#include <or.h>
Data Fields | |
| time_t | sent_versions_at |
| unsigned int | started_here: 1 |
| unsigned int | received_versions: 1 |
| unsigned int | received_auth_challenge: 1 |
| unsigned int | received_certs_cell: 1 |
| unsigned int | received_authenticate: 1 |
| unsigned int | authenticated: 1 |
| unsigned int | authenticated_rsa: 1 |
| unsigned int | authenticated_ed25519: 1 |
| unsigned int | sent_netinfo: 1 |
| struct tor_cert_st * | own_link_cert |
| uint8_t | authenticated_rsa_peer_id [DIGEST_LEN] |
| ed25519_public_key_t | authenticated_ed25519_peer_id |
| or_handshake_certs_t * | certs |
| unsigned int | digest_sent_data: 1 |
| unsigned int | digest_received_data: 1 |
| crypto_digest_t * | digest_sent |
| crypto_digest_t * | digest_received |
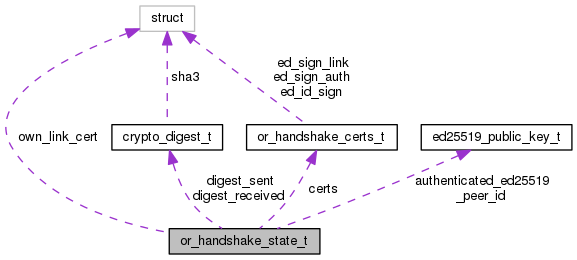
Detailed Description
Stores flags and information related to the portion of a v2/v3 Tor OR connection handshake that happens after the TLS handshake is finished.
Field Documentation
◆ authenticated_ed25519_peer_id
| ed25519_public_key_t authenticated_ed25519_peer_id |
Identity Ed25519 public key that we have received and authenticated for our peer on this connection.
◆ authenticated_rsa_peer_id
| uint8_t authenticated_rsa_peer_id[DIGEST_LEN] |
Identity RSA digest that we have received and authenticated for our peer on this connection.
◆ certs
| or_handshake_certs_t* certs |
Certificates that a connection initiator sent us in a CERTS cell; we're holding on to them until we get an AUTHENTICATE cell.
◆ digest_sent
| crypto_digest_t* digest_sent |
Digests of the cells that we have sent or received as part of a V3 handshake. Used for making and checking AUTHENTICATE cells.
◆ digest_sent_data
| unsigned int digest_sent_data |
True iff we should feed outgoing cells into digest_sent and digest_received respectively.
From the server's side of the v3 handshake, we want to capture everything from the VERSIONS cell through and including the AUTH_CHALLENGE cell. From the client's, we want to capture everything from the VERSIONS cell through but not including the AUTHENTICATE cell.
◆ own_link_cert
| struct tor_cert_st* own_link_cert |
The signing->ed25519 link certificate corresponding to the x509 certificate we used on the TLS connection (if this is a server-side connection). We make a copy of this here to prevent a race condition caused by TLS context rotation.
◆ received_auth_challenge
| unsigned int received_auth_challenge |
True iff we have received and processed an AUTH_CHALLENGE cell
◆ received_authenticate
| unsigned int received_authenticate |
True iff we have received and processed an AUTHENTICATE cell
◆ received_certs_cell
| unsigned int received_certs_cell |
True iff we have received and processed a CERTS cell.
◆ received_versions
| unsigned int received_versions |
True iff we have received and processed a VERSIONS cell.
◆ sent_versions_at
| time_t sent_versions_at |
When was the VERSIONS cell sent on this connection? Used to get an estimate of the skew in the returning NETINFO reply.
◆ started_here
| unsigned int started_here |
True iff we originated this connection
The documentation for this struct was generated from the following file:
- /home/user/_my/code/bwauth-related/tor/src/or/or.h
 1.8.13
1.8.13