connect over IPv4. If false, they will avoid connecting over IPv4. We enforce this for OR and Dir connections.
◆ ClientUseIPv6
| int ClientUseIPv6 |
If true, clients may connect over IPv6. If false, they will avoid connecting over IPv4. We enforce this for OR and Dir connections. Use fascist_firewall_use_ipv6() instead of accessing this value directly.
◆ command
| enum { ... } command |
What should the tor process actually do?
◆ command_arg
| char* command_arg |
Argument for command-line option.
◆ ConnDirectionStatistics
| int ConnDirectionStatistics |
If true, the user wants us to collect connection statistics.
◆ ConnectionPadding
| int ConnectionPadding |
Autobool: if auto, then connection padding will be negotiated by client and server. If 0, it will be fully disabled. If 1, the client will still pad to the server regardless of server support.
◆ ConnLimit
| int ConnLimit |
Demanded minimum number of simultaneous connections.
◆ ConnLimit_
| int ConnLimit_ |
Maximum allowed number of simultaneous connections.
◆ ConnLimit_high_thresh
| int ConnLimit_high_thresh |
start trying to lower socket usage if we have this many.
◆ ConnLimit_low_thresh
| int ConnLimit_low_thresh |
try to get down to here after socket exhaustion.
◆ ConsensusParams
| char* ConsensusParams |
Authority only: key=value pairs that we add to our networkstatus consensus vote on the 'params' line.
◆ ConstrainedSockets
| int ConstrainedSockets |
Shrink xmit and recv socket buffers.
◆ ConstrainedSockSize
| uint64_t ConstrainedSockSize |
Size of constrained buffers.
◆ ContactInfo
| char* ContactInfo |
Contact info to be published in the directory.
◆ ControlPort_lines
| config_line_t* ControlPort_lines |
Ports to listen on for control connections.
◆ ControlPortFileGroupReadable
| int ControlPortFileGroupReadable |
Should that file be group-readable?
◆ ControlPortWriteToFile
| char* ControlPortWriteToFile |
File where we should write the ControlPort.
◆ ControlSocket
| config_line_t* ControlSocket |
List of Unix Domain Sockets to listen on for control connections.
◆ ControlSocketsGroupWritable
| int ControlSocketsGroupWritable |
Boolean: Are control sockets g+rw?
◆ CookieAuthentication
| int CookieAuthentication |
Boolean: do we enable cookie-based auth for the control system?
◆ CookieAuthFile
| char* CookieAuthFile |
Filesystem location of a ControlPort authentication cookie.
◆ CookieAuthFileGroupReadable
| int CookieAuthFileGroupReadable |
Boolean: Is the CookieAuthFile g+r?
◆ CountPrivateBandwidth
| int CountPrivateBandwidth |
Boolean: if set, then even connections to private addresses will get rate-limited.
◆ DataDirectory
| char* DataDirectory |
Where to store long-term data, as modified.
◆ DataDirectory_option
| char* DataDirectory_option |
Where to store long-term data, as configured by the user.
◆ DataDirectoryGroupReadable
| int DataDirectoryGroupReadable |
Boolean: Is the DataDirectory g+r?
◆ DebugLogFile
| char* DebugLogFile |
Where to send verbose log messages.
◆ DirAllowPrivateAddresses
| int DirAllowPrivateAddresses |
Whether dirservers allow router descriptors with private IPs.
◆ DirAuthorities
| config_line_t* DirAuthorities |
List of configuration lines for replacement directory authorities. If you just want to replace one class of authority at a time, use the "Alternate*Authority" options below instead.
◆ DirAuthorityFallbackRate
| double DirAuthorityFallbackRate |
Weight to apply to all directory authority rates if considering them along with fallbackdirs
◆ DirCache
| int DirCache |
Cache all directory documents and accept requests via tunnelled dir conns from clients. If 1, enabled (default); If 0, disabled.
◆ DirPolicy
| config_line_t* DirPolicy |
Lists of dir policy components
◆ DirPort_lines
| config_line_t* DirPort_lines |
Ports to listen on for directory connections.
◆ DirPortFrontPage
| char* DirPortFrontPage |
This is a full path to a file with an html disclaimer. This allows a server administrator to show that they're running Tor and anyone visiting their server will know this without any specialized knowledge.
◆ DirReqStatistics
| int DirReqStatistics |
Internal variable to remember whether we're actually acting on DirReqStatistics_option – yes if it's set and we're a server, else no.
◆ DirReqStatistics_option
| int DirReqStatistics_option |
If true, we're configured to collect statistics on clients requesting network statuses from us as directory.
◆ DisableAllSwap
| int DisableAllSwap |
Boolean: Attempt to call mlockall() on our process for all current and future memory.
◆ DisableDebuggerAttachment
| int DisableDebuggerAttachment |
Currently Linux only specific attempt to disable ptrace; needs BSD testing.
◆ DisableNetwork
| int DisableNetwork |
If 1, we accept and launch no external network connections, except on control ports.
◆ DisableOOSCheck
| int DisableOOSCheck |
If 1, we skip all OOS checks.
◆ DisablePredictedCircuits
| int DisablePredictedCircuits |
Boolean: does Tor preemptively make circuits in the background (0), or not (1)?
◆ DisableSignalHandlers
| int DisableSignalHandlers |
If true, Tor shouldn't install any posix signal handlers, since it is running embedded inside another process.
◆ DNSPort_lines
| config_line_t* DNSPort_lines |
Ports to listen on for DNS requests.
◆ DoSCircuitCreationBurst
| int DoSCircuitCreationBurst |
Maximum allowed burst of circuits. Reaching that value, the address is detected as malicious and a defense might be used.
◆ DoSCircuitCreationDefenseTimePeriod
| int DoSCircuitCreationDefenseTimePeriod |
For how much time (in seconds) the defense is applicable for a malicious address. A random time delta is added to the defense time of an address which will be between 1 second and half of this value.
◆ DoSCircuitCreationDefenseType
| int DoSCircuitCreationDefenseType |
When an address is marked as malicous, what defense should be used against it. See the dos_cc_defense_type_t enum.
◆ DoSCircuitCreationEnabled
| int DoSCircuitCreationEnabled |
Autobool: Is the circuit creation DoS mitigation subsystem enabled?
◆ DoSCircuitCreationMinConnections
| int DoSCircuitCreationMinConnections |
Minimum concurrent connection needed from one single address before any defense is used.
◆ DoSCircuitCreationRate
| int DoSCircuitCreationRate |
Circuit rate used to refill the token bucket.
◆ DoSConnectionDefenseType
| int DoSConnectionDefenseType |
When an address is reaches the maximum count, what defense should be used against it. See the dos_conn_defense_type_t enum.
◆ DoSConnectionEnabled
| int DoSConnectionEnabled |
Autobool: Is the DoS connection mitigation subsystem enabled?
◆ DoSConnectionMaxConcurrentCount
| int DoSConnectionMaxConcurrentCount |
Maximum concurrent connection allowed per address.
◆ DoSRefuseSingleHopClientRendezvous
| int DoSRefuseSingleHopClientRendezvous |
Autobool: Do we refuse single hop client rendezvous?
◆ DownloadExtraInfo
| int DownloadExtraInfo |
If true, we try to download extra-info documents (and we serve them, if we are a cache). For authorities, this is always true.
◆ EnforceDistinctSubnets
| int EnforceDistinctSubnets |
If true, don't allow multiple routers in the same network zone in the same circuit.
◆ EntryNodes
| routerset_t* EntryNodes |
Structure containing nicknames, digests, country codes and IP address patterns of ORs to consider as entry points.
◆ EntryStatistics
| int EntryStatistics |
If true, the user wants us to collect statistics as entry node.
◆ ExcludeExitNodes
| routerset_t* ExcludeExitNodes |
Structure containing nicknames, digests, country codes and IP address patterns of ORs not to consider as exits.
◆ ExcludeExitNodesUnion_
| routerset_t* ExcludeExitNodesUnion_ |
Union of ExcludeNodes and ExcludeExitNodes
◆ ExcludeNodes
| routerset_t* ExcludeNodes |
Structure containing nicknames, digests, country codes and IP address patterns of ORs not to use in circuits. But see StrictNodes above.
◆ ExitNodes
| routerset_t* ExitNodes |
Structure containing nicknames, digests, country codes and IP address patterns of ORs to consider as exits.
◆ ExitPolicy
| config_line_t* ExitPolicy |
Lists of exit policy components.
◆ ExitPolicyRejectLocalInterfaces
| int ExitPolicyRejectLocalInterfaces |
Should we not exit to local interface addresses? Includes OutboundBindAddresses and configured ports.
◆ ExitPolicyRejectPrivate
| int ExitPolicyRejectPrivate |
Should we not exit to reserved private addresses, and our own published addresses?
◆ ExitPortStatistics
| int ExitPortStatistics |
If true, the user wants us to collect statistics on port usage.
◆ ExitRelay
| int ExitRelay |
Is this an exit node? This is a tristate, where "1" means "yes, and use the default exit policy if none is given" and "0" means "no; exit policy is 'reject *'" and "auto" (-1) means "same as 1, but warn the user."
XXXX Eventually, the default will be 0.
◆ ExtendAllowPrivateAddresses
| int ExtendAllowPrivateAddresses |
Whether routers accept EXTEND cells to routers with private IPs.
◆ ExtendByEd25519ID
| int ExtendByEd25519ID |
Autobool: Should we include Ed25519 identities in extend2 cells? If -1, we should do whatever the consensus parameter says.
◆ ExtORPort_lines
| config_line_t* ExtORPort_lines |
Ports to listen on for extended OR connections.
◆ ExtORPortCookieAuthFile
| char* ExtORPortCookieAuthFile |
Filesystem location of Extended ORPort authentication cookie.
◆ ExtORPortCookieAuthFileGroupReadable
| int ExtORPortCookieAuthFileGroupReadable |
Boolean: Is the ExtORPortCookieAuthFile g+r?
◆ ExtraInfoStatistics
| int ExtraInfoStatistics |
If true, include statistics file contents in extra-info documents.
◆ FallbackDir
| config_line_t* FallbackDir |
List of fallback directory servers
◆ FascistFirewall
| int FascistFirewall |
Whether to prefer ORs reachable on open ports.
◆ FetchDirInfoEarly
| int FetchDirInfoEarly |
Should we always fetch our dir info on the mirror schedule (which means directly from the authorities) no matter our other config?
◆ FetchDirInfoExtraEarly
| int FetchDirInfoExtraEarly |
Should we fetch our dir info at the start of the consensus period?
◆ FetchHidServDescriptors
| int FetchHidServDescriptors |
and hidden service descriptors?
◆ FetchServerDescriptors
| int FetchServerDescriptors |
Do we fetch server descriptors as normal?
◆ FetchUselessDescriptors
| int FetchUselessDescriptors |
Do we fetch non-running descriptors too?
◆ FilesOpenedByIncludes
| smartlist_t* FilesOpenedByIncludes |
List of files that were opened by include in torrc and torrc-defaults
◆ FirewallPorts
| smartlist_t* FirewallPorts |
Which ports our firewall allows (strings).
◆ GeoIPExcludeUnknown
| int GeoIPExcludeUnknown |
Autobool: if auto, then any attempt to Exclude{Exit,}Nodes a particular country code will exclude all nodes in ?? and A1. If true, all nodes in ?? and A1 are excluded. Has no effect if we don't know any GeoIP data.
◆ GeoIPFile
| char* GeoIPFile |
Optionally, IPv4 and IPv6 GeoIP data.
◆ GuardfractionFile
| char* GuardfractionFile |
Location of guardfraction file
◆ GuardLifetime
| int GuardLifetime |
How long (seconds) do we keep a guard before picking a new one?
◆ HardwareAccel
| int HardwareAccel |
Boolean: Should we enable OpenSSL hardware acceleration where available?
◆ HashedControlPassword
| config_line_t* HashedControlPassword |
Base64-encoded hash of accepted passwords for the control system.
◆ HashedControlSessionPassword
| config_line_t* HashedControlSessionPassword |
As HashedControlPassword, but not saved.
◆ HeartbeatPeriod
| int HeartbeatPeriod |
Log heartbeat messages after this many seconds have passed.
◆ HiddenServiceSingleHopMode
| int HiddenServiceSingleHopMode |
Onion Services in HiddenServiceSingleHopMode make one-hop (direct) circuits between the onion service server, and the introduction and rendezvous points. (Onion service descriptors are still posted using 3-hop paths, to avoid onion service directories blocking the service.) This option makes every hidden service instance hosted by this tor instance a Single Onion Service. HiddenServiceSingleHopMode requires HiddenServiceNonAnonymousMode to be set to 1. Use rend_service_allow_non_anonymous_connection() or rend_service_reveal_startup_time() instead of using this option directly.
◆ HiddenServiceStatistics
| int HiddenServiceStatistics |
Internal variable to remember whether we're actually acting on HiddenServiceStatistics_option – yes if it's set and we're a server, else no.
◆ HiddenServiceStatistics_option
| int HiddenServiceStatistics_option |
If true, the user wants us to collect statistics as hidden service directory, introduction point, or rendezvous point.
◆ HidServAuth
| config_line_t* HidServAuth |
List of configuration lines for client-side authorizations for hidden services
◆ HSLayer2Nodes
| routerset_t* HSLayer2Nodes |
A routerset that should be used when picking middle nodes for HS circuits.
◆ HSLayer3Nodes
| routerset_t* HSLayer3Nodes |
A routerset that should be used when picking third-hop nodes for HS circuits.
◆ HTTPProxy
| char* HTTPProxy |
hostname[:port] to use as http proxy, if any.
◆ HTTPProxyAddr
| tor_addr_t HTTPProxyAddr |
Parsed IPv4 addr for http proxy, if any.
◆ HTTPProxyAuthenticator
| char* HTTPProxyAuthenticator |
username:password string, if any.
◆ HTTPProxyPort
| uint16_t HTTPProxyPort |
Parsed port for http proxy, if any.
◆ HTTPSProxy
| char* HTTPSProxy |
hostname[:port] to use as https proxy, if any.
◆ HTTPSProxyAddr
| tor_addr_t HTTPSProxyAddr |
Parsed addr for https proxy, if any.
◆ HTTPSProxyAuthenticator
| char* HTTPSProxyAuthenticator |
username:password string, if any.
◆ HTTPSProxyPort
| uint16_t HTTPSProxyPort |
Parsed port for https proxy, if any.
◆ HTTPTunnelPort_lines
| config_line_t* HTTPTunnelPort_lines |
Ports to listen on for HTTP Tunnel connections.
◆ IncludeUsed
| int IncludeUsed |
Bool (default: 0): Tells if a include was used on torrc
◆ IPv6Exit
| int IPv6Exit |
Do we support exiting to IPv6 addresses?
◆ KeepalivePeriod
| int KeepalivePeriod |
How often do we send padding cells to keep connections alive?
◆ KeepBindCapabilities
| int KeepBindCapabilities |
Autobool: Do we try to retain capabilities if we can?
◆ KeyDirectory
| char* KeyDirectory |
Where to store keys data, as modified.
◆ KeyDirectory_option
| char* KeyDirectory_option |
Where to store keys, as configured by the user.
◆ KeyDirectoryGroupReadable
| int KeyDirectoryGroupReadable |
Boolean: Is the KeyDirectory g+r?
◆ KISTSchedRunInterval
| int KISTSchedRunInterval |
Have the KIST scheduler run every X milliseconds. If less than zero, do not use the KIST scheduler but use the old vanilla scheduler instead. If zero, do what the consensus says and fall back to using KIST as if this is set to "10 msec" if the consensus doesn't say anything.
◆ KISTSockBufSizeFactor
| double KISTSockBufSizeFactor |
A multiplier for the KIST per-socket limit calculation.
◆ LearnCircuitBuildTimeout
| int LearnCircuitBuildTimeout |
If non-zero, we attempt to learn a value for CircuitBuildTimeout based on timeout history. Use circuit_build_times_disabled() rather than checking this value directly.
◆ LeaveStreamsUnattached
| int LeaveStreamsUnattached |
Boolean: Does Tor attach new streams to circuits itself (0), or does it expect a controller to cope? (1)
◆ LogMessageDomains
| int LogMessageDomains |
Boolean: Should we log the domain(s) in which each log message occurs?
◆ Logs
| config_line_t* Logs |
New-style list of configuration lines for logs
◆ LogTimeGranularity
| int LogTimeGranularity |
Log resolution in milliseconds.
◆ LongLivedPorts
| smartlist_t* LongLivedPorts |
Application ports that require all nodes in circ to have sufficient uptime.
◆ MainloopStats
| int MainloopStats |
Log main loop statistics as part of the heartbeat messages.
◆ MaxAdvertisedBandwidth
| uint64_t MaxAdvertisedBandwidth |
How much bandwidth are we willing to tell other nodes we have?
◆ MaxCircuitDirtiness
| int MaxCircuitDirtiness |
Never use circs that were first used more than this interval ago.
◆ MaxClientCircuitsPending
| int MaxClientCircuitsPending |
Maximum number of non-open general-purpose origin circuits to allow at once.
◆ MaxConsensusAgeForDiffs
| int MaxConsensusAgeForDiffs |
The seconds after expiration which we as a relay should keep old consensuses around so that we can generate diffs from them. If 0, use the default.
◆ MaxMemInQueues
| uint64_t MaxMemInQueues |
If we have more memory than this allocated for queues and buffers, run the OOM handler
◆ MaxMemInQueues_low_threshold
| uint64_t MaxMemInQueues_low_threshold |
Above this value, consider ourselves low on RAM.
◆ MaxUnparseableDescSizeToLog
| uint64_t MaxUnparseableDescSizeToLog |
Maximum total size of unparseable descriptors to log during the lifetime of this Tor process.
◆ MinMeasuredBWsForAuthToIgnoreAdvertised
| int MinMeasuredBWsForAuthToIgnoreAdvertised |
Authority only: minimum number of measured bandwidths we must see before we only believe measured bandwidths to assign flags.
◆ MinUptimeHidServDirectoryV2
| int MinUptimeHidServDirectoryV2 |
As directory authority, accept hidden service directories after what time?
◆ MyFamily
| config_line_t* MyFamily |
Declared family for this OR, normalized
◆ MyFamily_lines
| config_line_t* MyFamily_lines |
Declared family for this OR.
◆ NATDPort_lines
| config_line_t* NATDPort_lines |
Ports to listen on for transparent natd connections.
◆ NewCircuitPeriod
| int NewCircuitPeriod |
How long do we use a circuit before building a new one?
◆ Nickname
| char* Nickname |
OR only: nickname of this onion router.
◆ NodeFamilies
| config_line_t* NodeFamilies |
List of config lines for node families
◆ NodeFamilySets
| smartlist_t* NodeFamilySets |
List of parsed NodeFamilies values.
◆ NoExec
| int NoExec |
Bool (default: 0). Tells Tor to never try to exec another program.
◆ NumCPUs
| int NumCPUs |
How many CPUs should we try to use?
◆ NumDirectoryGuards
| int NumDirectoryGuards |
How many dir guards do we try to establish? If 0, use value from NumEntryGuards.
◆ NumEntryGuards
| int NumEntryGuards |
How many entry guards do we try to establish?
◆ NumPrimaryGuards
| int NumPrimaryGuards |
How many primary guards do we want?
◆ OfflineMasterKey
| int OfflineMasterKey |
Force use of offline master key features: never generate a master ed25519 identity key except from tor –keygen
◆ OptimisticData
| int OptimisticData |
If 1, we always send optimistic data when it's supported. If 0, we never use it. If -1, we do what the consensus says.
◆ ORPort_lines
| config_line_t* ORPort_lines |
Ports to listen on for OR connections.
◆ OutboundBindAddress
| config_line_t* OutboundBindAddress |
Local address to bind outbound sockets
◆ OutboundBindAddresses
| tor_addr_t OutboundBindAddresses[OUTBOUND_ADDR_MAX][2] |
Addresses derived from the various OutboundBindAddress lines. [][0] is IPv4, [][1] is IPv6
◆ OutboundBindAddressExit
| config_line_t* OutboundBindAddressExit |
Local address to bind outbound exit sockets
◆ OutboundBindAddressOR
| config_line_t* OutboundBindAddressOR |
Local address to bind outbound relay sockets
◆ OwningControllerFD
| int OwningControllerFD |
FD specifier for a controller that owns this Tor instance.
◆ OwningControllerProcess
| char* OwningControllerProcess |
Process specifier for a controller that ‘owns’ this Tor instance. Tor will terminate if its owning controller does.
◆ PaddingStatistics
| int PaddingStatistics |
If true, the user wants us to collect padding statistics.
◆ PathBiasCircThreshold
| int PathBiasCircThreshold |
Parameters for path-bias detection.
These options override the default behavior of Tor's (currently experimental) path bias detection algorithm. To try to find broken or misbehaving guard nodes, Tor looks for nodes where more than a certain fraction of circuits through that guard fail to get built.
The PathBiasCircThreshold option controls how many circuits we need to build through a guard before we make these checks. The PathBiasNoticeRate, PathBiasWarnRate and PathBiasExtremeRate options control what fraction of circuits must succeed through a guard so we won't write log messages. If less than PathBiasExtremeRate circuits succeed and PathBiasDropGuards is set to 1, we disable use of that guard.
When we have seen more than PathBiasScaleThreshold circuits through a guard, we scale our observations by 0.5 (governed by the consensus) so that new observations don't get swamped by old ones.
By default, or if a negative value is provided for one of these options, Tor uses reasonable defaults from the networkstatus consensus document. If no defaults are available there, these options default to 150, .70, .50, .30, 0, and 300 respectively.
◆ PathBiasUseThreshold
| int PathBiasUseThreshold |
Parameters for path-bias use detection
Similar to the above options, these options override the default behavior of Tor's (currently experimental) path use bias detection algorithm.
Where as the path bias parameters govern thresholds for successfully building circuits, these four path use bias parameters govern thresholds only for circuit usage. Circuits which receive no stream usage are not counted by this detection algorithm. A used circuit is considered successful if it is capable of carrying streams or otherwise receiving well-formed responses to RELAY cells.
By default, or if a negative value is provided for one of these options, Tor uses reasonable defaults from the networkstatus consensus document. If no defaults are available there, these options default to 20, .80, .60, and 100, respectively.
◆ PathsNeededToBuildCircuits
| double PathsNeededToBuildCircuits |
Fraction:
◆ PerConnBWBurst
| uint64_t PerConnBWBurst |
Allowed burst on a single TLS conn, if set.
◆ PerConnBWRate
| uint64_t PerConnBWRate |
Long-term bw on a single TLS conn, if set.
◆ PidFile
| char* PidFile |
Where to store PID of Tor process.
◆ ProtocolWarnings
| int ProtocolWarnings |
Boolean: when other parties screw up the Tor protocol, is it a warn or an info in our logs?
◆ PublishHidServDescriptors
| int PublishHidServDescriptors |
Boolean: do we publish hidden service descriptors to the HS auths?
◆ PublishServerDescriptor
| smartlist_t* PublishServerDescriptor |
To what authority types do we publish our descriptor? Choices are "v1", "v2", "v3", "bridge", or "".
◆ PublishServerDescriptor_
| dirinfo_type_t PublishServerDescriptor_ |
A bitfield of authority types, derived from PublishServerDescriptor.
◆ ReachableAddresses
| config_line_t* ReachableAddresses |
IP:ports our firewall allows.
◆ ReachableDirAddresses
| config_line_t* ReachableDirAddresses |
IP:ports for Dir conns.
◆ ReachableORAddresses
| config_line_t* ReachableORAddresses |
IP:ports for OR conns.
◆ RecommendedVersions
| config_line_t* RecommendedVersions |
Directory server only: which versions of Tor should we tell users to run?
◆ ReducedConnectionPadding
| int ReducedConnectionPadding |
Boolean: Should we try to keep connections open shorter and pad them less against connection-level traffic analysis?
◆ ReducedExitPolicy
| int ReducedExitPolicy |
Should we use the Reduced Exit Policy?
◆ RefuseUnknownExits
| int RefuseUnknownExits |
Whether we should drop exit streams from Tors that we don't know are relays. One of "0" (never refuse), "1" (always refuse), or "-1" (do what the consensus says, defaulting to 'refuse' if the consensus says nothing).
◆ RejectPlaintextPorts
| smartlist_t* RejectPlaintextPorts |
Application ports that are likely to be unencrypted and unauthenticated; we reject requests for them to prevent the user from screwing up and leaking plaintext secrets to an observer somewhere on the Internet.
◆ RelayBandwidthBurst
| uint64_t RelayBandwidthBurst |
How much bandwidth, at maximum, will we use in a second for all relayed conns?
◆ RelayBandwidthRate
| uint64_t RelayBandwidthRate |
How much bandwidth, on average, are we willing to use for all relayed conns?
◆ ReloadTorrcOnSIGHUP
| int ReloadTorrcOnSIGHUP |
If true, SIGHUP should reload the torrc. Sometimes controllers want to make this false.
◆ RendConfigLines
| config_line_t* RendConfigLines |
List of configuration lines for rendezvous services.
◆ RendPostPeriod
| int RendPostPeriod |
How often do we post each rendezvous service descriptor? Remember to publish them independently.
◆ RephistTrackTime
| int RephistTrackTime |
How many seconds do we keep rephist info?
◆ RunAsDaemon
| int RunAsDaemon |
If true, run in the background. (Unix only)
◆ SafeLogging
| char* SafeLogging |
Contains "relay", "1", "0" (meaning no scrubbing).
◆ SafeSocks
| int SafeSocks |
Boolean: should we outright refuse application connections that use socks4 or socks5-with-local-dns?
◆ Sandbox
| int Sandbox |
Boolean: should sandboxing be enabled?
◆ Schedulers
| smartlist_t* Schedulers |
The list of scheduler type string ordered by priority that is first one has to be tried first. Default: KIST,KISTLite,Vanilla
◆ ServerDNSAllowBrokenConfig
| int ServerDNSAllowBrokenConfig |
Boolean: if set, we start even if our resolv.conf file is missing or broken.
◆ ServerDNSAllowNonRFC953Hostnames
| int ServerDNSAllowNonRFC953Hostnames |
If true, we try resolving hostnames with weird characters.
◆ ServerDNSDetectHijacking
| int ServerDNSDetectHijacking |
Boolean: If true, check for DNS failure hijacking.
◆ ServerDNSRandomizeCase
| int ServerDNSRandomizeCase |
Boolean: Use the 0x20-hack to prevent DNS poisoning attacks.
◆ ServerDNSResolvConfFile
| char* ServerDNSResolvConfFile |
If provided, we configure our internal resolver from the file here rather than from /etc/resolv.conf (Unix) or the registry (Windows).
◆ ServerDNSSearchDomains
| int ServerDNSSearchDomains |
Boolean: If set, we don't force exit addresses to be FQDNs, but rather search for them in the local domains.
◆ ServerDNSTestAddresses
| smartlist_t* ServerDNSTestAddresses |
A list of addresses that definitely should be resolvable. Used for testing our DNS server.
◆ ServerTransportListenAddr
| config_line_t* ServerTransportListenAddr |
List of TCP/IP addresses that transports should listen at.
◆ ServerTransportOptions
| config_line_t* ServerTransportOptions |
List of options that must be passed to pluggable transports.
◆ ServerTransportPlugin
| config_line_t* ServerTransportPlugin |
List of client transport plugins.
◆ ShutdownWaitLength
| int ShutdownWaitLength |
When we get a SIGINT and we're a server, how long do we wait before exiting?
◆ SigningKeyLifetime
| int SigningKeyLifetime |
For how long (seconds) do we declare our signing keys to be valid?
◆ Socks4Proxy
| char* Socks4Proxy |
hostname:port to use as a SOCKS4 proxy, if any.
◆ Socks4ProxyAddr
| tor_addr_t Socks4ProxyAddr |
Derived from Socks4Proxy.
◆ Socks4ProxyPort
| uint16_t Socks4ProxyPort |
Derived from Socks4Proxy.
◆ Socks5Proxy
| char* Socks5Proxy |
hostname:port to use as a SOCKS5 proxy, if any.
◆ Socks5ProxyAddr
| tor_addr_t Socks5ProxyAddr |
Derived from Sock5Proxy.
◆ Socks5ProxyPassword
| char* Socks5ProxyPassword |
Password for SOCKS5 authentication, if any
◆ Socks5ProxyPort
| uint16_t Socks5ProxyPort |
Derived from Socks5Proxy.
◆ Socks5ProxyUsername
| char* Socks5ProxyUsername |
Username for SOCKS5 authentication, if any
◆ SocksPolicy
| config_line_t* SocksPolicy |
Lists of socks policy components
◆ SocksPort_lines
| config_line_t* SocksPort_lines |
Ports to listen on for SOCKS connections.
◆ SocksTimeout
| int SocksTimeout |
How long do we let a socks connection wait unattached before we fail it?
◆ SSLKeyLifetime
| int SSLKeyLifetime |
What expiry time shall we place on our SSL certs? "0" means we should guess a suitable value.
◆ StrictNodes
| int StrictNodes |
Boolean: When none of our EntryNodes or ExitNodes are up, or we need to access a node in ExcludeNodes, do we just fail instead?
◆ SyslogIdentityTag
| char* SyslogIdentityTag |
Identity tag to add for syslog logging.
◆ TestingAuthDirTimeToLearnReachability
| int TestingAuthDirTimeToLearnReachability |
If an authority has been around for less than this amount of time, it does not believe its reachability information is accurate. Only altered on testing networks.
◆ TestingAuthKeyLifetime
| int TestingAuthKeyLifetime |
For how long (seconds) do we declare our auth keys to be valid?
◆ TestingAuthKeySlop
| int TestingAuthKeySlop |
How long before auth keys expire will we try to make a new one?
◆ TestingBridgeBootstrapDownloadInitialDelay
| int TestingBridgeBootstrapDownloadInitialDelay |
Schedule for when clients should download bridge descriptors when they have no running bridges. Only altered on testing networks.
◆ TestingBridgeDownloadInitialDelay
| int TestingBridgeDownloadInitialDelay |
Schedule for when clients should download bridge descriptors. Only altered on testing networks.
◆ TestingClientConsensusDownloadInitialDelay
| int TestingClientConsensusDownloadInitialDelay |
Schedule for when clients should download consensuses. Only altered on testing networks.
◆ TestingClientDownloadInitialDelay
| int TestingClientDownloadInitialDelay |
Schedule for when clients should download things in general. Only altered on testing networks.
◆ TestingClientMaxIntervalWithoutRequest
| int TestingClientMaxIntervalWithoutRequest |
When directory clients have only a few descriptors to request, they batch them until they have more, or until this amount of time has passed. Only altered on testing networks.
◆ TestingDirAuthVoteExit
| routerset_t* TestingDirAuthVoteExit |
Relays in a testing network which should be voted Exit regardless of exit policy.
◆ TestingDirAuthVoteGuard
| routerset_t* TestingDirAuthVoteGuard |
Relays in a testing network which should be voted Guard regardless of uptime and bandwidth.
◆ TestingDirAuthVoteHSDir
| routerset_t* TestingDirAuthVoteHSDir |
Relays in a testing network which should be voted HSDir regardless of uptime and DirPort.
◆ TestingDirConnectionMaxStall
| int TestingDirConnectionMaxStall |
How long do we let a directory connection stall before expiring it? Only altered on testing networks.
◆ TestingEnableCellStatsEvent
| int TestingEnableCellStatsEvent |
Enable CELL_STATS events. Only altered on testing networks.
◆ TestingEnableConnBwEvent
| int TestingEnableConnBwEvent |
Enable CONN_BW events. Only altered on testing networks.
◆ TestingEstimatedDescriptorPropagationTime
| int TestingEstimatedDescriptorPropagationTime |
Clients don't download any descriptor this recent, since it will probably not have propagated to enough caches. Only altered on testing networks.
◆ TestingLinkCertLifetime
| int TestingLinkCertLifetime |
For how long (seconds) do we declare our link keys to be valid?
◆ TestingLinkKeySlop
| int TestingLinkKeySlop |
How long before link keys expire will we try to make a new one?
◆ TestingMinExitFlagThreshold
| uint64_t TestingMinExitFlagThreshold |
Minimum value for the Exit flag threshold on testing networks.
◆ TestingMinFastFlagThreshold
| uint64_t TestingMinFastFlagThreshold |
Minimum value for the Fast flag threshold on testing networks.
◆ TestingServerConsensusDownloadInitialDelay
| int TestingServerConsensusDownloadInitialDelay |
Schedule for when servers should download consensuses. Only altered on testing networks.
◆ TestingServerDownloadInitialDelay
| int TestingServerDownloadInitialDelay |
Schedule for when servers should download things in general. Only altered on testing networks.
◆ TestingSigningKeySlop
| int TestingSigningKeySlop |
How long before signing keys expire will we try to make a new one?
◆ TestingTorNetwork
| int TestingTorNetwork |
If true, we take part in a testing network. Change the defaults of a couple of other configuration options and allow to change the values of certain configuration options.
◆ TestingV3AuthInitialDistDelay
| int TestingV3AuthInitialDistDelay |
The length of time we think it will take to distribute initial signatures. Only altered on testing networks.
◆ TestingV3AuthInitialVoteDelay
| int TestingV3AuthInitialVoteDelay |
The length of time we think it will take to distribute initial votes. Only altered on testing networks.
◆ TestingV3AuthInitialVotingInterval
| int TestingV3AuthInitialVotingInterval |
The length of time that we think an initial consensus should be fresh. Only altered on testing networks.
◆ TestingV3AuthVotingStartOffset
| int TestingV3AuthVotingStartOffset |
Offset in seconds added to the starting time for consensus voting. Only altered on testing networks.
◆ TestSocks
| int TestSocks |
Boolean: when we get a socks connection, do we loudly log whether it was DNS-leaking or not?
◆ TokenBucketRefillInterval
| int TokenBucketRefillInterval |
Token Bucket Refill resolution in milliseconds.
◆ Tor2webMode
| int Tor2webMode |
Run in 'tor2web mode'? (I.e. only make client connections to hidden services, and use a single hop for all hidden-service-related circuits.)
◆ Tor2webRendezvousPoints
| routerset_t* Tor2webRendezvousPoints |
A routerset that should be used when picking RPs for HS circuits.
◆ TrackHostExits
| smartlist_t* TrackHostExits |
Should we try to reuse the same exit node for a given host
◆ TrackHostExitsExpire
| int TrackHostExitsExpire |
Number of seconds until we expire an addressmap
◆ TransPort_lines
| config_line_t* TransPort_lines |
Ports to listen on for transparent pf/netfilter connections.
◆ TransProxyType
| char* TransProxyType |
What kind of transparent proxy implementation are we using?
◆ TransProxyType_parsed
| enum { ... } TransProxyType_parsed |
Parsed value of TransProxyType.
◆ TruncateLogFile
| int TruncateLogFile |
Boolean: Should we truncate the log file before we start writing?
◆ UnixSocksGroupWritable
| int UnixSocksGroupWritable |
Boolean: Are SOCKS Unix sockets g+rw?
◆ UpdateBridgesFromAuthority
| int UpdateBridgesFromAuthority |
Boolean: if we know the bridge's digest, should we get new descriptors from the bridge authorities or from the bridge itself?
◆ UseBridges
| int UseBridges |
Boolean: should we start all circuits with a bridge?
◆ UseDefaultFallbackDirs
| int UseDefaultFallbackDirs |
Whether to use the default hard-coded FallbackDirs
◆ UseEntryGuards
| int UseEntryGuards |
Internal variable to remember whether we're actually acting on UseEntryGuards_option – when we're a non-anonymous Tor2web client or Single Onion Service, it is always false, otherwise we use the value of UseEntryGuards_option.
◆ UseEntryGuards_option
| int UseEntryGuards_option |
Boolean: Do we try to enter from a smallish number of fixed nodes?
◆ UseGuardFraction
| int UseGuardFraction |
If 1, we use any guardfraction information we see in the consensus. If 0, we don't. If -1, let the consensus parameter decide.
◆ UseMicrodescriptors
| int UseMicrodescriptors |
If 1, we try to use microdescriptors to build circuits. If 0, we don't. If -1, Tor decides.
◆ User
| char* User |
Name of user to run Tor as.
◆ UsingTestNetworkDefaults_
| int UsingTestNetworkDefaults_ |
Set to true if the TestingTorNetwork configuration option is set. This is used so that options_validate() has a chance to realize that the defaults have changed.
◆ V3AuthDistDelay
| int V3AuthDistDelay |
The length of time we think it will take to distribute signatures.
◆ V3AuthNIntervalsValid
| int V3AuthNIntervalsValid |
The number of intervals we think a consensus should be valid.
◆ V3AuthoritativeDir
| int V3AuthoritativeDir |
Boolean: is this an authoritative directory for version 3 directories?
◆ V3AuthUseLegacyKey
| int V3AuthUseLegacyKey |
Should advertise and sign consensuses with a legacy key, for key migration purposes?
◆ V3AuthVoteDelay
| int V3AuthVoteDelay |
The length of time we think it will take to distribute votes.
◆ V3AuthVotingInterval
| int V3AuthVotingInterval |
The length of time that we think a consensus should be fresh.
◆ V3BandwidthsFile
| char* V3BandwidthsFile |
Location of bandwidth measurement file
◆ VersioningAuthoritativeDir
| int VersioningAuthoritativeDir |
Boolean: is this an authoritative directory that's willing to recommend versions?
◆ VirtualAddrNetworkIPv4
| char* VirtualAddrNetworkIPv4 |
Address and mask to hand out for virtual MAPADDRESS requests for IPv4 addresses
◆ VirtualAddrNetworkIPv6
| char* VirtualAddrNetworkIPv6 |
Address and mask to hand out for virtual MAPADDRESS requests for IPv6 addresses
◆ WarnPlaintextPorts
| smartlist_t* WarnPlaintextPorts |
Related to RejectPlaintextPorts above, except this config option controls whether we warn (in the log and via a controller status event) every time a risky connection is attempted.
The documentation for this struct was generated from the following file:
- /home/user/_my/code/bwauth-related/tor/src/or/or.h
 1.8.13
1.8.13