Functions to handle OR connections, TLS handshaking, and cells on the network. More...
#include "or.h"#include "bridges.h"#include "buffers.h"#include "channel.h"#include "channeltls.h"#include "circuitbuild.h"#include "circuitlist.h"#include "circuitstats.h"#include "command.h"#include "config.h"#include "connection.h"#include "connection_or.h"#include "control.h"#include "crypto_rand.h"#include "crypto_util.h"#include "dirserv.h"#include "entrynodes.h"#include "geoip.h"#include "main.h"#include "link_handshake.h"#include "microdesc.h"#include "networkstatus.h"#include "nodelist.h"#include "proto_cell.h"#include "reasons.h"#include "relay.h"#include "rephist.h"#include "router.h"#include "routerkeys.h"#include "routerlist.h"#include "ext_orport.h"#include "scheduler.h"#include "torcert.h"#include "channelpadding.h"
Data Structures | |
| struct | broken_state_count_t |
| struct | or_connect_failure_entry_t |
Macros | |
| #define | TOR_CHANNEL_INTERNAL_ |
| #define | CONNECTION_OR_PRIVATE |
| #define | MAX_REASONS_TO_REPORT 10 |
| #define | MAX_OR_INBUF_WHEN_NONOPEN 0 |
| #define | TIME_BEFORE_OR_CONN_IS_TOO_OLD (60*60*24*7) |
| #define | OR_CONNECT_FAILURE_LIFETIME 60 |
| #define | OR_CONNECT_FAILURE_CLEANUP_INTERVAL 60 |
| #define | certs_cell_ed25519_disabled_for_testing 0 |
Typedefs | |
| typedef struct broken_state_count_t | broken_state_count_t |
| typedef struct or_connect_failure_entry_t | or_connect_failure_entry_t |
Detailed Description
Functions to handle OR connections, TLS handshaking, and cells on the network.
An or_connection_t is a subtype of connection_t (as implemented in connection.c) that uses a TLS connection to send and receive cells on the Tor network. (By sending and receiving cells connection_or.c, it cooperates with channeltls.c to implement a the channel interface of channel.c.)
Every OR connection has an underlying tortls_t object (as implemented in tortls.c) which it uses as its TLS stream. It is responsible for sending and receiving cells over that TLS.
This module also implements the client side of the v3 Tor link handshake,
Macro Definition Documentation
◆ MAX_REASONS_TO_REPORT
| #define MAX_REASONS_TO_REPORT 10 |
Upper limit on the number of different states to report for connection failure.
◆ TIME_BEFORE_OR_CONN_IS_TOO_OLD
| #define TIME_BEFORE_OR_CONN_IS_TOO_OLD (60*60*24*7) |
How old do we let a connection to an OR get before deciding it's too old for new circuits?
Typedef Documentation
◆ broken_state_count_t
| typedef struct broken_state_count_t broken_state_count_t |
Helper type used to sort connection states and find the most frequent.
Function Documentation
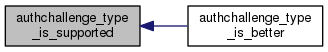
◆ authchallenge_type_is_better()
| int authchallenge_type_is_better | ( | uint16_t | challenge_type_a, |
| uint16_t | challenge_type_b | ||
| ) |
Return true iff challenge_type_a is one that we would rather use than challenge_type_b.
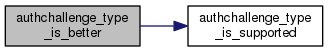
◆ authchallenge_type_is_supported()
| int authchallenge_type_is_supported | ( | uint16_t | challenge_type | ) |
Return true iff challenge_type is an AUTHCHALLENGE type that we can send and receive.
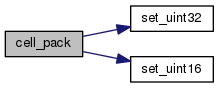
◆ cell_pack()
| void cell_pack | ( | packed_cell_t * | dst, |
| const cell_t * | src, | ||
| int | wide_circ_ids | ||
| ) |
Pack the cell_t host-order structure src into network-order in the buffer dest. See tor-spec.txt for details about the wire format.
Note that this function doesn't touch dst->next: the caller should set it or clear it as appropriate.
◆ clear_broken_connection_map()
| void clear_broken_connection_map | ( | int | stop_recording | ) |
Forget all recorded states for failed connections. If stop_recording is true, don't record any more.
◆ connection_init_or_handshake_state()
| int connection_init_or_handshake_state | ( | or_connection_t * | conn, |
| int | started_here | ||
| ) |
Allocate a new connection handshake state for the connection conn. Return 0 on success, -1 on failure.
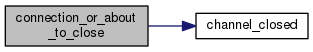
◆ connection_or_about_to_close()
| void connection_or_about_to_close | ( | or_connection_t * | or_conn | ) |
Called when we're about to finally unlink and free an OR connection: perform necessary accounting and cleanup
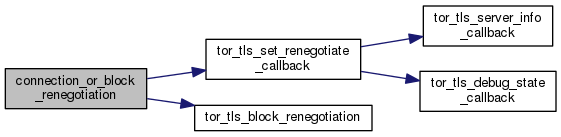
◆ connection_or_block_renegotiation()
| void connection_or_block_renegotiation | ( | or_connection_t * | conn | ) |
Block all future attempts to renegotiate on 'conn'
◆ connection_or_clear_ext_or_id_map()
| void connection_or_clear_ext_or_id_map | ( | void | ) |
Deallocate the global Extended ORPort identifier list
◆ connection_or_clear_identity()
| void connection_or_clear_identity | ( | or_connection_t * | conn | ) |
Clear clear conn->identity_digest and update other data structures as appropriate.
◆ connection_or_clear_identity_map()
| void connection_or_clear_identity_map | ( | void | ) |
Clear all identities in OR conns.
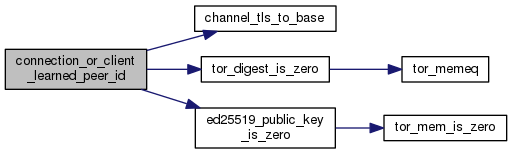
◆ connection_or_client_learned_peer_id()
| int connection_or_client_learned_peer_id | ( | or_connection_t * | conn, |
| const uint8_t * | rsa_peer_id, | ||
| const ed25519_public_key_t * | ed_peer_id | ||
| ) |
Called when we (as a connection initiator) have definitively, authenticatedly, learned that ID of the Tor instance on the other side of conn is rsa_peer_id and optionally ed_peer_id. For v1 and v2 handshakes, this is right after we get a certificate chain in a TLS handshake or renegotiation. For v3+ handshakes, this is right after we get a certificate chain in a CERTS cell.
If we did not know the ID before, record the one we got.
If we wanted an ID, but we didn't get the one we expected, log a message and return -1. On relays:
- log a protocol warning whenever the fingerprints don't match; On clients:
- if a relay's fingerprint doesn't match, log a warning;
- if we don't have updated relay fingerprints from a recent consensus, and a fallback directory mirror's hard-coded fingerprint has changed, log an info explaining that we will try another fallback.
If we're testing reachability, remember what we learned.
Return 0 on success, -1 on failure.
◆ connection_or_client_used()
| time_t connection_or_client_used | ( | or_connection_t * | conn | ) |
Return when we last used this channel for client activity (origin circuits). This is called from connection.c, since client_used is now one of the timestamps in channel_t

◆ connection_or_close_normally()
| void connection_or_close_normally | ( | or_connection_t * | orconn, |
| int | flush | ||
| ) |
Mark orconn for close and transition the associated channel, if any, to the closing state.
It's safe to call this and connection_or_close_for_error() any time, and channel layer will treat it as a connection closing for reasons outside its control, like the remote end closing it. It can also be a local reason that's specific to connection_t/or_connection_t rather than the channel mechanism, such as expiration of old connections in run_connection_housekeeping(). If you want to close a channel_t from somewhere that logically works in terms of generic channels rather than connections, use channel_mark_for_close(); see also the comment on that function in channel.c.
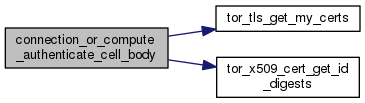
◆ connection_or_compute_authenticate_cell_body()
| var_cell_t* connection_or_compute_authenticate_cell_body | ( | or_connection_t * | conn, |
| const int | authtype, | ||
| crypto_pk_t * | signing_key, | ||
| const ed25519_keypair_t * | ed_signing_key, | ||
| int | server | ||
| ) |
Compute the main body of an AUTHENTICATE cell that a client can use to authenticate itself on a v3 handshake for conn. Return it in a var_cell_t.
If server is true, only calculate the first V3_AUTH_FIXED_PART_LEN bytes – the part of the authenticator that's determined by the rest of the handshake, and which match the provided value exactly.
If server is false and signing_key is NULL, calculate the first V3_AUTH_BODY_LEN bytes of the authenticator (that is, everything that should be signed), but don't actually sign it.
If server is false and signing_key is provided, calculate the entire authenticator, signed with signing_key.
Return the length of the cell body on success, and -1 on failure.
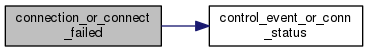
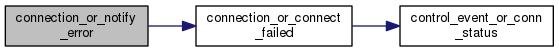
◆ connection_or_connect_failed()
| void connection_or_connect_failed | ( | or_connection_t * | conn, |
| int | reason, | ||
| const char * | msg | ||
| ) |
conn is in the 'connecting' state, and it failed to complete a TCP connection. Send notifications appropriately.
reason specifies the or_conn_end_reason for the failure; msg specifies the strerror-style error message.
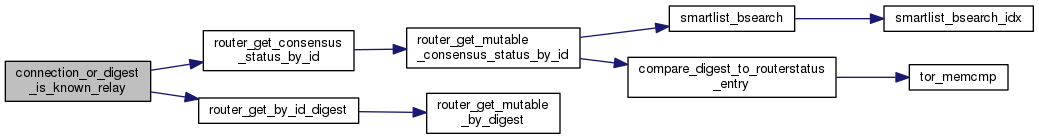
◆ connection_or_digest_is_known_relay()
| int connection_or_digest_is_known_relay | ( | const char * | id_digest | ) |
Return 1 if identity digest id_digest is known to be a currently or recently running relay. Otherwise return 0.
◆ connection_or_finished_connecting()
| int connection_or_finished_connecting | ( | or_connection_t * | or_conn | ) |
Connected handler for OR connections: begin the TLS handshake.
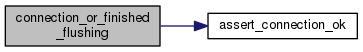
◆ connection_or_finished_flushing()
| int connection_or_finished_flushing | ( | or_connection_t * | conn | ) |
Connection conn has finished writing and has no bytes left on its outbuf.
Otherwise it's in state "open": stop writing and return.
If conn is broken, mark it for close and return -1, else return 0.
◆ connection_or_flushed_some()
| int connection_or_flushed_some | ( | or_connection_t * | conn | ) |
Called whenever we have flushed some data on an or_conn: add more data from active circuits.

◆ connection_or_get_by_ext_or_id()
| or_connection_t* connection_or_get_by_ext_or_id | ( | const char * | id | ) |
Return the connection whose ext_or_id is id. Return NULL if no such connection is found.
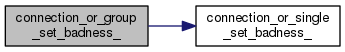
◆ connection_or_group_set_badness_()
| void connection_or_group_set_badness_ | ( | smartlist_t * | group, |
| int | force | ||
| ) |
Given a list of all the or_connections with a given identity, set elements of that list as is_bad_for_new_circs as appropriate. Helper for connection_or_set_bad_connections().
Specifically, we set the is_bad_for_new_circs flag on:
- all connections if force is true.
- all connections that are too old.
- all open non-canonical connections for which a canonical connection exists to the same router.
- all open canonical connections for which a 'better' canonical connection exists to the same router.
- all open non-canonical connections for which a 'better' non-canonical connection exists to the same router at the same address.
See channel_is_better() in channel.c for our idea of what makes one OR connection better than another.
◆ connection_or_init_conn_from_address()
| void connection_or_init_conn_from_address | ( | or_connection_t * | conn, |
| const tor_addr_t * | addr, | ||
| uint16_t | port, | ||
| const char * | id_digest, | ||
| const ed25519_public_key_t * | ed_id, | ||
| int | started_here | ||
| ) |
If we don't necessarily know the router we're connecting to, but we have an addr/port/id_digest, then fill in as much as we can. Start by checking to see if this describes a router we know. started_here is 1 if we are the initiator of conn and 0 if it's an incoming connection.
◆ connection_or_nonopen_was_started_here()
| int connection_or_nonopen_was_started_here | ( | or_connection_t * | conn | ) |
Return 1 if we initiated this connection, or 0 if it started out as an incoming connection.

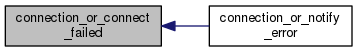
◆ connection_or_notify_error()
| void connection_or_notify_error | ( | or_connection_t * | conn, |
| int | reason, | ||
| const char * | msg | ||
| ) |
conn got an error in connection_handle_read_impl() or connection_handle_write_impl() and is going to die soon.
reason specifies the or_conn_end_reason for the failure; msg specifies the strerror-style error message.
◆ connection_or_num_cells_writeable()
| ssize_t connection_or_num_cells_writeable | ( | or_connection_t * | conn | ) |
This is for channeltls.c to ask how many cells we could accept if they were available.
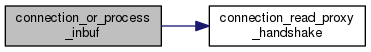
◆ connection_or_process_inbuf()
| int connection_or_process_inbuf | ( | or_connection_t * | conn | ) |
Handle any new bytes that have come in on connection conn. If conn is in 'open' state, hand it to connection_or_process_cells_from_inbuf() (else do nothing).
Don't let the inbuf of a nonopen OR connection grow beyond this many bytes: it's either a broken client, a non-Tor client, or a DOS attempt.
◆ connection_or_reached_eof()
| int connection_or_reached_eof | ( | or_connection_t * | conn | ) |
We've received an EOF from conn. Mark it for close and return.
◆ connection_or_remove_from_ext_or_id_map()
| void connection_or_remove_from_ext_or_id_map | ( | or_connection_t * | conn | ) |
Remove the Extended ORPort identifier of conn from the global identifier list. Also, clear the identifier from the connection itself.
◆ connection_or_report_broken_states()
| void connection_or_report_broken_states | ( | int | severity, |
| int | domain | ||
| ) |
Report a list of the top states for failed OR connections at log level severity, in log domain domain.
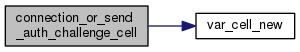
◆ connection_or_send_auth_challenge_cell()
| int connection_or_send_auth_challenge_cell | ( | or_connection_t * | conn | ) |
Send an AUTH_CHALLENGE cell on the connection conn. Return 0 on success, -1 on failure.
◆ connection_or_send_certs_cell()
| int connection_or_send_certs_cell | ( | or_connection_t * | conn | ) |
Send a CERTS cell on the connection conn. Return 0 on success, -1 on failure.
◆ connection_or_send_versions()
| int connection_or_send_versions | ( | or_connection_t * | conn, |
| int | v3_plus | ||
| ) |
Send a VERSIONS cell on conn, telling the other host about the link protocol versions that this Tor can support.
If v3_plus, this is part of a V3 protocol handshake, so only allow protocol version v3 or later. If not v3_plus, this is not part of a v3 protocol handshake, so don't allow protocol v3 or later.
◆ connection_or_set_ext_or_identifier()
| void connection_or_set_ext_or_identifier | ( | or_connection_t * | conn | ) |
Creates an Extended ORPort identifier for conn and deposits it into the global list of identifiers.
◆ connection_or_set_state_open()
| int connection_or_set_state_open | ( | or_connection_t * | conn | ) |
Set conn's state to OR_CONN_STATE_OPEN, and tell other subsystems as appropriate. Called when we are done with all TLS and OR handshaking.
◆ connection_or_single_set_badness_()
| int connection_or_single_set_badness_ | ( | time_t | now, |
| or_connection_t * | or_conn, | ||
| int | force | ||
| ) |
Expire an or_connection if it is too old. Helper for connection_or_group_set_badness_ and fast path for channel_rsa_id_group_set_badness.
Returns 1 if the connection was already expired, else 0.
◆ connection_or_update_token_buckets()
| void connection_or_update_token_buckets | ( | smartlist_t * | conns, |
| const or_options_t * | options | ||
| ) |
Either our set of relays or our per-conn rate limits have changed. Go through all the OR connections and update their token buckets to make sure they don't exceed their maximum values.
◆ connection_or_write_cell_to_buf()
| void connection_or_write_cell_to_buf | ( | const cell_t * | cell, |
| or_connection_t * | conn | ||
| ) |
Pack cell into wire-format, and write it onto conn's outbuf. For cells that use or affect a circuit, this should only be called by connection_or_flush_from_first_active_circuit().
◆ connection_tls_continue_handshake()
| int connection_tls_continue_handshake | ( | or_connection_t * | conn | ) |
Move forward with the tls handshake. If it finishes, hand conn to connection_tls_finish_handshake().
Return -1 if conn is broken, else return 0.
◆ is_or_protocol_version_known()
| int is_or_protocol_version_known | ( | uint16_t | v | ) |
Return true iff v is a link protocol version that this Tor implementation believes it can support.
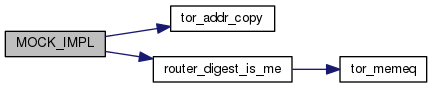
◆ MOCK_IMPL() [1/7]
| MOCK_IMPL | ( | int | , |
| connection_or_get_num_circuits | , | ||
| (or_connection_t *conn) | |||
| ) |
Return the number of circuits using an or_connection_t; this used to be an or_connection_t field, but it got moved to channel_t and we shouldn't maintain two copies.
◆ MOCK_IMPL() [2/7]
| MOCK_IMPL | ( | or_connection_t * | , |
| connection_or_connect | , | ||
| (const tor_addr_t *_addr, uint16_t port, const char *id_digest, const ed25519_public_key_t *ed_id, channel_tls_t *chan) | |||
| ) |
Launch a new OR connection to addr:port and expect to handshake with an OR with identity digest id_digest. Optionally, pass in a pointer to a channel using this connection.
If id_digest is me, do nothing. If we're already connected to it, return that connection. If the connect() is in progress, set the new conn's state to 'connecting' and return it. If connect() succeeds, call connection_tls_start_handshake() on it.
This function is called from router_retry_connections(), for ORs connecting to ORs, and circuit_establish_circuit(), for OPs connecting to ORs.
Return the launched conn, or NULL if it failed.
◆ MOCK_IMPL() [3/7]
| MOCK_IMPL | ( | void | , |
| connection_or_close_for_error | , | ||
| (or_connection_t *orconn, int flush) | |||
| ) |
Mark orconn for close and transition the associated channel, if any, to the error state.
◆ MOCK_IMPL() [4/7]
| MOCK_IMPL | ( | int | , |
| connection_tls_start_handshake | , | ||
| (or_connection_t *conn, int receiving) | |||
| ) |
Begin the tls handshake with conn. receiving is 0 if we initiated the connection, else it's 1.
Assign a new tls object to conn->tls, begin reading on conn, and pass conn to connection_tls_continue_handshake().
Return -1 if conn is broken, else return 0.

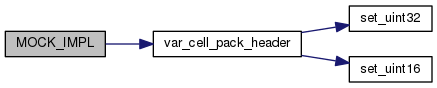
◆ MOCK_IMPL() [5/7]
| MOCK_IMPL | ( | void | , |
| connection_or_write_var_cell_to_buf | , | ||
| (const var_cell_t *cell, or_connection_t *conn) | |||
| ) |
Pack a variable-length cell into wire-format, and write it onto conn's outbuf. Right now, this DOES NOT support cells that affect a circuit.
◆ MOCK_IMPL() [6/7]
| MOCK_IMPL | ( | int | , |
| connection_or_send_netinfo | , | ||
| (or_connection_t *conn) | |||
| ) |
Send a NETINFO cell on conn, telling the other server what we know about their address, our address, and the current time.
◆ MOCK_IMPL() [7/7]
| MOCK_IMPL | ( | int | , |
| connection_or_send_authenticate_cell | , | ||
| (or_connection_t *conn, int authtype) | |||
| ) |
Send an AUTHENTICATE cell on the connection conn. Return 0 on success, -1 on failure
◆ or_handshake_state_free_()
| void or_handshake_state_free_ | ( | or_handshake_state_t * | state | ) |
Free all storage held by state.
◆ or_handshake_state_record_cell()
| void or_handshake_state_record_cell | ( | or_connection_t * | conn, |
| or_handshake_state_t * | state, | ||
| const cell_t * | cell, | ||
| int | incoming | ||
| ) |
Remember that cell has been transmitted (if incoming is false) or received (if incoming is true) during a V3 handshake using state.
(We don't record the cell, but we keep a digest of everything sent or received during the v3 handshake, and the client signs it in an authenticate cell.)
◆ or_handshake_state_record_var_cell()
| void or_handshake_state_record_var_cell | ( | or_connection_t * | conn, |
| or_handshake_state_t * | state, | ||
| const var_cell_t * | cell, | ||
| int | incoming | ||
| ) |
Remember that a variable-length cell has been transmitted (if incoming is false) or received (if incoming is true) during a V3 handshake using state.
(We don't record the cell, but we keep a digest of everything sent or received during the v3 handshake, and the client signs it in an authenticate cell.)

◆ var_cell_copy()
| var_cell_t* var_cell_copy | ( | const var_cell_t * | src | ) |
Copy a var_cell_t
◆ var_cell_free_()
| void var_cell_free_ | ( | var_cell_t * | cell | ) |
Release all space held by cell.
◆ var_cell_new()
| var_cell_t* var_cell_new | ( | uint16_t | payload_len | ) |
Allocate and return a new var_cell_t with payload_len bytes of payload space.

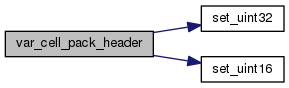
◆ var_cell_pack_header()
| int var_cell_pack_header | ( | const var_cell_t * | cell, |
| char * | hdr_out, | ||
| int | wide_circ_ids | ||
| ) |
Write the header of cell into the first VAR_CELL_MAX_HEADER_SIZE bytes of hdr_out. Returns number of bytes used.
 1.8.13
1.8.13