#include <or.h>
Data Fields | |
| connection_t | base_ |
| char | identity_digest [DIGEST_LEN] |
| char * | ext_or_conn_id |
| char * | ext_or_auth_correct_client_hash |
| char * | ext_or_transport |
| char * | nickname |
| tor_tls_t * | tls |
| int | tls_error |
| channel_tls_t * | chan |
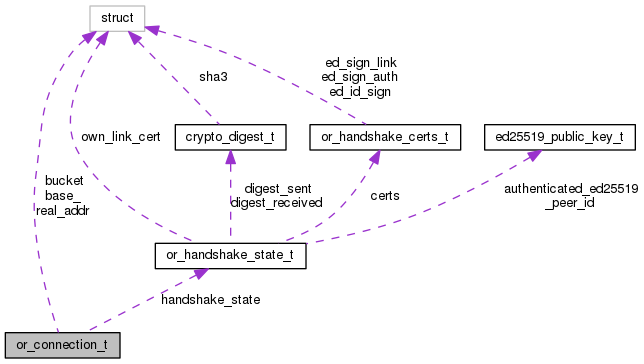
| tor_addr_t | real_addr |
| unsigned int | is_canonical:1 |
| unsigned int | is_outgoing:1 |
| unsigned int | proxy_type:2 |
| unsigned int | wide_circ_ids:1 |
| unsigned int | have_noted_bootstrap_problem:1 |
| unsigned int | tracked_for_dos_mitigation: 1 |
| uint16_t | link_proto |
| uint16_t | idle_timeout |
| or_handshake_state_t * | handshake_state |
| time_t | timestamp_lastempty |
| token_bucket_rw_t | bucket |
| uint64_t | bytes_xmitted |
| uint64_t | bytes_xmitted_by_tls |
Detailed Description
Subtype of connection_t for an "OR connection" – that is, one that speaks cells over TLS.
Field Documentation
◆ bucket
| token_bucket_rw_t bucket |
Used for rate limiting when the connection is in state CONN_OPEN.
◆ chan
| channel_tls_t* chan |
When we last used this conn for any client traffic. If not recent, we can rate limit it further.
◆ ext_or_auth_correct_client_hash
| char* ext_or_auth_correct_client_hash |
This is the ClientHash value we expect to receive from the client during the Extended ORPort authentication protocol. We compute it upon receiving the ClientNoce from the client, and we compare it with the acual ClientHash value sent by the client.
◆ ext_or_conn_id
| char* ext_or_conn_id |
Extended ORPort connection identifier.
◆ ext_or_transport
| char* ext_or_transport |
String carrying the name of the pluggable transport (e.g. "obfs2") that is obfuscating this connection. If no pluggable transports are used, it's NULL.
◆ handshake_state
| or_handshake_state_t* handshake_state |
If we are setting this connection up, state information to do so.
◆ have_noted_bootstrap_problem
| unsigned int have_noted_bootstrap_problem |
True iff this connection has had its bootstrap failure logged with control_event_bootstrap_problem.
◆ identity_digest
| char identity_digest[DIGEST_LEN] |
Hash of the public RSA key for the other side's identity key, or zeroes if the other side hasn't shown us a valid identity key.
◆ idle_timeout
| uint16_t idle_timeout |
How long can this connection sit with no circuits on it before we close it? Based on IDLE_CIRCUIT_TIMEOUT_{NON,}CANONICAL and on is_canonical, randomized.
◆ is_canonical
| unsigned int is_canonical |
Should this connection be used for extending circuits to the server matching the identity_digest field? Set to true if we're pretty sure we aren't getting MITMed, either because we're connected to an address listed in a server descriptor, or because an authenticated NETINFO cell listed the address we're connected to as recognized.
◆ is_outgoing
| unsigned int is_outgoing |
True iff this is an outgoing connection.
◆ link_proto
| uint16_t link_proto |
What protocol version are we using? 0 for "none negotiated yet."
◆ nickname
| char* nickname |
Nickname of OR on other side (if any).
◆ proxy_type
| unsigned int proxy_type |
One of PROXY_NONE...PROXY_SOCKS5
◆ real_addr
| tor_addr_t real_addr |
The actual address that this connection came from or went to. The addr field is prone to getting overridden by the address from the router descriptor matching identity_digest.
◆ timestamp_lastempty
| time_t timestamp_lastempty |
When was the outbuf last completely empty?
◆ tls
| tor_tls_t* tls |
TLS connection state.
◆ tls_error
| int tls_error |
Last tor_tls error code.
◆ tracked_for_dos_mitigation
| unsigned int tracked_for_dos_mitigation |
True iff this is a client connection and its address has been put in the geoip cache and handled by the DoS mitigation subsystem. We use this to insure we have a coherent count of concurrent connection.
The documentation for this struct was generated from the following file:
- /home/user/_my/code/bwauth-related/tor/src/or/or.h
 1.8.13
1.8.13