Header file for policies.c. More...
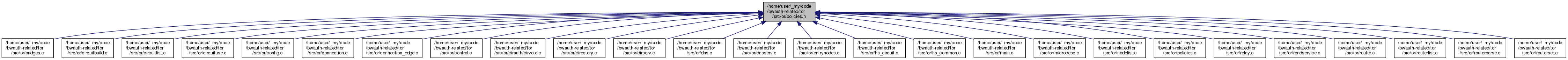
Go to the source code of this file.
Macros | |
| #define | POLICY_BUF_LEN 72 |
| #define | EXIT_POLICY_IPV6_ENABLED (1 << 0) |
| #define | EXIT_POLICY_REJECT_PRIVATE (1 << 1) |
| #define | EXIT_POLICY_ADD_DEFAULT (1 << 2) |
| #define | EXIT_POLICY_REJECT_LOCAL_INTERFACES (1 << 3) |
| #define | EXIT_POLICY_ADD_REDUCED (1 << 4) |
| #define | EXIT_POLICY_OPTION_MAX EXIT_POLICY_ADD_REDUCED |
| #define | EXIT_POLICY_OPTION_ALL ((EXIT_POLICY_OPTION_MAX << 1) - 1) |
| #define | addr_policy_list_free(lst) FREE_AND_NULL(smartlist_t, addr_policy_list_free_, (lst)) |
| #define | addr_policy_free(p) FREE_AND_NULL(addr_policy_t, addr_policy_free_, (p)) |
| #define | short_policy_free(p) FREE_AND_NULL(short_policy_t, short_policy_free_, (p)) |
Typedefs | |
| typedef enum firewall_connection_t | firewall_connection_t |
| typedef int | exit_policy_parser_cfg_t |
Enumerations | |
| enum | firewall_connection_t { FIREWALL_OR_CONNECTION = 0, FIREWALL_DIR_CONNECTION = 1 } |
Functions | |
| int | firewall_is_fascist_or (void) |
| int | firewall_is_fascist_dir (void) |
| int | fascist_firewall_use_ipv6 (const or_options_t *options) |
| int | fascist_firewall_prefer_ipv6_orport (const or_options_t *options) |
| int | fascist_firewall_prefer_ipv6_dirport (const or_options_t *options) |
| int | fascist_firewall_allows_address_addr (const tor_addr_t *addr, uint16_t port, firewall_connection_t fw_connection, int pref_only, int pref_ipv6) |
| int | fascist_firewall_allows_rs (const routerstatus_t *rs, firewall_connection_t fw_connection, int pref_only) |
| int | fascist_firewall_allows_node (const node_t *node, firewall_connection_t fw_connection, int pref_only) |
| int | fascist_firewall_allows_dir_server (const dir_server_t *ds, firewall_connection_t fw_connection, int pref_only) |
| void | fascist_firewall_choose_address_rs (const routerstatus_t *rs, firewall_connection_t fw_connection, int pref_only, tor_addr_port_t *ap) |
| void | fascist_firewall_choose_address_node (const node_t *node, firewall_connection_t fw_connection, int pref_only, tor_addr_port_t *ap) |
| void | fascist_firewall_choose_address_dir_server (const dir_server_t *ds, firewall_connection_t fw_connection, int pref_only, tor_addr_port_t *ap) |
| int | dir_policy_permits_address (const tor_addr_t *addr) |
| int | socks_policy_permits_address (const tor_addr_t *addr) |
| int | authdir_policy_permits_address (uint32_t addr, uint16_t port) |
| int | authdir_policy_valid_address (uint32_t addr, uint16_t port) |
| int | authdir_policy_badexit_address (uint32_t addr, uint16_t port) |
| int | validate_addr_policies (const or_options_t *options, char **msg) |
| void | policy_expand_private (smartlist_t **policy) |
| void | policy_expand_unspec (smartlist_t **policy) |
| int | policies_parse_from_options (const or_options_t *options) |
| addr_policy_t * | addr_policy_get_canonical_entry (addr_policy_t *ent) |
| int | addr_policies_eq (const smartlist_t *a, const smartlist_t *b) |
| MOCK_DECL (addr_policy_result_t, compare_tor_addr_to_addr_policy,(const tor_addr_t *addr, uint16_t port, const smartlist_t *policy)) | |
| addr_policy_result_t | compare_tor_addr_to_node_policy (const tor_addr_t *addr, uint16_t port, const node_t *node) |
| int | policies_parse_exit_policy_from_options (const or_options_t *or_options, uint32_t local_address, const tor_addr_t *ipv6_local_address, smartlist_t **result) |
| int | policies_parse_exit_policy (config_line_t *cfg, smartlist_t **dest, exit_policy_parser_cfg_t options, const smartlist_t *configured_addresses) |
| void | policies_parse_exit_policy_reject_private (smartlist_t **dest, int ipv6_exit, const smartlist_t *configured_addresses, int reject_interface_addresses, int reject_configured_port_addresses) |
| void | policies_exit_policy_append_reject_star (smartlist_t **dest) |
| void | addr_policy_append_reject_addr (smartlist_t **dest, const tor_addr_t *addr) |
| void | addr_policy_append_reject_addr_list (smartlist_t **dest, const smartlist_t *addrs) |
| void | policies_set_node_exitpolicy_to_reject_all (node_t *exitrouter) |
| int | exit_policy_is_general_exit (smartlist_t *policy) |
| int | policy_is_reject_star (const smartlist_t *policy, sa_family_t family, int reject_by_default) |
| char * | policy_dump_to_string (const smartlist_t *policy_list, int include_ipv4, int include_ipv6) |
| int | getinfo_helper_policies (control_connection_t *conn, const char *question, char **answer, const char **errmsg) |
| int | policy_write_item (char *buf, size_t buflen, const addr_policy_t *item, int format_for_desc) |
| void | addr_policy_list_free_ (smartlist_t *p) |
| void | addr_policy_free_ (addr_policy_t *p) |
| void | policies_free_all (void) |
| char * | policy_summarize (smartlist_t *policy, sa_family_t family) |
| short_policy_t * | parse_short_policy (const char *summary) |
| char * | write_short_policy (const short_policy_t *policy) |
| void | short_policy_free_ (short_policy_t *policy) |
| int | short_policy_is_reject_star (const short_policy_t *policy) |
| addr_policy_result_t | compare_tor_addr_to_short_policy (const tor_addr_t *addr, uint16_t port, const short_policy_t *policy) |
Detailed Description
Header file for policies.c.
Function Documentation
◆ addr_policies_eq()
| int addr_policies_eq | ( | const smartlist_t * | a, |
| const smartlist_t * | b | ||
| ) |
As single_addr_policy_eq, but compare every element of two policies.

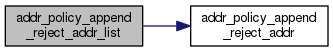
◆ addr_policy_append_reject_addr()
| void addr_policy_append_reject_addr | ( | smartlist_t ** | dest, |
| const tor_addr_t * | addr | ||
| ) |
Add "reject <b>addr</b>:*" to dest, creating the list as needed.
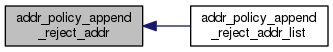
◆ addr_policy_append_reject_addr_list()
| void addr_policy_append_reject_addr_list | ( | smartlist_t ** | dest, |
| const smartlist_t * | addrs | ||
| ) |
Add "reject addr:*" to dest, for each addr in addrs, creating the list as needed.
◆ addr_policy_free_()
| void addr_policy_free_ | ( | addr_policy_t * | p | ) |
Release all storage held by p.
◆ addr_policy_list_free_()
| void addr_policy_list_free_ | ( | smartlist_t * | lst | ) |
Release all storage held by p.
◆ authdir_policy_badexit_address()
| int authdir_policy_badexit_address | ( | uint32_t | addr, |
| uint16_t | port | ||
| ) |
Return 1 if addr:port should be marked as a bad exit, based on authdir_badexit_policy. Else return 0.
◆ authdir_policy_permits_address()
| int authdir_policy_permits_address | ( | uint32_t | addr, |
| uint16_t | port | ||
| ) |
Return 1 if addr:port is permitted to publish to our directory, based on authdir_reject_policy. Else return 0.
◆ authdir_policy_valid_address()
| int authdir_policy_valid_address | ( | uint32_t | addr, |
| uint16_t | port | ||
| ) |
Return 1 if addr:port is considered valid in our directory, based on authdir_invalid_policy. Else return 0.
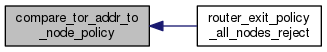
◆ compare_tor_addr_to_node_policy()
| addr_policy_result_t compare_tor_addr_to_node_policy | ( | const tor_addr_t * | addr, |
| uint16_t | port, | ||
| const node_t * | node | ||
| ) |
Decide whether addr:port is probably or definitely accepted or rejected by node. See compare_tor_addr_to_addr_policy for details on addr/port interpretation.
◆ compare_tor_addr_to_short_policy()
| addr_policy_result_t compare_tor_addr_to_short_policy | ( | const tor_addr_t * | addr, |
| uint16_t | port, | ||
| const short_policy_t * | policy | ||
| ) |
See whether the addr:port address is likely to be accepted or rejected by the summarized policy policy. Return values are as for compare_tor_addr_to_addr_policy. Unlike the regular addr_policy functions, requires the port be specified.
◆ dir_policy_permits_address()
| int dir_policy_permits_address | ( | const tor_addr_t * | addr | ) |
Return 1 if addr is permitted to connect to our dir port, based on dir_policy. Else return 0.
◆ exit_policy_is_general_exit()
| int exit_policy_is_general_exit | ( | smartlist_t * | policy | ) |
Return true iff ri is "useful as an exit node", meaning it allows exit to at least one /8 address space for each of ports 80 and 443.
◆ fascist_firewall_allows_address_addr()
| int fascist_firewall_allows_address_addr | ( | const tor_addr_t * | addr, |
| uint16_t | port, | ||
| firewall_connection_t | fw_connection, | ||
| int | pref_only, | ||
| int | pref_ipv6 | ||
| ) |
Return true iff we think our firewall will let us make a connection to addr:port. Uses ReachableORAddresses or ReachableDirAddresses based on fw_connection. If pref_only is true, return true if addr is in the client's preferred address family, which is IPv6 if pref_ipv6 is true, and IPv4 otherwise. If pref_only is false, ignore pref_ipv6, and return true if addr is allowed.
◆ fascist_firewall_allows_dir_server()
| int fascist_firewall_allows_dir_server | ( | const dir_server_t * | ds, |
| firewall_connection_t | fw_connection, | ||
| int | pref_only | ||
| ) |
◆ fascist_firewall_allows_node()
| int fascist_firewall_allows_node | ( | const node_t * | node, |
| firewall_connection_t | fw_connection, | ||
| int | pref_only | ||
| ) |
Like fascist_firewall_allows_base(), but takes node, and looks up pref_ipv6 from node_ipv6_or/dir_preferred().
◆ fascist_firewall_allows_rs()
| int fascist_firewall_allows_rs | ( | const routerstatus_t * | rs, |
| firewall_connection_t | fw_connection, | ||
| int | pref_only | ||
| ) |
Like fascist_firewall_allows_base(), but takes rs. When rs is a fake_status from a dir_server_t, it can have a reachable address, even when the corresponding node does not. nodes can be missing addresses when there's no consensus (IPv4 and IPv6), or when there is a microdescriptor consensus, but no microdescriptors (microdescriptors have IPv6, the microdesc consensus does not).

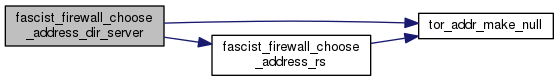
◆ fascist_firewall_choose_address_dir_server()
| void fascist_firewall_choose_address_dir_server | ( | const dir_server_t * | ds, |
| firewall_connection_t | fw_connection, | ||
| int | pref_only, | ||
| tor_addr_port_t * | ap | ||
| ) |
◆ fascist_firewall_choose_address_node()
| void fascist_firewall_choose_address_node | ( | const node_t * | node, |
| firewall_connection_t | fw_connection, | ||
| int | pref_only, | ||
| tor_addr_port_t * | ap | ||
| ) |
Like fascist_firewall_choose_address_base(), but takes node, and looks up the node's IPv6 preference rather than taking an argument for pref_ipv6.
◆ fascist_firewall_choose_address_rs()
| void fascist_firewall_choose_address_rs | ( | const routerstatus_t * | rs, |
| firewall_connection_t | fw_connection, | ||
| int | pref_only, | ||
| tor_addr_port_t * | ap | ||
| ) |
Like fascist_firewall_choose_address_base(), but takes rs. Consults the corresponding node, then falls back to rs if node is NULL. This should only happen when there's no valid consensus, and rs doesn't correspond to a bridge client's bridge.
◆ fascist_firewall_prefer_ipv6_dirport()
| int fascist_firewall_prefer_ipv6_dirport | ( | const or_options_t * | options | ) |
Do we prefer to connect to IPv6 DirPorts?
(node_ipv6_dir_preferred() doesn't support bridge client per-node IPv6 preferences. There's no reason to use it instead of this function.)
◆ fascist_firewall_prefer_ipv6_orport()
| int fascist_firewall_prefer_ipv6_orport | ( | const or_options_t * | options | ) |
Do we prefer to connect to IPv6 ORPorts? Use node_ipv6_or_preferred() whenever possible: it supports bridge client per-node IPv6 preferences.
◆ fascist_firewall_use_ipv6()
| int fascist_firewall_use_ipv6 | ( | const or_options_t * | options | ) |
Is this client configured to use IPv6? Returns true if the client might use IPv6 for some of its connections (including dual-stack and IPv6-only clients), and false if it will never use IPv6 for any connections. Use node_ipv6_or/dir_preferred() when checking a specific node and OR/Dir port: it supports bridge client per-node IPv6 preferences.
◆ firewall_is_fascist_dir()
| int firewall_is_fascist_dir | ( | void | ) |
Return true iff the firewall options, including ClientUseIPv4 0 and ClientUseIPv6 0, might block any Dir address:port combination. Address preferences may still change which address is selected even if this function returns false.
◆ firewall_is_fascist_or()
| int firewall_is_fascist_or | ( | void | ) |
Return true iff the firewall options, including ClientUseIPv4 0 and ClientUseIPv6 0, might block any OR address:port combination. Address preferences may still change which address is selected even if this function returns false.
◆ getinfo_helper_policies()
| int getinfo_helper_policies | ( | control_connection_t * | conn, |
| const char * | question, | ||
| char ** | answer, | ||
| const char ** | errmsg | ||
| ) |
Implementation for GETINFO control command: knows the answer for questions about "exit-policy/..."
◆ parse_short_policy()
| short_policy_t* parse_short_policy | ( | const char * | summary | ) |
Convert a summarized policy string into a short_policy_t. Return NULL if the string is not well-formed.
◆ policies_exit_policy_append_reject_star()
| void policies_exit_policy_append_reject_star | ( | smartlist_t ** | dest | ) |
Add "reject *:*" to the end of the policy in *dest, allocating *dest as needed.
◆ policies_free_all()
| void policies_free_all | ( | void | ) |
Release all storage held by policy variables.
◆ policies_parse_exit_policy()
| int policies_parse_exit_policy | ( | config_line_t * | cfg, |
| smartlist_t ** | dest, | ||
| exit_policy_parser_cfg_t | options, | ||
| const smartlist_t * | configured_addresses | ||
| ) |
Parse exit policy in cfg into dest smartlist.
Prepend an entry that rejects all IPv6 destinations unless EXIT_POLICY_IPV6_ENABLED bit is set in options bitmask.
If EXIT_POLICY_REJECT_PRIVATE bit is set in options:
- prepend an entry that rejects all destinations in all netblocks reserved for private use.
- prepend entries that reject the advertised relay addresses in configured_addresses If EXIT_POLICY_REJECT_LOCAL_INTERFACES bit is set in options:
- prepend entries that reject publicly routable addresses on this exit relay by calling policies_parse_exit_policy_internal
- prepend entries that reject the outbound bind addresses in configured_addresses
- prepend entries that reject all configured port addresses
If EXIT_POLICY_ADD_DEFAULT bit is set in options, append default exit policy entries to result smartlist.
◆ policies_parse_exit_policy_from_options()
| int policies_parse_exit_policy_from_options | ( | const or_options_t * | or_options, |
| uint32_t | local_address, | ||
| const tor_addr_t * | ipv6_local_address, | ||
| smartlist_t ** | result | ||
| ) |
Parse ExitPolicy member of or_options into result smartlist. If or_options->IPv6Exit is false, prepend an entry that rejects all IPv6 destinations.
If or_options->ExitPolicyRejectPrivate is true:
- prepend an entry that rejects all destinations in all netblocks reserved for private use.
- if local_address is non-zero, treat it as a host-order IPv4 address, and add it to the list of configured addresses.
- if ipv6_local_address is non-NULL, and not the null tor_addr_t, add it to the list of configured addresses. If or_options->ExitPolicyRejectLocalInterfaces is true:
- if or_options->OutboundBindAddresses[][0] (=IPv4) is not the null tor_addr_t, add it to the list of configured addresses.
- if or_options->OutboundBindAddresses[][1] (=IPv6) is not the null tor_addr_t, add it to the list of configured addresses.
If or_options->BridgeRelay is false, append entries of default Tor exit policy into result smartlist.
If or_options->ExitRelay is false, then make our exit policy into "reject *:*" regardless.

◆ policies_parse_exit_policy_reject_private()
| void policies_parse_exit_policy_reject_private | ( | smartlist_t ** | dest, |
| int | ipv6_exit, | ||
| const smartlist_t * | configured_addresses, | ||
| int | reject_interface_addresses, | ||
| int | reject_configured_port_addresses | ||
| ) |
Reject private helper for policies_parse_exit_policy_internal: rejects publicly routable addresses on this exit relay.
Add reject entries to the linked list *dest:
- if configured_addresses is non-NULL, add entries that reject each tor_addr_t in the list as a destination.
- if reject_interface_addresses is true, add entries that reject each public IPv4 and IPv6 address of each interface on this machine.
- if reject_configured_port_addresses is true, add entries that reject each IPv4 and IPv6 address configured for a port.
IPv6 entries are only added if ipv6_exit is true. (All IPv6 addresses are already blocked by policies_parse_exit_policy_internal if ipv6_exit is false.)
The list in dest is created as needed.
◆ policies_parse_from_options()
| int policies_parse_from_options | ( | const or_options_t * | options | ) |
Set all policies based on options, which should have been validated first by validate_addr_policies.
◆ policies_set_node_exitpolicy_to_reject_all()
| void policies_set_node_exitpolicy_to_reject_all | ( | node_t * | node | ) |
Replace the exit policy of node with reject *:*
◆ policy_dump_to_string()
| char* policy_dump_to_string | ( | const smartlist_t * | policy_list, |
| int | include_ipv4, | ||
| int | include_ipv6 | ||
| ) |
Given policy_list, a list of addr_policy_t, produce a string representation of the list. If include_ipv4 is true, include IPv4 entries. If include_ipv6 is true, include IPv6 entries.
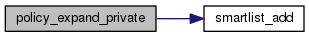
◆ policy_expand_private()
| void policy_expand_private | ( | smartlist_t ** | policy | ) |
Replace all "private" entries in *policy with their expanded equivalents.
◆ policy_expand_unspec()
| void policy_expand_unspec | ( | smartlist_t ** | policy | ) |
Expand each of the AF_UNSPEC elements in *policy (which indicate protocol-neutral wildcards) into a pair of wildcard elements: one IPv4- specific and one IPv6-specific.
◆ policy_is_reject_star()
| int policy_is_reject_star | ( | const smartlist_t * | policy, |
| sa_family_t | family, | ||
| int | default_reject | ||
| ) |
Return false if policy might permit access to some addr:port; otherwise if we are certain it rejects everything, return true. If no part of policy matches, return default_reject. NULL policies are allowed, and treated as empty.
◆ policy_summarize()
| char* policy_summarize | ( | smartlist_t * | policy, |
| sa_family_t | family | ||
| ) |
Create a string representing a summary for an exit policy. The summary will either be an "accept" plus a comma-separated list of port ranges or a "reject" plus port-ranges, depending on which is shorter.
If no exits are allowed at all then "reject 1-65535" is returned. If no ports are blocked instead of "reject " we return "accept 1-65535". (These are an exception to the shorter-representation-wins rule).

◆ policy_write_item()
| int policy_write_item | ( | char * | buf, |
| size_t | buflen, | ||
| const addr_policy_t * | policy, | ||
| int | format_for_desc | ||
| ) |
Write a single address policy to the buf_len byte buffer at buf. Return the number of characters written, or -1 on failure.
◆ short_policy_free_()
| void short_policy_free_ | ( | short_policy_t * | policy | ) |
Release all storage held in policy.
◆ short_policy_is_reject_star()
| int short_policy_is_reject_star | ( | const short_policy_t * | policy | ) |
Return true iff policy seems reject all ports

◆ socks_policy_permits_address()
| int socks_policy_permits_address | ( | const tor_addr_t * | addr | ) |
Return 1 if addr is permitted to connect to our socks port, based on socks_policy. Else return 0.
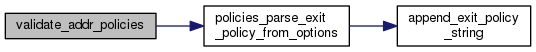
◆ validate_addr_policies()
| int validate_addr_policies | ( | const or_options_t * | options, |
| char ** | msg | ||
| ) |
Config helper: If there's any problem with the policy configuration options in options, return -1 and set msg to a newly allocated description of the error. Else return 0.
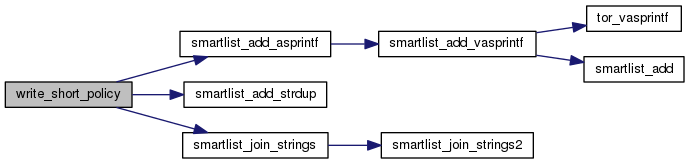
◆ write_short_policy()
| char* write_short_policy | ( | const short_policy_t * | policy | ) |
Write policy back out into a string.


 1.8.13
1.8.13