Implementation for ed25519-signed certificates as used in the Tor protocol. More...
#include "or.h"#include "config.h"#include "crypto_util.h"#include "torcert.h"#include "ed25519_cert.h"#include "torlog.h"#include "util.h"#include "compat.h"#include "link_handshake.h"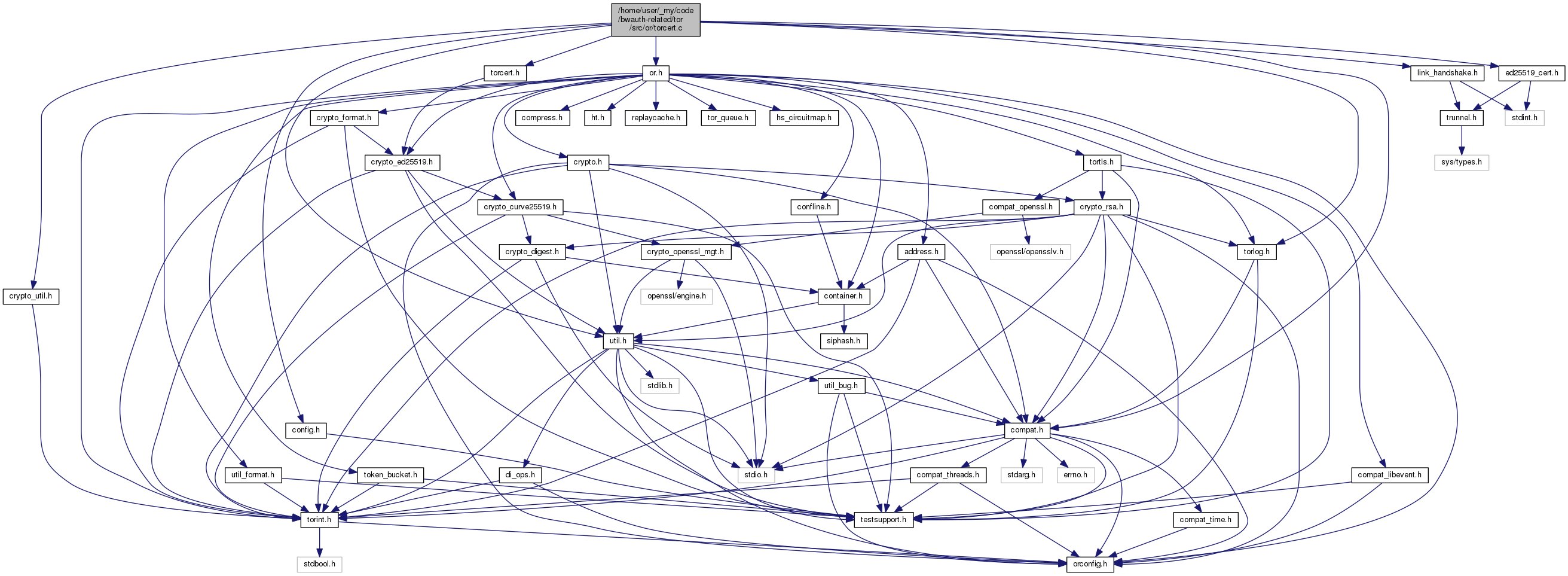
Macros | |
| #define | RSA_ED_CROSSCERT_PREFIX "Tor TLS RSA/Ed25519 cross-certificate" |
| #define | ERR(code, s) |
| #define | ERR(s) |
| #define | ADDCERT(cert, pk) |
Functions | |
| tor_cert_t * | tor_cert_create (const ed25519_keypair_t *signing_key, uint8_t cert_type, const ed25519_public_key_t *signed_key, time_t now, time_t lifetime, uint32_t flags) |
| void | tor_cert_free_ (tor_cert_t *cert) |
| tor_cert_t * | tor_cert_parse (const uint8_t *encoded, const size_t len) |
| int | tor_cert_get_checkable_sig (ed25519_checkable_t *checkable_out, const tor_cert_t *cert, const ed25519_public_key_t *pubkey, time_t *expiration_out) |
| int | tor_cert_checksig (tor_cert_t *cert, const ed25519_public_key_t *pubkey, time_t now) |
| const char * | tor_cert_describe_signature_status (const tor_cert_t *cert) |
| tor_cert_t * | tor_cert_dup (const tor_cert_t *cert) |
| int | tor_cert_eq (const tor_cert_t *cert1, const tor_cert_t *cert2) |
| int | tor_cert_opt_eq (const tor_cert_t *cert1, const tor_cert_t *cert2) |
| ssize_t | tor_make_rsa_ed25519_crosscert (const ed25519_public_key_t *ed_key, const crypto_pk_t *rsa_key, time_t expires, uint8_t **cert) |
| MOCK_IMPL (int, rsa_ed25519_crosscert_check,(const uint8_t *crosscert, const size_t crosscert_len, const crypto_pk_t *rsa_id_key, const ed25519_public_key_t *master_key, const time_t reject_if_expired_before)) | |
| or_handshake_certs_t * | or_handshake_certs_new (void) |
| void | or_handshake_certs_free_ (or_handshake_certs_t *certs) |
| int | or_handshake_certs_rsa_ok (int severity, or_handshake_certs_t *certs, tor_tls_t *tls, time_t now) |
| int | or_handshake_certs_ed25519_ok (int severity, or_handshake_certs_t *certs, tor_tls_t *tls, time_t now) |
| void | or_handshake_certs_check_both (int severity, or_handshake_certs_t *certs, tor_tls_t *tls, time_t now, const ed25519_public_key_t **ed_id_out, const common_digests_t **rsa_id_out) |
| int | tor_cert_encode_ed22519 (const tor_cert_t *cert, char **cert_str_out) |
Detailed Description
Implementation for ed25519-signed certificates as used in the Tor protocol.
This certificate format is designed to be simple and compact; it's documented in tor-spec.txt in the torspec.git repository. All of the certificates in this format are signed with an Ed25519 key; the contents themselves may be another Ed25519 key, a digest of a RSA key, or some other material.
In this module there is also support for a crooss-certification of Ed25519 identities using (older) RSA1024 identities.
Tor uses other types of certificate too, beyond those described in this module. Notably, our use of TLS requires us to touch X.509 certificates, even though sensible people would stay away from those. Our X.509 certificates are represented with tor_x509_cert_t, and implemented in tortls.c. We also have a separate certificate type that authorities use to authenticate their RSA signing keys with their RSA identity keys: that one is authority_cert_t, and it's mostly handled in routerlist.c.
Macro Definition Documentation
◆ ADDCERT
| #define ADDCERT | ( | cert, | |
| pk | |||
| ) |
◆ ERR [1/2]
| #define ERR | ( | code, | |
| s | |||
| ) |
◆ ERR [2/2]
| #define ERR | ( | s | ) |
Function Documentation
◆ MOCK_IMPL()
| MOCK_IMPL | ( | int | , |
| rsa_ed25519_crosscert_check | , | ||
| (const uint8_t *crosscert, const size_t crosscert_len, const crypto_pk_t *rsa_id_key, const ed25519_public_key_t *master_key, const time_t reject_if_expired_before) | |||
| ) |
Check whether the crosscert_len byte certificate in crosscert is in fact a correct cross-certification of master_key using the RSA key rsa_id_key.
Also reject the certificate if it expired before reject_if_expired_before.
Return 0 on success, negative on failure.
◆ or_handshake_certs_check_both()
| void or_handshake_certs_check_both | ( | int | severity, |
| or_handshake_certs_t * | certs, | ||
| tor_tls_t * | tls, | ||
| time_t | now, | ||
| const ed25519_public_key_t ** | ed_id_out, | ||
| const common_digests_t ** | rsa_id_out | ||
| ) |
Check the Ed certificates and/or the RSA certificates, as appropriate. If we obtained an Ed25519 identity, set *ed_id_out. If we obtained an RSA identity, set *rs_id_out. Otherwise, set them both to NULL.
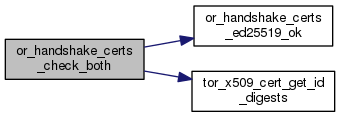
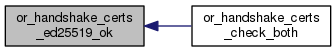
◆ or_handshake_certs_ed25519_ok()
| int or_handshake_certs_ed25519_ok | ( | int | severity, |
| or_handshake_certs_t * | certs, | ||
| tor_tls_t * | tls, | ||
| time_t | now | ||
| ) |
Check all the ed25519 certificates in certs against each other, and against the peer certificate in tls if appropriate. On success, return 0; on failure, return a negative value and warn at level severity
◆ or_handshake_certs_free_()
| void or_handshake_certs_free_ | ( | or_handshake_certs_t * | certs | ) |
Release all storage held in certs
◆ or_handshake_certs_new()
| or_handshake_certs_t* or_handshake_certs_new | ( | void | ) |
Construct and return a new empty or_handshake_certs object
◆ tor_cert_checksig()
| int tor_cert_checksig | ( | tor_cert_t * | cert, |
| const ed25519_public_key_t * | pubkey, | ||
| time_t | now | ||
| ) |
Validates the signature on cert with pubkey relative to the current time now. (If now is 0, do not check the expiration time.) Return 0 on success, -1 on failure. Sets flags in cert as appropriate.
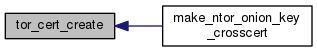
◆ tor_cert_create()
| tor_cert_t* tor_cert_create | ( | const ed25519_keypair_t * | signing_key, |
| uint8_t | cert_type, | ||
| const ed25519_public_key_t * | signed_key, | ||
| time_t | now, | ||
| time_t | lifetime, | ||
| uint32_t | flags | ||
| ) |
Create and return a new new certificate of type cert_type to authenticate signed_key using the key signing_key. The certificate should remain valid for at least lifetime seconds after now.
If CERT_FLAG_INCLUDE_SIGNING_KEY is set in flags, embed the public part of signing_key in the certificate.
◆ tor_cert_describe_signature_status()
| const char* tor_cert_describe_signature_status | ( | const tor_cert_t * | cert | ) |
Return a string describing the status of the signature on cert
Will always be "unchecked" unless tor_cert_checksig has been called.
◆ tor_cert_dup()
| tor_cert_t* tor_cert_dup | ( | const tor_cert_t * | cert | ) |
Return a new copy of cert
◆ tor_cert_eq()
| int tor_cert_eq | ( | const tor_cert_t * | cert1, |
| const tor_cert_t * | cert2 | ||
| ) |
Return true iff cert1 and cert2 are the same cert.

◆ tor_cert_free_()
| void tor_cert_free_ | ( | tor_cert_t * | cert | ) |
Release all storage held for cert.

◆ tor_cert_get_checkable_sig()
| int tor_cert_get_checkable_sig | ( | ed25519_checkable_t * | checkable_out, |
| const tor_cert_t * | cert, | ||
| const ed25519_public_key_t * | pubkey, | ||
| time_t * | expiration_out | ||
| ) |
Fill in checkable_out with the information needed to check the signature on cert with pubkey.
On success, if expiration_out is provided, and it is some time after the expiration time of this certificate, set it to the expiration time of this certificate.
◆ tor_cert_opt_eq()
| int tor_cert_opt_eq | ( | const tor_cert_t * | cert1, |
| const tor_cert_t * | cert2 | ||
| ) |
Return true iff cert1 and cert2 are the same cert, or if they are both NULL.
◆ tor_cert_parse()
| tor_cert_t* tor_cert_parse | ( | const uint8_t * | encoded, |
| const size_t | len | ||
| ) |
Parse a certificate encoded with len bytes in encoded.
◆ tor_make_rsa_ed25519_crosscert()
| ssize_t tor_make_rsa_ed25519_crosscert | ( | const ed25519_public_key_t * | ed_key, |
| const crypto_pk_t * | rsa_key, | ||
| time_t | expires, | ||
| uint8_t ** | cert | ||
| ) |
Create new cross-certification object to certify ed_key as the master ed25519 identity key for the RSA identity key rsa_key. Allocates and stores the encoded certificate in *cert, and returns the number of bytes stored. Returns negative on error.
 1.8.13
1.8.13